
Organizations are constantly looking to obtain a "big picture" view of information security so that they can better protect themselves against digital threats. To answer that call, a variety of companies regularly publish security trend reports in which they analyze how threats in the digital space are evolving. Some reports target specific kinds of threats, such as Lastline's annual review of top malware trends. Others collect threat information from others to better understand the industry as a whole, like Verizon does in its Data Breach Investigations Report. Still others combine the two, relying on their own data to provide organizations with insight into overarching threat trends in the security industry. One such publication is Microsoft's Security Intelligence Report. For more than a decade, the Redmond-based tech giant has been gathering data on threat trends. It has collected information from more than 600 million computers to write each year's report. This year, however, Microsoft decided to do something a little different different. In an attempt to help drive awareness, the company decided to publish 2016 Trends in Cybersecurity: A Quick Guide to the Most Important Insights in Security. This resource is meant to summarize the 198-page Security Intelligence Report. Microsoft's newest publication identifies 10 important trends in security that organizations can use to better protect themselves and the industry against digital threats. These are as follows:
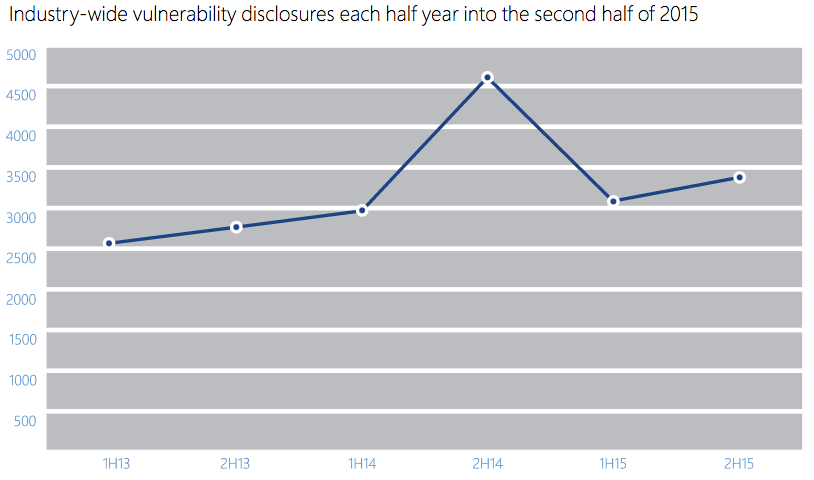
1. "Highly Severe" Vulnerabilities Are Up
Microsoft observed that nearly half (41.8 percent) of all vulnerabilities are rated "highly severe," which represents a three-year high. Additionally, it saw that disclosures rose 9.4 percent between the first and second halves of 2015, reaching a total of just above 3,300.
2. Java Exploits Are Down Attackers used to favor Java exploits, but that no longer seems to be the case. Malicious actors are increasingly turning away from incorporating Java into their attacks, likely as a result of changes in the way browsers evaluate and execute Java applets.
3. Enterprise Computers Encounter Half the Exploits of Consumer Counterparts
Enterprises commonly use defense-in-depth firewalls to protect users against malware. As a result, corporately owned computers generally encounter about half of the exploits seen by consumer computers even though they came across threats just as frequently.
4. Some Locations Have Higher Malware Rates than Others
Malware infection rates vary based upon where people live. For instance, Mongolia, Libya, the Palestinian territories, Iraq, and Pakistan had some of the highest infections rates globally. The worldwide malware infection rate in the fourth quarter of 2015 was 16.9 computers cleaned per every thousand scanned.
5. Exploit Kits Account for 40 Percent of Most Commonly Encountered Exploits
A typical exploit kit consists of compromised web pages containing several vulnerabilities. All an attacker need to do is rent or purchase an exploit kit and infect users via drive-by downloads. It's little wonder therefore that attackers with little to no technical skills gravitate towards exploit kits as opposed to developing their own malware.
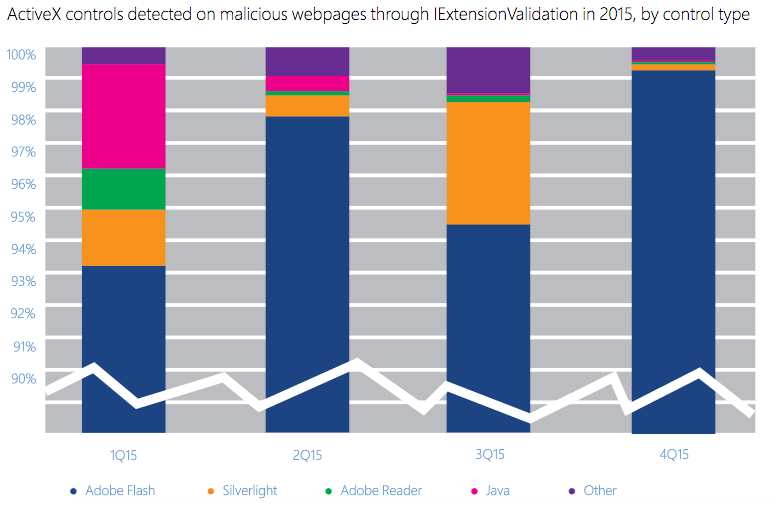
6. Adobe Flash Player Objects Appear on 90 Percent of Malicious Pages
While they once primarily used Java, attackers are now shifting to incorporating Adobe Flash Player into their exploits. Today, Adobe Flash Player objects appear on more than 90 percent of malicious pages. Users should therefore make it a priority to implement Adobe Flash Player security updates as soon as they become available.
7. Majority of Flaws Not Found in Browsers, Operating Systems Nearly half (44.2 percent) of all vulnerabilities are found in applications other than browsers and operating systems. With that in mind, organizations need to make sure they look to other applications if they are to remediate the vast majority of flaws disclosed.
8. Trojans Increased and Remained at Elevated Levels
Trojans increased by 57 percent. There's little wonder why. They rely on social engineering to trick users into believing the programs will do one thing while in actuality they will engage in malicious activity. While a high level of technical expertise is needed to develop trojanized software, malware authors can eventually rent out their programs to computer criminals with lower levels of technical expertise.
9. Threats Vary in Prevalence Depending on Nature, Location
Similar to its findings with malware, Microsoft observed the prevalence of a threat varies based upon its inherent nature as well as location. For instance, while some countries experience more ransomware infections, others see more trojans. This variation helps to explain why it is nearly impossible for companies with worldwide operations to achieve "perfect" security.
10. Microsoft Software Had a Low Comparative Rate of Vulnerability Disclosure
In any six-month period, less than 10 percent of vulnerability disclosures were found in Microsoft software. This finding illustrates the importance of prioritizing vulnerabilities based upon their severity and developing a patching schedule that addresses high-risk bugs first.
Conclusion
By learning about some of the most important trends in information security, organizations can better protect themselves against today's digital threats. Microsoft has provided some recommendations on how companies can protect against each of the trends discussed above. For more information, please view its 2016 Trends in Cybersecurity guide, or read through its most recent Security Intelligence Report.

