
Kraken ransomware recently added the Fallout exploit kit as another means of reaching users and encrypting their information. Working with the Insikt group from Recorded Future, the McAfee Advanced Threat Research team found evidence that the authors of the ransomware had asked those behind Fallout to be added to the exploit kit. Fallout's developers apparently agreed to the proposition. At the end of September, the exploit kit began distributing Kraken in addition to GandCrab, a successful ransomware family for which researchers at Bitdefender released a decryption tool about a month later. At this current time, Kraken employs a ransomware-as-a-service (RaaS) business model. The first version of the threat reserved a quarter of the profits generated from attack campaigns for Kraken's developers. But that percentage dropped to a fifth in the second version, presumably in a bid to attract more affiliates. According to McAfee, the developers give affiliates an updated version of the ransomware every 15 days to ensure that their creation avoids detection. Affiliates then spread the ransomware with the help of Fallout and other vectors. Upon successful infection, Kraken quickly encrypts data on the disk and uses SDelete from the Sysinternals suite along with other tools to wipe files and complicate the recovery process for the user. It then drops a ransom note on the infected computer asking victims to send money to one of several wallets operated by the attackers through BitcoinPenguin, an online gambling site.
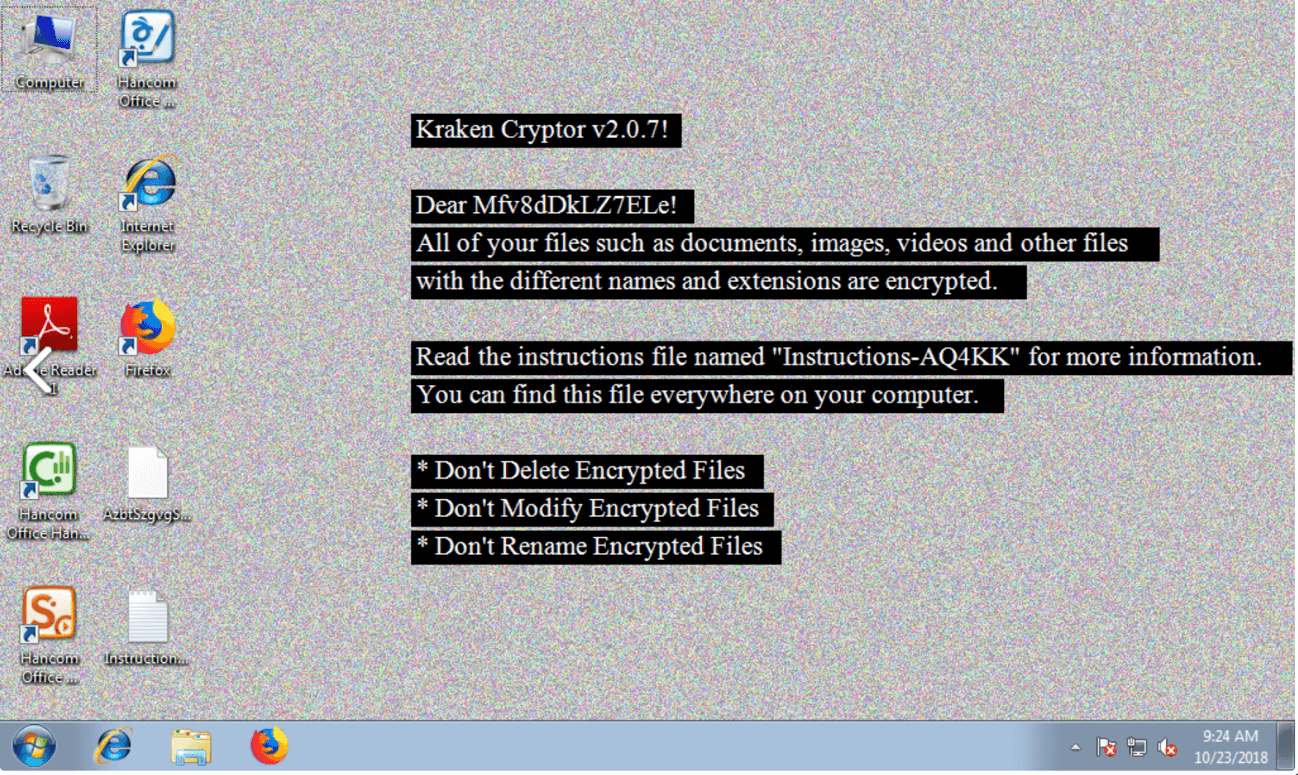
Kraken's ransom note (Source: McAfee) "After the victim pays the full ransom, the affiliate member sends a percentage of the received payment to the RaaS developers to get a decryptor key, which is forwarded to the victim," explains McAfee. "This system ensures the affiliate pays a percentage to the affiliate program and does not simply pocket the full amount. The cut for the developers offers them a relatively safe way of making a profit without exposing themselves to the risk of spreading ransomware." Given the profits involved in ransomware, not to mention the growing number of delivery mechanisms employed by Kraken and other families, it's important that organizations take steps to prevent a ransomware infection. User awareness training and prioritized patching are good places to start. For more ransomware prevention techniques, click here.

