
The Cybersecurity & Infrastructure Security Agency (CISA) warned that phishing emails are redirecting recipients to spoofed COVID-19 loan relief pages. On August 12, CISA announced its discovery of the attack campaign in Alert (AA20-225A):
The Cybersecurity and Infrastructure Security Agency (CISA) is currently tracking an unknown malicious cyber actor who is spoofing the Small Business Administration (SBA) COVID-19 loan relief webpage via phishing emails. These emails include a malicious link to the spoofed SBA website that the cyber actor is using for malicious re-directs and credential stealing.
CISA went on to explain that individuals at multiple Federal Civilian Executive Branch and state, local, tribal and territorial government had received the attack emails. Using the subject line "SBA Application – Review and Proceed," the emails informed recipients that they could apply and/or review their application for a COVID-19 relief loan via the Small Business Association (SBA) by clicking on an embedded link. This resource redirected them to "hxxps://leanproconsulting[.]com.br/gov/covid19relief/sba.gov," a domain which resolved to the IP address 162.214.104[.]246. That domain was the home to a fake SBA loan relief login portal at the time of CISA's analysis.
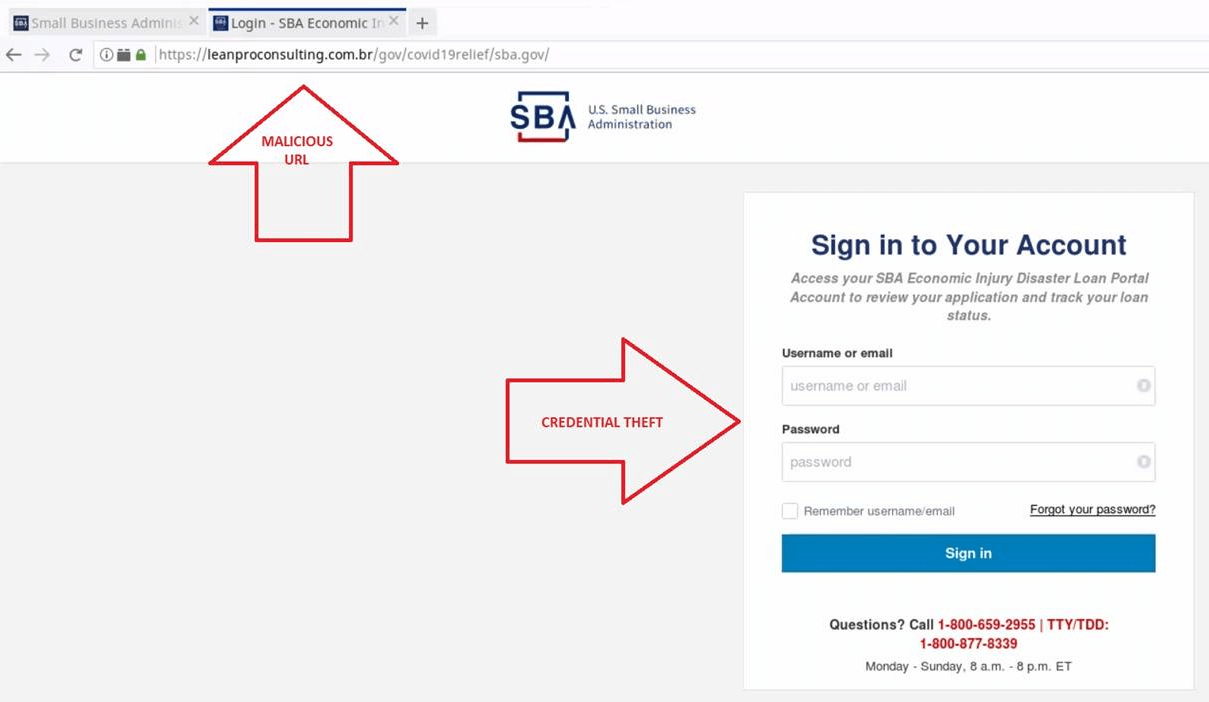
Webpage arrived at via malicious hyperlink. (Source: CISA) The attack described above wasn't the first time that scammers abused COVID-19 economic relief for nefarious purposes. Back in mid-March, malicious actors sent out scam emails informing recipients that they could collect a $1,000 economic stimulus check by providing their personal information, banking details and Social Security Numbers. This information gave attackers all they needed to perpetrate identity fraud against their victims. In response to the phishing emails it observed, CISA recommended that organizations implement banners for all emails that originate from outside their network, maintain up-to-date antivirus solutions and enforce a strong password policy. They should also consider educating their employees about some of the most common phishing campaigns and techniques that are in circulation today. They can use this resource to get started.

