
Data exposure reports have reached a dizzying pace in the past few months, and the security community has been focused on the risk from multiple angles. Now, a new study from HTTPCS gives us new insight into rates of vulnerable S3 configurations. HTTPCS scanned s3.amazonaws.com addresses looking for storage “buckets” and logged data on those that were empty, containing publicly readable files, as well as which buckets were writable. Out of the 100,000 buckets found, 10 percent were public in that they allowed any worldwide user some form of access. This statistic is in line with the previously reported research of public bucket numbers near 7 percent. Importantly, we now have greater insight into how these public buckets are configured. Fifty-eight percent of the public buckets contained readable files. This means that the potential for a data breach is there, but there are many reasons to have readable files publicly accessible, so this does not tell us the bucket is necessarily vulnerable. Most crucially, the research shows that 20 percent of publicly accessible buckets are writable. This is a critical vulnerability for multiple reasons. Attackers can use the public buckets for more attacks, serving or controlling malware at your expense. They could alter your organizations website hosted in S3, defacing it or serving cryptocurrency mining JavaScript that tarnishes your reputation. Attackers can also encrypt data found in the buckets and attempt to hold it for ransom. Anyone could be storing anything for any reason, all of which would be paid for by someone else. Simply put, public read/write access is a devastating vulnerability that gives attackers complete ownership of the S3 bucket.
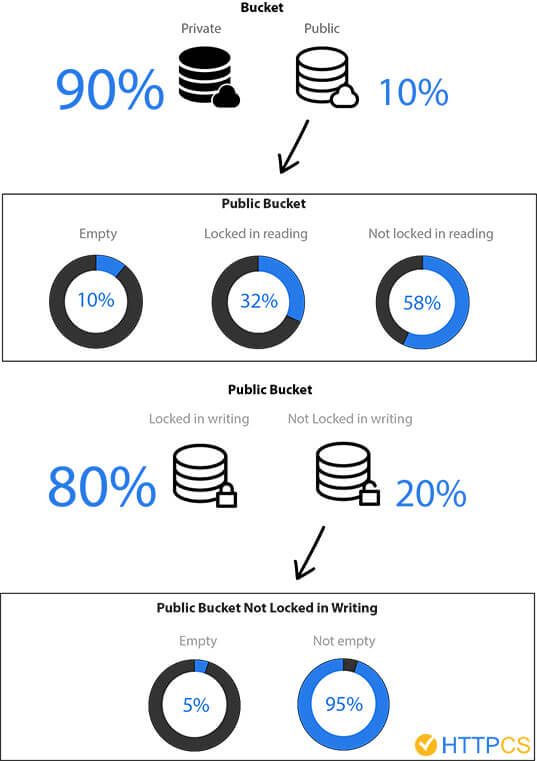
Illustration Legend : Diagram illustrating the results of the study conducted by HTTPCS Total S3 usage numbers can be hard to find, but SimilarTech claims nearly 400,000 websites are currently hosted using S3. A conservative extrapolation from websites alone says that there may potentially be 8,000 website S3 buckets exposed with write access. We’ve discussed how attackers and defenders are both using tools to find S3 exposures and how it is critical to routinely audit the security of your cloud infrastructure. These numbers shed new light on the nature of S3 data breaches. To learn more about staying secure in the cloud, find out what 18 experts advise for effective and secure cloud migration, here.

Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

