
Security researchers detected a clever new phishing campaign that abused three enterprise cloud services in an attempt to steal victims' credentials. On July 18, Bleeping Computer revealed that the phishing campaign's attack emails claimed to originated from the domain "servicedesk.com." The computer self-help site took a closer look. In the process, it found that those responsible for the campaign had sent the email through the intermediary "cn.trackhawk.pro." This technique helped the attack emails evade detection: As Bleeping Computer noted in its analysis:
In most email spoofing scenarios, a mismatch between the “From:” email domain and the domain listed in the bottommost “Received:” header is a red flag. In this campaign, the domain “servicedesk.com” is used in the “From:” (envelope) address matches the domain listed in the last “Received:” header, making it more easily bypass spam filters.
Because "servicedesk.com" returned timeouts but "cn.trackhawk.pro" correctly responded to pings, Bleeping Computer reasoned that the authors of the campaign had likely sent out the emails through the latter domain but had injected the forged "Received: from servicedesk.com ...” header at the bottom. Each of the phishing campaign's attack emails pretended to be a notification from a help desk informing the recipient that they had undelivered messages. It then asked them to click one of two embedded buttons in order to free up space in their inboxes.
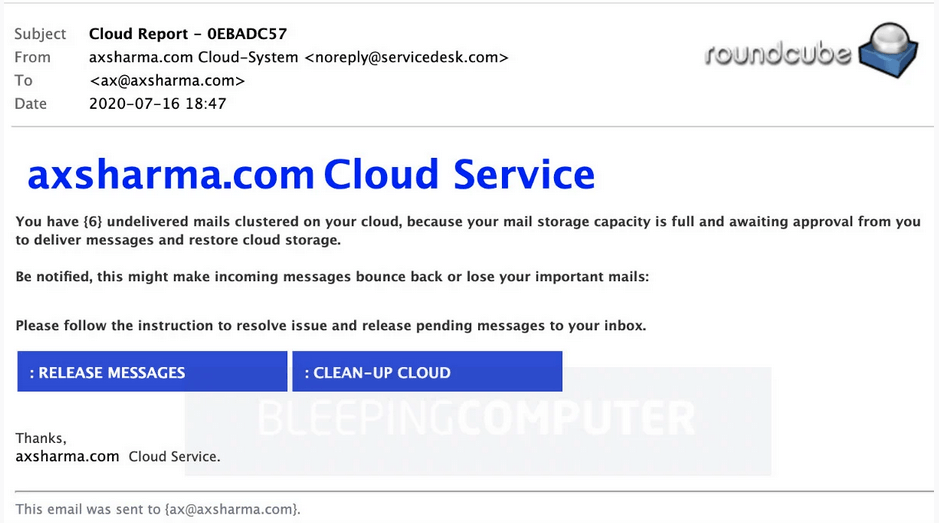
Phishing email pretending to be from an IT support desk (Source: Bleeping Computer) Either of these buttons redirected the user to a phishing site hosted on Microsoft Azure, Microsoft Dynamics or IBM Cloud. Upon receiving a set of email credentials, the phishing site redirected the user to another page that informed them that their account was in the process of updating. It then eventually redirected the user to a domain associated with their email account. The campaign described above highlights the need for organizations to defend themselves against phishing attacks. One of the ways they can do this is by training their employees to spot the latest phishing attacks that are circulating in the wild.

