
"Do you buy, build, or partner for cyber security capability" This is a question a lot of MSPs and IT providers are looking a right now. It’s no secret that according to the CompTIA data (see below chart), the Cyber Security discussion with businesses will be a hot topic worldwide.
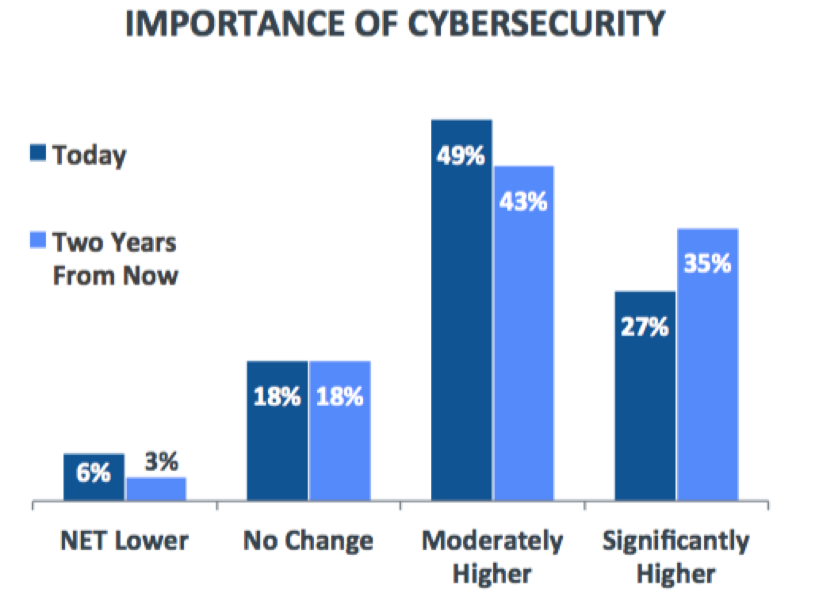
Another interesting number from CompTIA is that 79% of businesses expect security to become an even higher priority over the next two years. MSPs or IT Providers looking to prosper and grow should consider adding cyber security capability into their toolsets. Sadly, that’s easier said than done. According to the 2016 report Hacking the Skills Shortage by McAfee and the Center for Strategic and International Studies, the news is pretty stark. Whatever way you look at it, “cyber security capability it both badly needed by business and hard to obtain.” Respondents in all (eight) countries surveyed said cybersecurity education was deficient. Eighty-two percent of respondents reported a shortage of cybersecurity skills, while more than three out of four respondents (76%) believe their government is not investing enough in cybersecurity talent. Additionally, this shortage in cybersecurity skills does direct and measurable damage, according to 71% of respondents. One in three says a shortage of skills makes their organizations more desirable hacking targets, and one in four says insufficient cybersecurity staff strength has damaged their organization’s reputation and led directly to the loss of proprietary data through cyberattack.
Building an internal security resource
These are figures that MSPs and IT Providers can benefit from by buying, building, or partnering with the security market development. Be warned, though: do not travel the security road lightly. While presenting at DeepSec in Vienna, Austria, I got the chance to have a pint with Thomas Fischer, Global Security Advocate at Digital Guardian, who has done IT work in places as far flung as Africa, Latin America, and eastern Europe – places other infosec members may fear to tread. Here's what he told me:
"It’s hard to build an IT security resource internally, especially from already busy staff. So, you either plunge them into the deep end of the security pool and see how it goes, or you’re going to have make time for your candidate to figure out security things. Time is the most important thing you can give if you’re considering morphing a systems, dev, or admin into a security resource – and they have to have a natural curiosity and passion for security."
The decision to buy or partner with a cyber security firm has a lot to do with the cash flow of your MSP or IT provider business. With the cyber security market subject to the laws of supply and demand (just like any market), good quality cyber security talent is currently at an all-time high demand high and low supply. Expect to pay a premium for a company with some credentials and experience.
Partnering with someone with the right skill set
If your MSP or IT provider business isn’t turning a big enough profit to make this investment, then it may be a good idea to form a partnership with a larger firm that has cyber security skills – with some references, of course. Networking channel events sponsored by CompTIA and ASCI, as well channel partner events provided by suppliers like SolarWinds MSP, is a great place to find firms to partner with. These two strategies can give you access to a “security person.”
