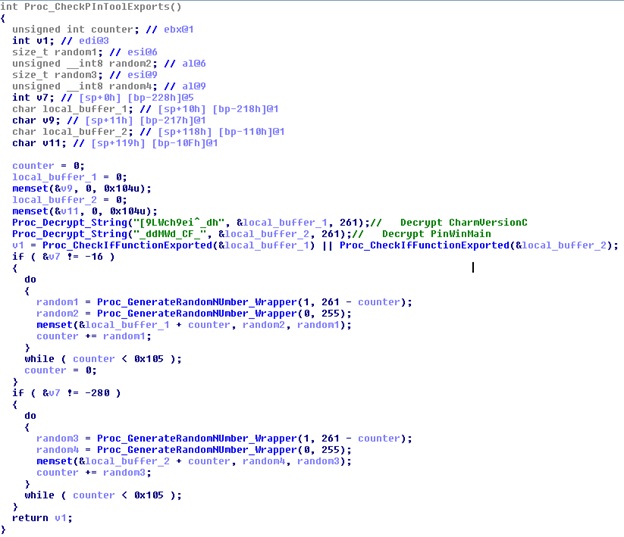
For decades, the field of computer security has evolved as a cat-and-mouse game between security researchers and malware authors. When the former devises new methods to detect malicious programs, the latter incorporates into their software dormant functionality scenarios and a variety of other evasive techniques – four of which are now particularly common among malware samples – to counteract them. These advancements have, in turn, led to the creation of Rombertik, BlackPoS and other poster children of a new generation of sophisticated malware. According to a blog post published by advanced persistent threat (APT) defense firm Lastline, traditional sandboxes attempt to counteract these evasive tactics employed by malware by using off-the-shelf hypervisors to contain the execution of a malware sample inside a virtual environment. But in many of these solutions, the CPU is not fully virtualized, meaning that the sandbox is dependent on analyzing the fingerprints of a malicious sample and passing it off to a library function or system call where the program's components can be analyzed. The malware therefore runs on a real CPU, which allows the malicious program to fingerprint the system on which it is running and scan for indicators of an active security solution. These signs commonly include programs that might be part of an analysis suite, system library hooks, or kernel drivers meant to intercept and record system calls. If any of these signs are detected, the malware sample terminates and preserves the integrity of its internal code. Just as each malware variant comes with different functionalities, each sample can modify the process of system fingerprinting to suit its needs. Indeed, as revealed in another blog post published by Lastline, the authors behind Darkhotel – an advanced persistent threat (APT) group that conducts spear-phishing campaigns and tracks its targets via hotel networks around the world – have introduced an update into their malicious code to prevent leaking information about how the sandbox is fingerprinted. Darkhotel's new functionality protects the internals of the malware by making sure that the program contains only hashed or encrypted versions of the fingerprint information. Furthermore, when the program decrypts the rest of the program memory, the strings used for fingerprinting do not follow. Instead Darkhotel uses just-in-time decryption to temporarily decrypt the fingerprinting strings when needed. "The code first decrypts fingerprint strings (in this case, the names of functions) into a temporary buffer using a custom algorithm (see Proc_Decrypt_String)," explains Lastline researchers Arunpreet Singh and Clemens Kolbitsch. "Then, it checks if these functions are exported inside the target process (see Proc_CheckIfFunctionExported): a positive identification reveals the presence of an analysis system." "Once the string is no longer needed, the temporary buffer is overwritten with random data (using Proc_GenerateRandomNumber) before the buffer is released. This way, plaintext fingerprint strings reside in process memory only for the absolute minimum of time that is necessary."
Source: Lastline If this decrypting feature were not enough, the authors of Darkhotel have also equipped their malware with a number of other functionalities designed to detect whether their program is running inside a sandbox environment. Among other things, it looks for the following:
- Analysis Subject: Darkhotel checks to see if the filename ends with ".Md5.exe" if its length is greater than 8--a common practice used by security researchers and sandbox solutions. It also checks to see if it has been executed from the root of the C:\\ drive.
- Process Memory: The malware looks to see if the libraries "snxhk.dll”, “snxhk64.dll”, or “sxIn.dll” are stored in the process memory, which would suggest that Avast Antivirus is offering sandbox protection on that particular machine. Additionally, it compares the executable names of the running processes on the system against a hardcoded list to determine if any other known AV software is running.
- Cuckoo Evasions: Cuckoo is a popular open source sandbox, and good number of free and commercial sandboxes are based on cuckoo technology. Darkhotel makes a special efforts to detect Cuckoo by:
- Checking for the presence of named pipe (\\\\.\\pipe\\cuckoo)
- Detecting cuckoo user mode dll by iterating through all the modules loaded in process and checking if "hook_disable_retaddr_check" is exported
- Checking if username is "Cuckoo" or if loaded module path contains substring "Cuckoo"
- Enumerating through the windows and checking for the presence of "START_PROCESS.PY" (Cuckoo's agent window)
- System Clock: The malicious program uses a function to determine whether the system clock has been tampered with, a tactic that is sometimes employed by analysis systems when scrutinizing malicious samples.
To successfully analyze Darkhotel, a sandbox must pass all of these individual tests. This reality highlights the advantages of using a true full-system emulator to analyze a malicious program. The Lastline sandbox uses a full-system emulation approach, which enables the security firm to detect Darkhotel's decryption of its fingerprint strings and its processes involved with identifying a security solution. To read more about Darkhotel, click here.

