
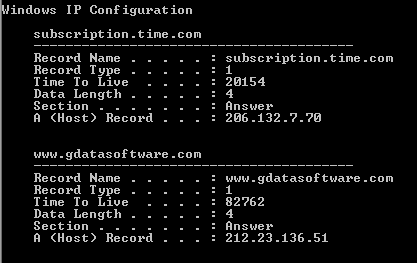
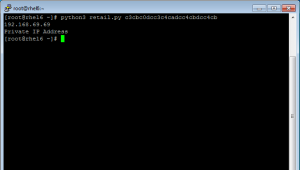
Protecting enterprise networks is a constant game of cat and mouse between information security professionals and malicious actors targeting their assets. Attackers are constantly changing their tactics for both establishing their foothold in the network, as well as methods on how to exfiltrate data back to systems they control. With the rise of exfiltration in current breaches, attackers are getting creative with how they hide their tracks. One such method was an analysis if the FrameworkPOS malware by G Data Software. The FrameworkPOS malware uses typical memory scraping techniques to find credit card data hidden in processes running on the endpoint. When the data is found, the malware utilizes DNS tunneling to connect to a command and control server to exfiltrate the data. The credit card data, IP address, and hostname are encoded via XOR and added to a HTTP request to send data out of the environment. While this hides the credit card data from a quick inspection of network traffic via firewalls and proxies, this is equivalent of security through obscurity for protecting the network. For users of Tripwire Enterprise, detecting malware like FrameworkPOS is straight forward. All malware leaves behind indicators of compromise that are detected by Tripwire. For FrameworkPOS, these include files, registry keys and system services. For exfiltration via DNS requests, detection is also possible. Windows stores the DNS queries to a cache and is accessible via the ‘ipconfig /displaydns’ command. Using a Command Output Capture Rule (COCR), the Tripwire Enterprise agents can pull the DNS cache and perform XOR functions to decode any internal IP addresses. Similar functionality on decoding DNS queries can be completed using Tripwire Log Center for a forensics analysis of potential exploitation attempts in the environment.
Even if your business does not have a retail network that is targeted by malicious software like FrameworkPOS, knowing how to detect and respond to their tactics is useful. While attacks targeted at retail environments will change, we are sure to see similar tactics against other industries. The shared tactics used by attackers is a key reason why sharing threat intelligence is becoming a necessity for mature security departments. Sharing of indicators of compromise, such as IP addresses, file hashes, and registry keys, is a step in the right direction. Sharing of malicious methodologies like those utilized my more advanced families of malware are going to be the next step in detecting indicators of compromise as attackers make additional efforts to hide their tracks and steal your most critical and sensitive data.
5 Things Your FIM Solution Should Be Doing for You
Discover the pivotal role of File Integrity Monitoring in maintaining system security and compliance with major standards. Tripwire Enterprise stands out as an advanced solution, offering real-time detection and detailed context for system changes, making it a superior choice for robust cybersecurity.

