With all the Russian election hacking scandals in the news during and after the 2016 Presidential election, curiosity consumed me to architect and run an experiment to see if I could monitor changes in the threat landscape in either Moscow, Russia or Washington D.C. during the 2018 U.S. midterm elections.
I have worked in four Security Operations Centers (SOC) and have been in a leadership capacity at two. These SOCs have ranged in size from smaller companies to the Big 4. I am no stranger to security monitoring, and if there is anywhere that I like to be, it is where the action is.
My expertise and passion led me to a honeypot project. Honeypots are deceptive security technology that are designed to sit strategically on a network with services that entice attackers to hack. When a honeypot monitors a connection to these services, it sends detailed logs to a centralized log server that monitors in real time the threat landscape.
I used the Modern Honey Network for this project, a brilliantly designed network which allows you to deploy deceptive honeypots. I began on this project by deciding what I wanted to monitor and what a significant change in the threat landscape would need to look like if it were to indicate increased or decreased cyber activity resulting from the elections.
I decided to buy two dedicated Virtual Private Servers (VPS) located in Moscow, Russia, and one VPS in Washington, D.C. I deployed the Dionaea honeypots to each of the VPS on Ubuntu 14.04 LTS servers. Dionaea honeypots are designed to have numerous vulnerable-looking services as well as a trap to capture malware. Additionally, I spun up two Amazon AWS Dionaea Honeypots in Ohio to act as a control.
Roughly a month before the elections, the infrastructure was completely set up, and all the honeypots were sending hundreds of thousands of security events a day to my Elastic, Logstash, Kibana (ELK) stack.
Within seconds of deploying it to the public internet, the honeypot got attacked. The takeaway from this observation is that if anyone in your company deploys a non-patched, unhardened system to the public internet for any amount of time, they should assume that the system has been compromised.
I played with Kibana to create the best dashboards to visualize the data I was getting. I created this dashboard to be the dashboard that would run 15 days prior to and after the election.
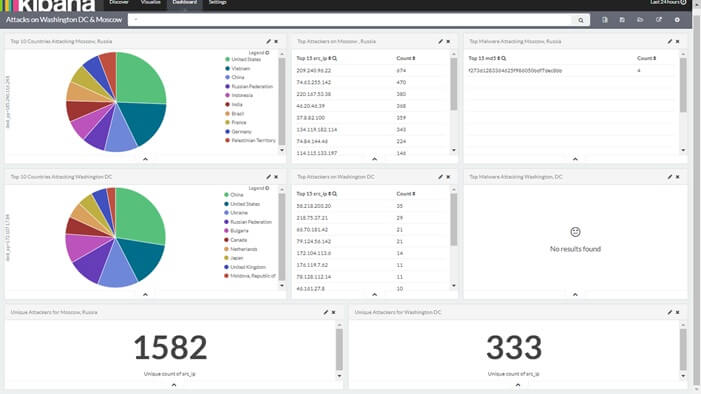
This basic dashboard shows a list and pie chart of what country the attacking IP address was sourcing from, the numbers on unique attacks and a list of the top 15 attack source IP addresses. Also, it lists the samples of malware that they picked up.
Now, I waited for 15 days after the election. What I expected to find was two distinct sets of data. One for Moscow and one for the United States.
Midterm Elections
As it turns out, there were not any significant changes in threat landscape during the election no matter how hard I tried to find a correlation of data. What I found was that the Top 100 attackers in Moscow were almost identical to those in Washington D.C. – I had the same findings in the Ohio honeypots.
As time continued, the data normalized across all the geographical locations of honeypots. All the honeypots captured multiple instances of the same malware samples, and during my observations, there were not any instances of regional malware outbreaks.
The below pie chart represents one Moscow, Russia honeypot. The Ohio and Washington D.C. honeypots had a similar breakdown of source countries and became almost identical at the close of the project:
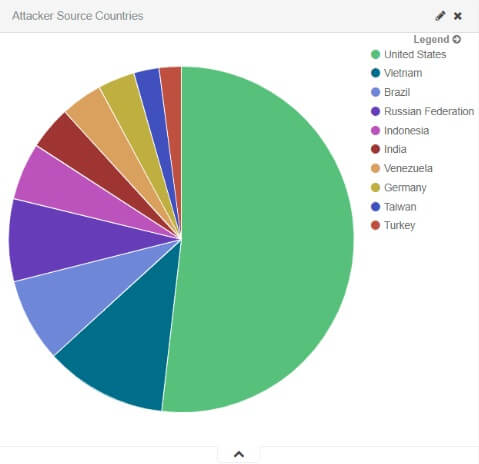
My conclusions are that the internet is a war zone that does not discriminate on which country the data lives in. My analysis of all these attackers proved that these are all known bad actors who are generally bots or compromised web and file servers.
IP addresses that are found in a public-facing honeypots are almost always true representations of malicious attacker. These IP addresses can feed back into your SIEM and thereby determine if there is any suspicious outbound activity from your internal network to these hosts. With a reasonable amount of checks, they can be inserted into blacklists on your firewalls to improve your security posture.
I discovered that there is no product to my knowledge that can take a large set of attacker IP addresses and tell you which emanated from an intelligent human. The intelligent human signifies a more persistent, patient and even more targeted attack source. Something worth investigating further.

About the Author:
Tyler Wall is a security fanatic. Employed as a Senior Security Engineer by day and born with a natural curiosity for anything and everything that spills over into everyday life by the form of his many (mis)adventures. He holds numerous security certifications and degrees and describes himself as a catalyst for positive change.
Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor and do not necessarily reflect those of Tripwire.

