
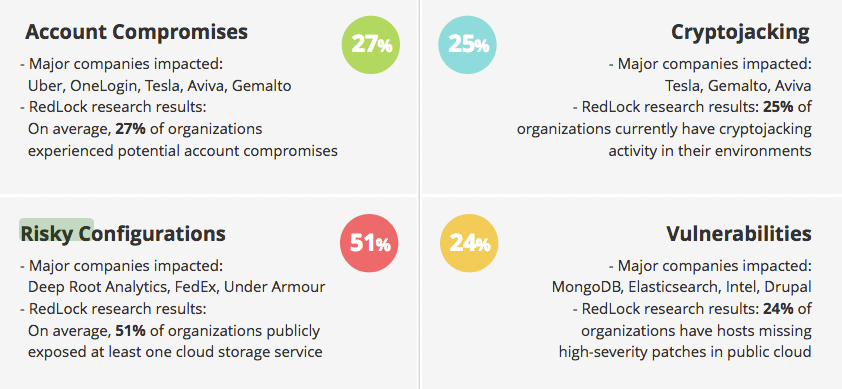
Cryptojacking attacks affected a quarter of organizations in their cloud environments, found a recent cloud security report. In RedLock's Cloud Security Trends, researchers with the security firm's Cloud Security Intelligence (CSI) team discovered that 25 percent of organizations had suffered cryptojacking incidents in the cloud. This rate marked a 300 percent increase over the previous quarter (February 2018) at just 8 percent. Even so, cryptojacking wasn't the most prolific security issue which organizations encountered in the cloud. Risky configurations topped that list at 51 percent, which means a majority of companies misconfigured and/or exposed a cloud storage service like an Amazon Simple Storage Service (S3) bucket. Account compromises also beat out malicious cryptomining attacks at 27 percent of organizations. Vulnerabilities were the only threat analyzed for the report over which cryptojacking was more prevalent. Specifically, RedLock's researchers found that almost a quarter (24 percent) of organizations lacked high-severity patches in the public cloud.
Cloud Security Trends report page 4 It wasn't all bad news, though. The report found that the percentage of organizations embracing database encryption, a practice which can help firms reach the General Data Protection Regulation's (GDPR) pseudonymization requirement, is increasing. 82 percent of cloud-based databases weren't encrypted a year ago. That percentage decreased to 49 percent in the latest report. RedLock's researchers explain in the report that organizations can't address cryptojacking by the piecemeal implementation of security measures:
The rise of cryptojacking and seemingly misuse of security groups highlights the need for a holistic approach to security in the cloud. A combination of configuration, user activity, network traffic, and host vulnerability monitoring is necessary to detect advanced threats in public cloud environments.
Organizations should also take steps to protect themselves against some of the other threats mentioned in RedLock's report. For instance, they can follow these recommendations to prevent an AWS S3 storage breach. They should also consider reviewing the strength of their vulnerability management program or setting up such a framework if they don't already have one.

