According to the 2015 Information Security Breaches Survey, a PwC study that I recently analyzed in an article for The State of Security, the number of denial of service (DoS) attacks has either dropped or remained stagnant for most UK corporations over the past year. Apparently, this decline has not stopped certain malicious actors from getting creative with their distributed denial of service (DDoS) attacks, however. Among those groups that have embraced DDoS attack campaigns this past year is Lizard Squad, a hacking group that set up a DDoS stresser service earlier in 2015 after successfully overloading the networks of both Playstation Network and Xbox Live on December 25th, 2014. These attacks may have ultimately contributed to Akamai’s finding that the world saw a 90 percent increase in DDoS attacks in 2014’s final quarter as compared to Q3. DDoS attacks are also not exclusive to amateur hacking groups. Earlier this spring, China targeted GitHub with a large DDoS attack, which caused service interruptions for some users. Now in the middle of 2015, yet another group has put its own spin on this tried and true method of network disruption. As analyzed by Heimdal Security Software, a group of computer criminals known as ‘DD4BC’ is threatening targets with massive DDoS attacks unless they pay a ransom using Bitcoins. These attacks generally bring down vital business services and cause disruption and financial loss. Each campaign launched by DD4BC begins with an email that informs the victim of a low-level DDoS attack currently underway against the victim’s website. The email, as revealed by Akamai in a profile of the group, then goes on to demand a ransom paid in Bitcoins in return for DD4BC abstaining from launching a larger DDoS attack against the target. According to research published by the Swiss Government Computer Emergency Response Team, DD4BC is theoretically capable of launching attacks consuming a bandwidth of up to 500 Gbit/s, which is about 1,000 times the capacity of a DSL/cable line, by taking advantage of amplification attacks that abuse the NTP, SSDP or DNS protocol. In reality, Incapsula, a cloud-based application delivery platform, has noted in a blog post that the group generally launches small application-layer attacks that peak at 150 requests per second. This does not stop security personnel and law enforcement officials from taking DD4BC seriously, however.
“We are working closely with law enforcement in various jurisdictions to make sure they have a clear picture of what we see and face,” Troels Oerting, group chief information security officer at Barclays and former head of Europol’s European Cybercrime Centre (EC3), told to Computer Weekly. “We take the necessary steps to prevent, detect, react and mitigate all kinds of cyber crime we face, and that is simply the way we work. We take our customers and employees' privacy and security very.”
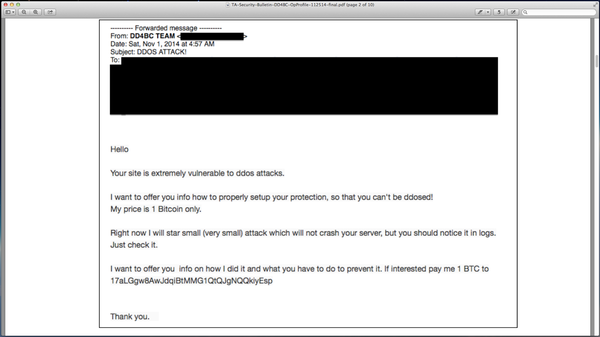
Source: Akamai The exploits of DD4BC go back at least a year. In November of 2014, reports emerged of the group having sent a note to the Bitalo Bitcoin exchange demanding 1 Bitcoin in return for helping the site enhance its protection against DDoS attacks. At the same time, DD4BC executed a small-scale attack to demonstrate the exchange’s vulnerability to this method of disruption. Bitalo ultimately refused to pay the ransom, however. Instead, the site publically accused the group of blackmail and extortion as well as created a bounty of more than USD $25,000 for information regarding the identities of those behind DD4BC. Since then, the group has begun demanding Bitcion ransom payments in exchange for refraining from launching large-scale DDoS campaigns. In March of this year, for example, DD4BC targeted Bitmain, one of the largest Bitcoin mining equipment manufacturing companies in the world, and demanded a ransom payment of 10 BTC to prevent an attack. Like Bitalo, Bitmain refused to pay the ransom. In fact, it ultimately added 10 Bitcoins to Bitalo’s existing bounty. DD4BC is still active as of this writing and is demanding as many as 25 Bitcoins from affected parties in exchange for assurance against a large DDoS attack. To protect against the attacks launched by DD4BC and other groups, it is recommended that companies invest in anti-DDoS technology and create an emergency computer response team (as well as an organization-wide security policy) that outlines a plan of action if an attack ever arises. For additional DDoS mitigation techniques, please click here. Title image courtesy of ShutterStock

