
In July 2019, Capital One made news headlines not for achieving another milestone but because it had been breached. Capital One was using AWS cloud services, as many businesses are doing nowadays. The problem stemmed (in part) because Capital One had a misconfigured open-source Web Application Firewall (WAF) hosted in the cloud with Amazon Web Services (AWS). Despite the inevitable criticism, Capital One’s breach “doesn’t prove the cloud is wrong,” says Glenn O’Donnell, a Forrester VP. “What it does prove is you have to have the right controls in place from a security and governance perspective.” Before we dig into cloud security issues, let us refresh our memory.
Cloud Services
With traditional IT services, the owner is responsible for all services from networking equipment to the application itself. Cloud computing offers services such as SaaS, PaaS and IaaS to make deployment and management of computing resources more efficiently.
- Infrastructure as a service (IaaS) is a “compute” platform that provides virtualized computing resources over the internet. Examples include the following: AWS AMI, Azure Virtual Machines and GCP Compute Engine.
- Platform as a service (PaaS) are pre-build applications that enable the customer to upload their code or data and use it without building the underlying infrastructure. The hardware and software tools are delivered by a third-party provider. It is also known as Serverless Environment. Examples include AWS Lamda, GCP Code Function, AWS RDS, AWS s3, GCP BigQuery and Azure SQL Database.
- Software as a service (SaaS) is a software distribution model in which a third-party provider hosts applications and makes them available to customers over the internet. Examples include Office365, Box, G Suite, Xero, Salesforce, Imperva WAF, Akamai CDN and Azure SQL Database.
The Shared Responsibility Model
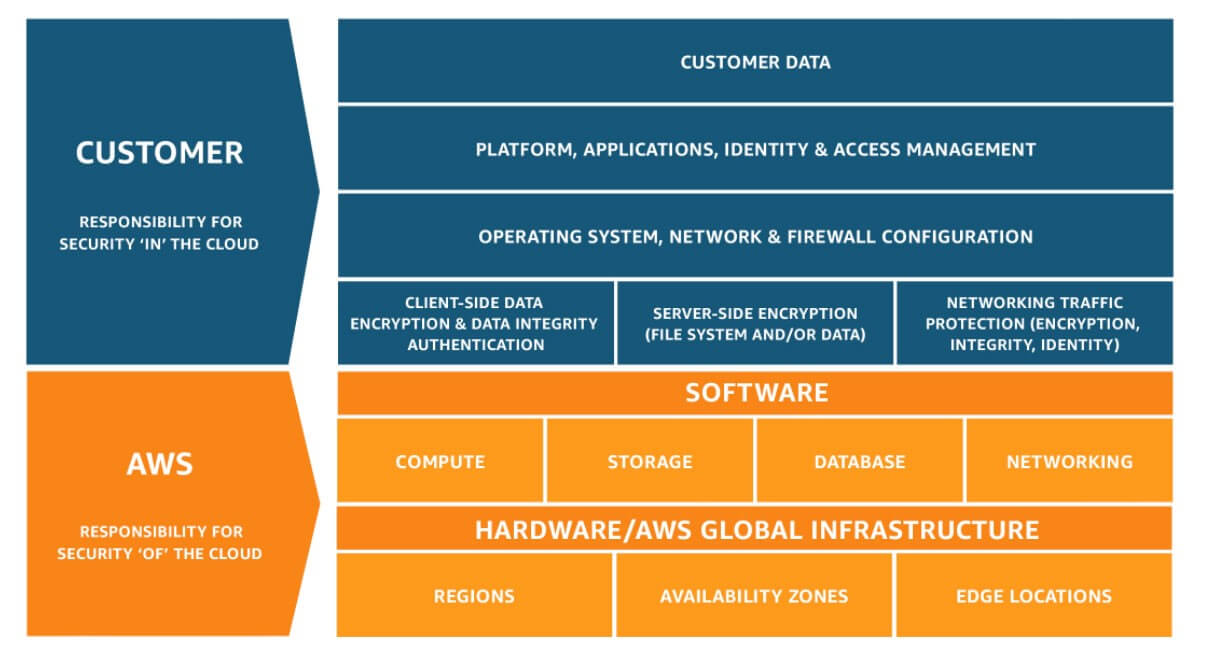
Who’s responsible for the integrity and confidentiality of the aforementioned services and the data therein? It is important to understand the shared responsibility model for both Amazon AWS and Microsoft Azure, where a great deal of misunderstanding and fog exists. Amazon AWS shared responsibility model affirms that “Security and Compliance is a shared responsibility between AWS and the customer.” Specifically, AWS is responsible for the “security of the cloud.... AWS operates, manages and controls the components from the host operating system and virtualization layer down to the physical security of the facilities in which the service operates.” On the other hand, the customer is responsible for “security in the cloud.” Per AWS,
The customer assumes responsibility and management of the guest operating system (including updates and security patches), other associated application software, as well as the configuration of the AWS, provided security group firewall. Customers should carefully consider the services they choose as their responsibilities vary depending on the services used, the integration of those services into their IT environment, and applicable laws and regulations.
