
Security researchers have released a decryptor that enables victims of the Planetary ransomware family to recover their files for free. Released by Emsisoft, this decryptor requires a victim to have a copy of the ransom note. It's not hard to find. Planetary ransomware, which earns its name for its use of planet-related file extensions including ".Pluto" and ".Neptune," places a copy of its message in each folder in which it encrypted files as well as on the desktop of the infected machine. The ransom note demands that victims contact either "recoverymydata@protonmail[dot]com" or "recoverydata@india[dot]com" with their personal ID, which is obscured in the Bleeping Computer screenshot provided below. The attackers then promise to send over a decryptor once they've received payment from the victims.
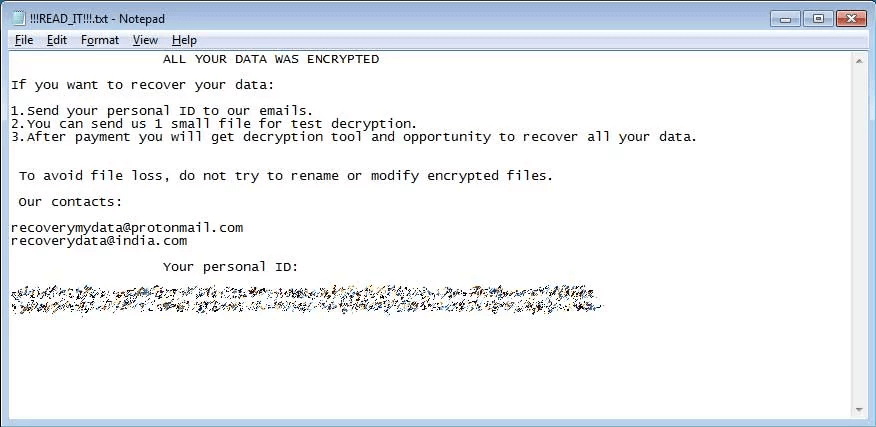
Screenshot of the Planetary ransom note. (Source: Bleeping Computer) Victims should download the decryptor, a link for which is available through Bleeping Computer, and save it to their machine's Desktop. They should then run the decryptor with admin privileges. This will ensure that the tool can recover all of the files affected by the ransomware. When they run the decryptor, the tool will ask the victims to select a ransom note and click "Start." The utility will then use that ransom note to display the decryption key used by the ransomware to encrypt the victim's files. At that point, the user can enter that decryption key into the decryptor screen, select any drives they'd like to decrypt and click the "Decrypt" button. Doing so will cause the program to search the computer for relevant file extensions used by the ransomware and, in turn, decrypt them. It's possible that those behind Planetary ransomware could plug whatever vulnerability which Emsisoft exploited to create its decryptor in the first place, thereby rendering its free tool ineffective. Given that possibility, users would be wise to back up their data on a regular basis. They should also follow these tips to prevent a ransomware infection.

