
A company responsible for helping to operate LeakedSource.com has submitted a guilty plea following an investigation by the Royal Canadian Mounted Police (RCMP). On 17 May, Defiant Tech Inc. pleaded guilty to the charge of "trafficking in identity information and possession of property obtained by crime" in association with an investigation surrounding LeakedSource. RCMP initiated its investigation, dubbed "Project Adoration," back in 2016 when it learned that the website's servers were based in Quebec. Through this effort, law enforcement confirmed that the service contained a database of approximately three billion records containing users' personal information and login credentials. The site allowed interested parties to access these records for a fee. Overall, Defiant Tech Inc. generated $247,000 from tracking victims' personal information via the site.
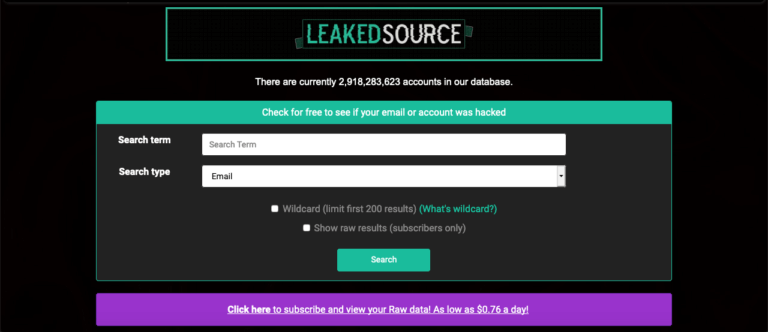
A web archive screenshot of LeakedSource.com. Superintendent Mike Maclean, criminal operations officer at the RCMP's national division, explained that he is pleased with the outcome of Project Adoration, an effort which involved the assistance of the Dutch National Police and the FBI. As quoted in a statement:
We are pleased with this latest development. This is all thanks to the relentless efforts put by our men and women working in the National Division Cybercrime Investigative Team. I am immensely proud of this outcome as combatting cybercrime is an operational priority for us.
Defiant Tech wasn't the only entity ever involved with the management of LeakedSource.com. As reported by Brian Krebs back in 2017, it appears that a U.S. individual named "Jeremy Wade" might have had a part to play, as well. But that individual never received any criminal charges. Project Adoration reveals how there are services available to digital criminals and identity thieves alike that make their jobs easier. In response, users should consider signing up with Troy Hunt's Have I Been Pwned service so that they can receive an alert if a security incident ever compromises their login credentials. They should also follow these steps to protect themselves against identity thieves.

