
Click-fraud is traditionally thought of as a widespread but low-impact online risk. Using this method of attack, criminals steal money away from pay-per-click (PPC) online advertisers by commanding another person or bot to click on an ad for the purposes of generating a charge per click. No actual interest is generated by these fake clicks, and the advertiser's budget is subsequently exhausted. Given the variety of other risks populating today's threat landscape, security professionals tend to overlook instances of click fraud and address higher priority attacks that directly affect users. However, new research is challenging this mindset, suggesting that click fraud can be used to deliver additional, more serious attacks downstream on an enterprise's network. As revealed in their State of Infections 1H 2015 report, security researchers with Damballa detected one instance of a click-fraud campaign that was used to launch secondary and tertiary attacks against a compromised device. The threat, which the researchers named "RuthlessTreeMafia," started off with a phishing email that installed the Asprox botnet malware. Upon successful infection, Asprox received an update from its C&C servers in the form of a Zemot dropper, which included Rovnix (a rootkit) and Rerdom (a click-fraud installer).
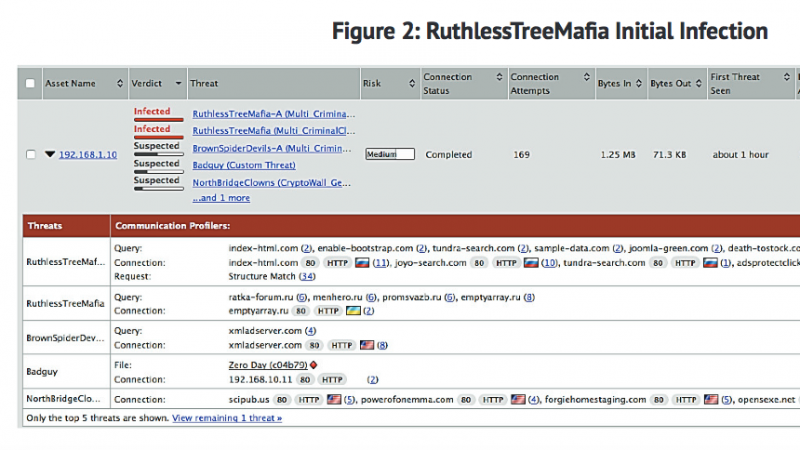
Source: Damballa The operators of the attack then sold multiple threat actors access to the compromised device, which generated additional revenue for the original attackers. One of these actors, known to Damballa as "HotLakeTroop," appeared on the infection chain and then installed six instances of the same file via direct IP connection to the device. Later analysis revealed that the downloaded infection was CryptoWall, a strain of ransomware which encrypts all of the system's host files. In two hours time, the initial attack resulted in three additional click-fraud infections, including CryptoWall. Earlier this year, the FBI released a statement warning businesses that CryptoWall attacks have caused organizations at least $18 million of losses in the past year. This finding, however, is part of a larger trend in which ransomware infections are on the rise. In the first quarter of 2015 alone, McAfee Labs detected a 165% increase in ransomware samples, which is in spite of the decline of CryptoLocker ransomware following an international legal takedown in 2014.
Stephen Newman, CTO at Damballa, hopes that this latest report on click fraud will help draw attention to the importance of watching initial infection vectors closely.
“The changing nature of these attacks, underscores the importance of being armed with advanced detection, to combat these more stealthy threats. As infections can spread quickly through the network, security teams should take proactive measures to avoid becoming a cautionary click-fraud tale,” Newman told Softpedia.
To learn how Tripwire's threat intelligence solutions can help your organization stay ahead of click-fraud attacks and protect against more serious threats, please click here.
Title image courtesy of ShutterStock

