
Someone leaked the source code for the Exobot Android banking trojan online, leading the malware to circulate widely on the underground web. Bleeping Computer said it received a copy of the source code from an unknown individual in June. In response, it verified the authenticity of the code with both ESET and ThreatFabric. Security researchers from the latter company told Bleeping Computer that the code was for version 2.5 of the malware, otherwise known as the "Trump Edition." They further clarified that someone leaked the source code for that variant in May.
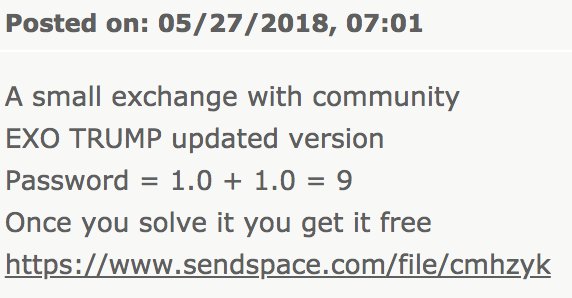
Posting of leaked Exobot "Trump Edition" (Source: Bleeping Computer) Exobot is a type of malware that targets Android users via malicious apps. Some of those programs made their way onto the Google Play Store at one point. Upon successful installation, the apps load up Exobot, which uses overlay attacks whenever the infected device's owner visits a banking website. This technique allows Exobot's handlers to steal users' banking credentials, which they can then use to siphon money from their accounts. As reported by ThreatFabric, the malware author announced the sale of their creation in December 2017. It's thought that someone who purchased the source code for the Trump Edition leaked it online in order to share it with the malware community. Indeed, Bleeping Computer confirmed the appearance of the malware's leaked source code on several underground forums following the leak. This development has security researchers concerned that there will be an uptick in Exobot-based attacks. After all, it happened with BankBot, a version of which exclusively targeted Google Play, after its source code made it to the web. Unfortunately, Exobot is just as effective a trojan as BankBot. Cengiz Han Sahin, security researcher and spokesperson with ThreatFabric, told Bleeping Computer as much:
The trojan gets the package name of the foreground app without requiring any additional permissions. This is a bit buggy, still, but works in most cases. The interesting part here is that no Android permissions are required. All other Android banking trojans families are using the Accessibility ore Use Stats permissions to achieve the same goal and therefore require user interaction with the victim.
Acknowledging those capabilities, it's important that Android users protect themselves by downloading apps from only trusted developers on the Google Play Store.
Financial Services Cybersecurity Regulations
Learn how Tripwire's strategies bolster cybersecurity in the financial sector. Facing heightened risks, financial organizations can benefit from Tripwire's expertise in security configuration management and file integrity monitoring, ensuring compliance with critical regulations and safeguarding sensitive data.

