Few would dispute the idea that an effective cybersecurity profile requires candid assessments of potential vulnerabilities. Here’s a closer look at the challenges facing the federal cybersecurity mission and the efforts of state-level agencies.
Federal
Though the federal government demonstrates an ongoing commitment to ramping up its cybersecurity mission with annual spending in the tens of billions of dollars, key challenges include the decentralized nature of this effort spread across more than 100 agencies, each responsible for their own cybersecurity. Or, to put it another way: “Federal cybersecurity is a dense, inaccessible topic to those outside the information security community and even to some inside it. Information is scattered across a variety of government documents, with no ‘one stop shop’ to understand the topic.” This assessment is part of a comprehensive report (“Understanding Federal Cybersecurity”) by Harvard’s Kennedy School of Government and the Belfer Center for Science and International Affairs, which found that—in addition to the need for more efficient coordination and ongoing efforts to improve the technological tools and the operational strategies necessary for effective risk assessment and incident response—there is a significant “shortage in skilled cybersecurity-minded talent.”
State
Much of the reporting on cybersecurity at the state level also cites perceived shortcomings, with articles characterizing state efforts as a “weak link” in the nation’s cybersecurity defenses and headlines like "State Cybersecurity Offices Need More Money and Staff." According to a survey of leading IT security officers in 50 states, “the top three issues impacting states’ cybersecurity remain the same from past surveys – budget, talent and increasing cyber threats.” The report (“States at Risk: A Bold Play for Change”) notes that nearly half of states do not have a separate cybersecurity budget and more than a third have seen no growth or a reduction in those budgets. However, an article in NewAmerica.org suggests that, because state-level cybersecurity agencies hold far more of their citizens’ information than does the federal government, and are arguably “more intimately connected to their citizens,” it is imperative that they have state-of-the-art cybersecurity practices.
Federal-Level Cybersecurity Overview
Several key federal agencies “play cross-cutting roles to support, monitor or oversee other agencies’ implementation of cybersecurity practices,” according to the Harvard/Belfer Center report. These include the Office of Management and Budget, the General Services Administration, the National Institute of Standards and Technology, and the Department of Homeland Security. “DHS, in particular, plays the primary day-to-day operational role in directing, assisting and engaging with agencies to implement federal cybersecurity measures.” Within DHS, the Cybersecurity and Infrastructure Security Agency (CISA) is responsible for “protecting the nation’s critical infrastructure from physical and cyber threats” — a mission that requires “effective coordination and collaboration among a broad spectrum of government and private sector organizations.” Part of CISA’s mandate is to “engage with the global cybersecurity community to strengthen the security and resiliency of the overall cyber ecosystems by addressing systemic challenges like increasingly global supply chains; by fostering improvements in international collaboration to deter malicious cyber actors and build capacity; by increasing research and development, and by improving our cyber workforce.” For information security enthusiasts and citizens alike, DHS offers an in-depth look at its overall “Cybersecurity Strategy” and its goals, as broken down into five pillars:
- Risk Identification
- Vulnerability Reduction
- Threat Reduction
- Consequence Mitigation
- Cybersecurity Outcomes
Despite the Department of Homeland Security’s ongoing vigilance, the fact that DHS itself was the victim of a high-profile data breach provides clear evidence that no one is immune to the ever-expanding threat of cyber treachery.
