
If there is one truth about today's threat landscape, it is that nothing remains the same. Such dynamism rests partially with the sheer volume of threats circulating the web. Multiple reports indicate that bad actors are developing as many if not more threats than security personnel have time to remediate. Indeed, in the second quarter of 2015 alone, the Spanish security firm Panda Security observed an average of 230,000 malware samples created each day. Trend Micro, another security firm, put this figure closer to one million. In their report, researchers with Panda Security explain that a majority of the new types of malware they observed were "mainly variants of previously known malware," which suggests bad actors are attempting to modify existing samples so as to evade detection by antivirus solutions. This observation does not come as a surprise. Malware authors are continuously trying to find new ways to bypass detection, to make money, and to gain access to sensitive data in new and creative ways. As such, bad actors frequently incorporate new techniques into their programs to refine the effectiveness and stealth of their products. Lastline, an advanced malware protection company, is well aware of the inventiveness of computer criminals. It is the job of its researchers to study malicious behavior on an ongoing basis with the hope of gaining insight into where malware development as an industry is heading. Looking back at 2015, Lastline observed three trends in the evolution of malware. Those are code signing, modified browser settings, and password guessing attacks.
Trend #1: Code Signing
Code signing via the use of digital signatures helps to establish trust between entities. As a result, malware authors commonly look to this practice as a way for their programs to evade detection by antivirus providers. That's not to say that obtaining the ability to sign an illegitimate piece of software is easy. On the contrary, there are several hurdles which malicious actors must overcome. First, they need to convince a Certification Authority (CA) to issue them with a valid certificate, a step which requires the CA to verify the identity of the company. This process could expose a certification candidate as a bad actor. Once they have been approved for a certificate, the malware authors must then agree to purchase the certificate knowing full well that it can be revoked at any time if any of their signed programs are found to be malicious. It is therefore perhaps unsurprising that while Lastline found an uptick in code signing, it did so primarily for potentially unwanted programs (PUPs), software that at best may annoy a user and at worst serve as a gateway for malware.
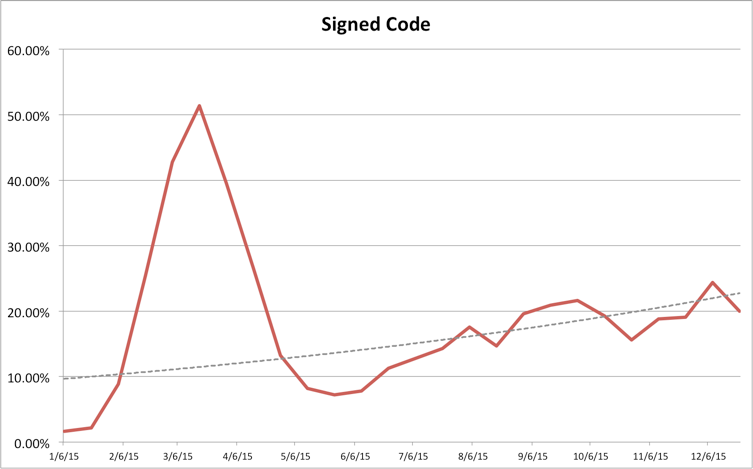
Figure 1: Fraction of signed malicious and suspicious samples (Source: Lastline) On the other hand, programs that were openly malicious demonstrated fewer instances of digital signatures, which no doubt reflects the challenge of a bad actor convincing a CA of its legitimacy. Lastline could not single out one CA in particular for signing malware. It found all popular, well known CAs to be affected.
Trend #2: Modified Browser Settings
Another trend in the evolution of malware observed last year was the practice of modifying browser settings. For all major browsers (Internet Explorer, Google Chrome, Firefox, Opera, and Safari), Lastline observed an increase in the number and fraction of malware that modified important and security-relevant modified browser settings as well as relevant Windows registry keys that influence the behaviors of these browsers.
