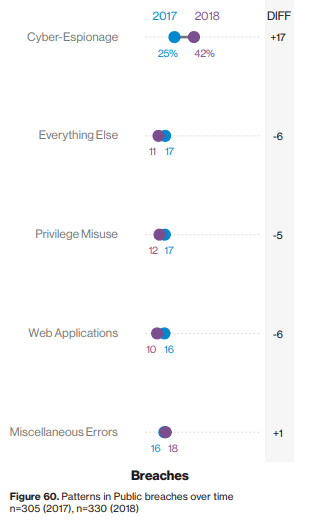
It’s been a few weeks since Verizon released the 12th edition of its Data Breach Investigations Report (DBIR). For this publication, Verizon’s researchers studied 41,686 security incidents in which a response was necessary. These analysts found that 2,013 of those incidents were data breaches in that some sort of information was actually compromised. Out of all the other sectors, public administration saw a disproportionately large share of security events during Verizon’s reporting period. Approximately 56 percent of all security incidents analyzed for the 2019 DBIR struck public organizations, for instance. The sector also accounted for about 16 percent of all publicly disclosed data breaches. A closer look at these public sector security incidents shows that digital espionage was the most prevalent attack pattern for this industry. Espionage played a pivotal role in almost half (42 percent) of data breaches reported by public organizations. That is an increase of 168 percent from just 25 percent of breaches a year earlier. Given this growth, it’s no wonder that espionage was the predominant motive in two-thirds of public sector breaches.
Source: 2019 Data Breach Investigations Report It’s also not surprising that primarily external attackers were responsible for those data breaches. 30 percent of those security incidents with confirmed data disclosure involved internal actors. 30 percent isn’t nothing, but it’s not a majority either. Meanwhile, partners were behind only one percent of these security events. It’s important to note that agencies are spending lots of money to combat the risks associated with insider threats. (The Office of the Director of National Intelligence’s creation of a government-wide insider threat program is but one example.) Some might feel this level of investment is wasted given the fact that there were fewer data breaches associated with insider threats than those resulting from external attackers. But that’s not the case. Simply, organizations need to look at the types of insider threats that exist and tailor their investments accordingly.
The Public Sector vs. the Private Sector
The findings presented above stand in stark contrast to those from private sector organizations. Indeed, digital attackers had largely financial motivations for targeting other industries. In other words, bad actors were more interested in how much they could get for selling a private organization’s stolen data than they were in learning what secrets that data could reveal. The public sector also differed from the private sector in terms of the amount of time needed to discover a data breach. Overall, data breaches affecting public organizations were 2.5 times more likely to take years for security professionals to discover than security incidents in the private sector. This time discrepancy could reflect the number of incidents which public sector organizations encountered during Verizon’s reporting period. But it could also have something to do with the tendency for public agencies’ security professionals to be overconfident in their ability to discover data breaches in a timely manner.
What Public Organizations Can Do to Defend Themselves
The findings of Verizon’s 2019 DBIR highlight how public organizations can do more to strengthen their digital security. They can do so by abiding by these following four guidelines:
- Bolster email security: Verizon found in its 2019 DBIR that email was responsible for 94 percent of all malware attacks across all sectors. Given this prevalence, organizations should invest in their user awareness training to prepare their employees to be on the lookout for phishing attacks. They should balance this focus on training with investment in email security solutions such as whitelists, as training only goes so far.
- Defend against insider threats: Similar to email security, organizations need to use training and technical controls to defend against insider threats. They can do this by specifically monitoring for unplanned changes as well as changes that aren’t part of a change management process.
- Monitor the network: Once a digital attacker successfully compromises their intended asset, they usually use a backdoor or command-and-control (C&C) server to establish communication with outside assets for the purpose of data exfiltration. Organizations should, therefore, invest in solutions that can monitor for suspicious network traffic including the exfiltration of information outside the network.
- Use controls to reduce the attack surface: Lastly, organizations should use various foundational controls to minimize their attack surface once a compromise has occurred. Specifically, they should manage their assets’ configurations, monitor for vulnerabilities (so as to prevent lateral movement) and make sure that they close their malware gaps.
To make their security efforts as successful as possible, public sector organizations should consider investing in a solution that blends these and other foundational controls together. Learn how Tripwire’s products accomplish this.