State-Level Cybersecurity Overview
State-level cybersecurity efforts also leave plenty of room for improvement. Recommendations included in the “States at Risk” report cited above include:
- Advocating for dedicated cyber funding on the state level
- Seeking funding and informational resources from federal agencies
- Working with the private sector and colleges/universities to develop sources of new talent
The Center for Internet and Society reports that, in addition to creating boards, commissions, task forces, working groups and related multi-agency and multi-disciplinary structures, states are also taking actions related to:
- Analysis and outreach
- Cyber incident response plans
- Grant programs targeting cyber vulnerabilities
- Readiness exercises and simulations
The need for states and cities alike to step up their cyber readiness is illustrated in incidents such as the 2017 Atlanta ransomware attack that cost an estimated $2.6 million. Though the city reportedly received help from both the FBI and DHS to recover, limited federal resources will not always permit a response to smaller-scale incidents, so states are under considerable pressure to develop their own robust cybersecurity capabilities
How the Cybersecurity Talent Shortage Affects State and Federal Readiness
As the cybercrime epidemic has escalated rapidly in recent years, government agencies and private sector companies alike have struggled to hire enough qualified professionals to safeguard against the growing threat. This trend is expected to continue, with some estimates indicating that there are some 1 million unfilled positions worldwide (potentially rising to 3.5 million by 2021, according to CybersecurityVentures.com). At the federal government level, this is resulted in a strong push to recruit the “best talent” to combat “rogue hackers, criminal organizations and nation-states,” according to a DHS cybersecurity recruitment video. The DHS and its CISA branch are recruiting professionals with the following skill sets:
- Cyber Incident Response
- Cyber Risk and Strategic Analysis
- Vulnerability Detection and Assessment
- Intelligence and Investigation
- Networks and Systems Engineering
- Digital Forensics and Forensics Analysis
- Software Assurance
“There’s not enough capability to go around,” CISA Director Chris Krebs said in a NextGov.com article about his efforts to rethink hiring methods and strategies. He expressed concern that as top talent gravitates toward the big tech companies rather than government service, “the rich are getting richer.” One potential pipeline for government cybersecurity talent is the U.S. military since many of the mission objectives and needed skill sets are closely aligned. In addition, many military IT professionals have already obtained security clearances. “Cybersecurity is a great way to continue serving our country, just on a different battlefield,” said Donald Greene, a 23-year Air Force veteran and cybersecurity expert with public and private sector experience, in one of the many articles touting cybersecurity as an option for veterans and military personnel. As part of its revamped cybersecurity hiring initiative, DHS has launched a Cyber Talent Management System that will enable it to speed up the hiring process, offer more competitive salaries and attract more people from nontraditional backgrounds. According to its most recent budget request, “DHS will hire at least 150 new cybersecurity employees using this system” by the end of FY 2020.
Federal vs. State Cybersecurity: Shared Challenges & Key Differences
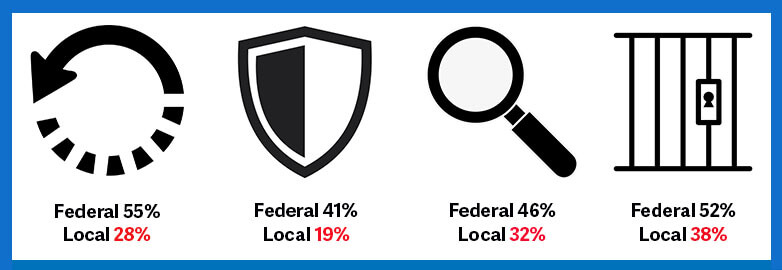
The shared challenges and differences between federal and state/local cybersecurity efforts were examined in a Ponemon Institute survey of nearly 850 IT security practitioners from agencies on both sides of the aisle. Some of the key findings include: Lack of Skilled Personnel The shortage is more severe at the state and local level, where 62 percent say this is a major challenge; 53 percent of federal respondents said lack of needed expertise is a disadvantage. Both groups see a lack of budgetary resources as an issue. Issues & Obstacles State and local respondents cited a need for stronger sharing of threat intelligence; federal concerns included organizational politics affecting their ability to achieve a stronger cybersecurity posture within their organizations. Top Threats Primary security threats cited by federal respondents: negligent insider followed by the zero-day attack and third party or contractor mistakes. Primary security threats cited by state and local agencies: failure to patch known vulnerabilities, negligent insiders and zero-day attacks. Perceptions of Preparedness Federal: 60 percent of respondents describe the maturity level of their organization’s cybersecurity program or activities as mature. State/local: 38 percent said their agencies have achieved that level of maturity in their cybersecurity initiatives. The study also cites four key areas where the federal government appears to be outpacing state and local agencies in terms of response capabilities when there is an attack:
- Ability to recover. Percentage rating their ability to recover from a cyber attack as very high: federal 55%, state/local 28%.
- Ability to prevent. Percentage rating their ability to prevent a cyber attack as very high: federal 41%; state/local 19%.
- Ability to quickly detect. Percentage rating their ability to quickly detect a cyber attack as very high: federal 46%; state/local 32%.
- Ability to contain. Percentage rating their ability to contain a cyber attack as very high: federal 52%; state/local 38%.
One of the key takeaways of the Harvard/Belfer Center report on the federal cybersecurity landscape also applies to state-level efforts—that there are “no silver bullets” and “no finish line,” that cybersecurity is by necessity “an enduring mission, always evolving and changing to stay ahead of the threat.”
About the Author: Michelle Moore, Ph.D., is academic director and adjunct professor for the University of San Diego’s innovative, online Master of Science in Cyber Security Operations and Leadership program, which is strongly committed to helping build America’s cybersecurity workforce. She is also a researcher, author and cybersecurity policy analyst with over two decades of private-sector and government experience as a cybersecurity expert. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