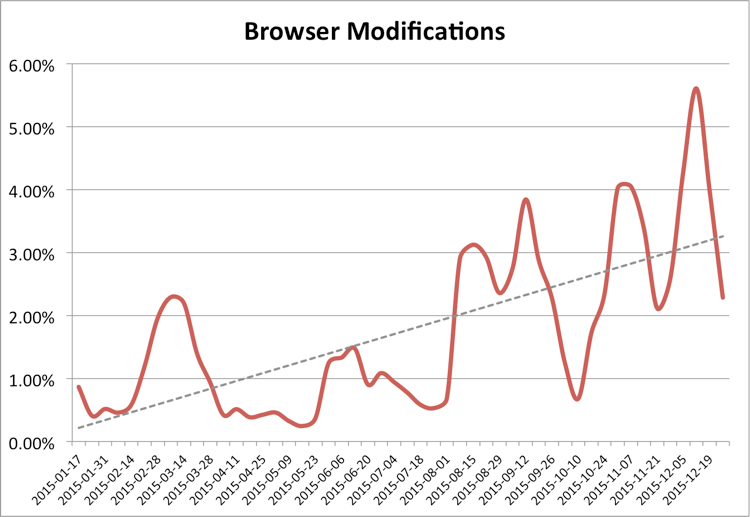
Figure 2: Fraction of samples that modify browser settings (Source: Lastline) A majority of the malware samples that went after victims' browsers specifically changed the proxy settings. This method of attack, especially the act of changing the AutoConfigURL registry setting in Internet Explorer, has been around since at least 2005 when Brazilian computer criminals began refining the use of PAC files for malicious purposes. Attackers in Turkey, Russia, and elsewhere can now employ malicious scripts that employ much of the creativity of drive-by campaigns to successfully, regularly, and silently impersonate HTTPS connections. Attackers have also been known to use certain malware, such as ProxyBack, to turn compromised systems into proxies without users' consent.
Trend #3: Password Guessing Attacks
For its final trend, Lastline picked up on a growing number of malware that use password guessing attacks. In these campaigns, the malware invokes an authentication procedure and uses common username and password combinations, including any of these weak passwords, in an attempt to gain access and then escalate local privileges.
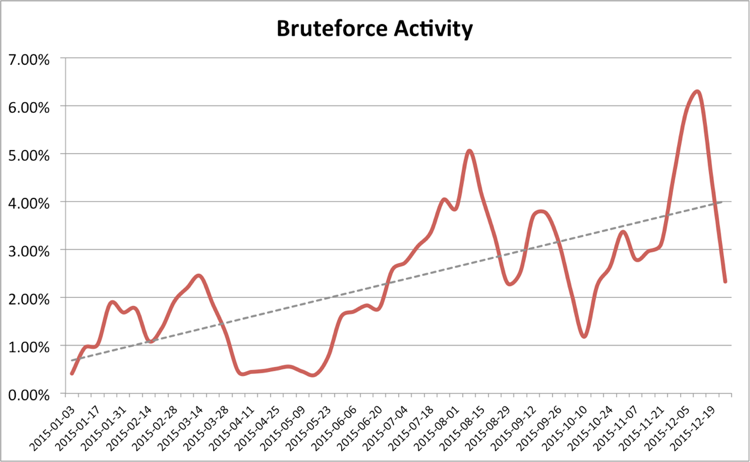
Figure 3: Fraction of samples that perform (password) brute force activity (Source: Lastline) Figure 3: Fraction of samples that perform (password) brute force activity It is important to note that password brute force attacks are neither new nor reserved for desktops only. Last summer, AppBugs conducted a study in which it found that 53 mobile apps were vulnerable to password guessing attacks. Those vulnerabilities placed upwards of 600 million users, both on Android and iOS, in danger of being hacked. Even so, the frequency of password brute force attacks is growing as a result of a number of developments. These include services being hardened against vulnerability exploitation and malware setting its sights on a growing list of targets, including Internet of Things products that are designed with little security in mind as well as out-of-date versions of content management systems like WordPress.
Conclusion
Lastline's analysis demonstrates that malware authors have improved their products significantly. By signing their code, bad actors can ensure their programs will evade most anti-virus solutions. This is especially true if their programs incorporate other evasive behaviors, such as dormant functionality. Malware samples can also modify a target systems' proxy settings to redirect all browser traffic through a machine that the attackers control as well as conduct brute force campaigns to escalate local privileges. With those trends in mind, it is more important than ever for security personnel to not only share information with one another but to also inspire the next generation of security professionals so that they can help check the rise of malware. For a list of conferences where you can connect with like-minded infosec individuals, click here. Title image courtesy of ShutterStock