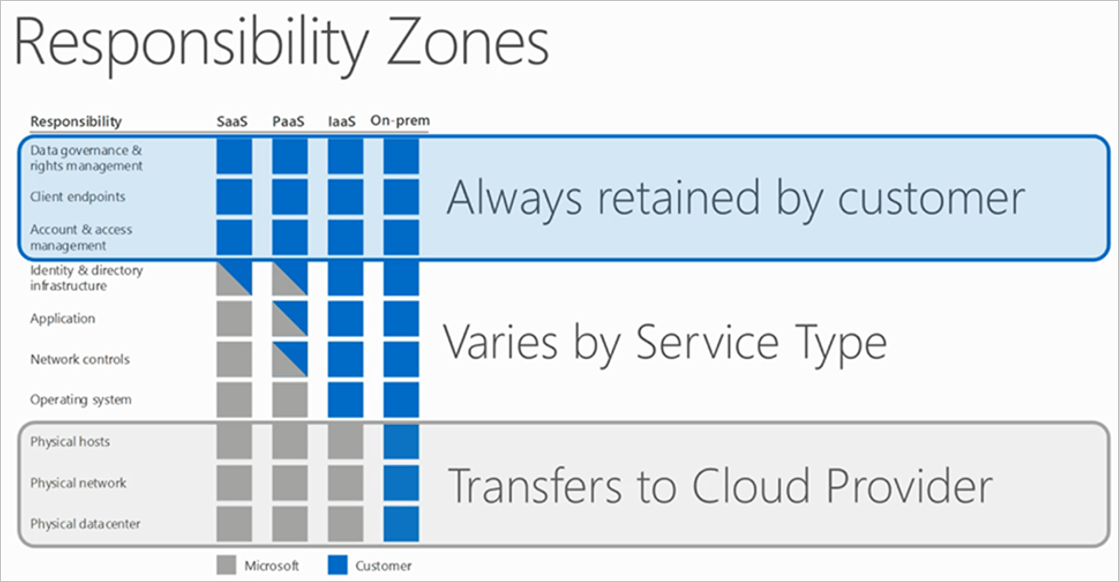
Microsoft Azure has a bit of a different approach to shared responsibility. Essentially, responsibility for identity and directory infrastructure, as well as network controls and applications for PaaS and IaaS, are retained by the customer. The only aspect of security that transfers wholly to Azure is physical security. Per Microsoft’s words, “Ensuring that the data and its classification is done correctly and that the solution will be compliant with regulatory obligations is the responsibility of the customer. Physical security is the one responsibility that is wholly owned by cloud service providers when using cloud computing.”
Aforementioned clarifications should clear away the fog on who is responsible for what.
Cloud Complexity
With more and more businesses adopting digital transformation, “moving everything to the cloud” seems like a one-way road. But it is not an easy one. According to a recent report by Cloud Security Alliance, an increasing number of companies are embracing a “hybrid” cloud model where they combine on-premises services with public cloud ones. Furthermore, companies do not rely on a single cloud service provider (CSP), but they tend to get services from multiple CSPs. The problem is that cloud platforms include ecosystems of services that are not always fully compatible with each other, causing data ownership and interoperability issues. In addition, the various cloud options also need to be integrated with on-premise networks and other third-party services. Adding to the cloud complexity issue, an organization’s computing environment must be able to remain secure and stay current with regulatory compliance protocols. Perhaps it is obvious, but moving to the cloud doesn’t change many of the considerations we would have in a more traditional environment.
Cloud Security: Concerns and Challenges
In order to explore how organizations are responding to the evolving security threats in the cloud, Cybersecurity Insiders in cooperation with Synopsis surveyed IT professionals and published their findings in the 2019 Cloud Security report. The report highlights what is and what is not working for security operations teams in securing their cloud data, systems and services within the shared responsibility model. An overwhelming majority of cybersecurity professionals (93%) say they are at least moderately concerned about public cloud security, while only 37% are very confident or extremely confident in their organization's cloud security posture. The low level of security confidence is in line with the findings of a Tripwire survey during Black Hat USA 2019, where 84% said that it was difficult for their organizations to maintain security configurations across cloud services. Of those, 17% said it was “very difficult.” The biggest concerns shared by the survey respondents are related to data loss (64%) and data privacy (62%), while 39% are concerned about legal and regulatory compliance. These findings are closely related, since data privacy regulations such as GDPR and CCPA are pushing for severe penalties in case of a data breach and violation of the privacy legislation. It is obvious that data breaches are a security concern, as a data breach is the result of a break in security controls and the unwanted outcome along with the loss of availability of data and loss of data integrity.
When it comes to the way companies protect their data in the cloud, cybersecurity professionals say access controls (52%) are the primary method they use to protect data in the cloud followed by encryption or tokenization (48%) and the use of security services offered by the cloud provider (45%).
The latter finding – use of native CSP security services – highlights certain myths and misconceptions that shape the way enterprises are making decisions. CSP-offered security services cannot serve the needs of an enterprise-wide security, especially when this enterprise uses multiple cloud platforms. If your corporate strategy caters for cloud agility, why should your cloud security strategy be pinned to one cloud provider? Organizations that want to be agile and avoid vendor lock-in need a cloud-agnostic solution that not only provides the ability to centrally enforce security policy but also the ability to standardize roles and responsibilities so that applications and their data can truly live within one or more clouds without fear of breaking or slowing operations. When it comes to compliance challenges, monitoring cloud services for new vulnerabilities stands out at 43%, followed by going through audits and risk assessments (40%) and monitoring for compliance (39%). Businesses are also struggling at maintaining a high level of compliance when migrating workloads to the cloud. Eighty-four percent of the respondents said that it is extremely important or very important to maintain continuous compliance when migrating workloads to the cloud. Overall, the findings in this report emphasize that to protect their evolving IT environments, security teams must reassess their security posture and strategies before addressing the shortcomings of legacy security tools and approaches.
How Tripwire Helps Secure Your Cloud Environment
As discussed before, you should consider implementing a cloud-agnostic security solution. Configuration management, vulnerability management and log management can be better handled with the help of a company that has specific expertise with these security services. It is also strongly recommended to download Tripwire’s free whitepaper on Securing AWS Cloud Management Configurations, especially if you’re considering AWS as your cloud provider. To learn more about staying secure in the cloud, find out what 18 experts advise for effective and secure cloud migration here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