Doing it yourself
Central to the question of building cybersecurity capability is: can an MSP or IT Provider make a “security person”? The answer is yes, provided there is the right material to work with and the person is passionate and motivated. It’s going to take some work to build the cyber security skills necessary to be useful and valued as a security resource. Cyber security capability has to be built on a basic understanding of network administration, system administration, and some understanding of software development. A few entry-level certifications or a technology program and a few years of experience form a solid foundation. Experience in network infrastructure architecture, switch, firewall and router configuration, as well as other operating systems is also a requirement. Other skills that are highly desirable are succinct oral and written communication skills (especially useful for presentations and written work) alongside some experience in managing or serving as a key resource on a project.
Training & Feeding
At some point, to ensure credibility in the market place as a “security firm,” certifications of your security resource are going to be required. It’s a controversial topic in IT security, as what is frequently learned in the classroom on courses that range upwards of USD $5000 in price may not be appropriate for real-life security challenges at the SMB/SME level. In the first year, it may be prudent to consider online course materials rather than in-classroom training, which can cost upwards of USD $10000 when hotels and flights are considered.
Cleaning & Maintenance
This is perhaps the least expensive but most important requirement for a cyber security resource: the cyber-defense lab. One or two machines with excellent processor capabilities and considerable amounts of RAM are necessary for running Virtual Machines to work on secure configurations, testing and research. If you have standardized customers on a standard platform, it may be a good idea to equip the lab with those, as well. That’s a great place to make sure the latest firmware is good-to-go before melting down a customer’s firewall with an upgrade that goes wrong. Keep in mind most of the software tools used by cyber security professionals are open-source or free.
Treats & Rewards
Certainly a quarterly or bi-yearly bonus tied to the security resource’s Management by Objectives (MBOs) is advisable. MSPs and IT Providers can expect a requirement for flexible hours, remote work and overtime (if a customer requires it). Customers don’t like downtime even for security work or really any sort of IT work, so weekend work is usually essential, as well. Since there are so many security conferences and events held in almost every part of the country, employer support for these conferences is important to consider in order to keep the security skill set current.
Discipline & Accountability
IT Security does not mean that standard employee policies don’t apply to your resource. IT security testing and research should NEVER occur in a production network – the MSP or IT providers and certainly NEVER EVER in a customer’s network. Accidentally infecting a customer’s network could potentially get your organization sued, put the customer relationship under extreme jeopardy, and even get you fired. Every proposed security adjustment, upgrade, or change should require documentation, a test plan and a back-out plan. If something goes wrong, be fair, firm and friendly when trying to figure out what went happened.
Passion & Commitment
Making security resources feel like they're part of the team can be challenging. As an MSP or IT provider, when discussing security it’s important to have enough of an understanding of security to engage in conversation. Asking open-ended questions is a great idea to connect with the security resource. “What do you think went wrong at Talk Talk? Do we have any customers that could be attacked that way? What can we do to prevent that from happening?” Don’t accept “No” as an answer from the security resource. Instead, ask “how can I do this securely; can you give me options from very secure to hideously insecure?” As mentioned before, buying, building, or partnering for security capability is an important decision for the MSP and IT provider’s growth plan in the years ahead. Perhaps the most important trait is the personality of the resource. Security resources, just like all employees, have to work as a team and be able to engage with team members and customers as required. Pay close attention to those interview behavioral-based questions, and choose someone who would work best at your organization.

About the Author: Ian Trump, CD, CEH, CPM, BA is an ITIL certified Information Technology (IT) consultant with 20 years of experience in IT security and information technology. Ian’s broad experience on security integration projects, facilitating technological change and promoting security best practices have been embraced and endorsed by his industry peers. From 1989 to 1992, Ian served with the Canadian Forces (CF), Military Intelligence Branch; in 2002, he joined the CF Military Police Reserves and retired as a Public Affairs Officer in 2013. Currently, Ian is the Security Lead at LogicNow working across all lines of business to define, create and execute security solutions to promote a safe, secure Internet for Small & Medium Business world-wide. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

