
In 1985, around the time that the Internet was just beginning to take shape, there were six top-level domains (TLDs) in existence. These were ".com", ".net", ".org", ".gov", ".mil", and ".edu". Along with some 100 country codes, those TLDs led the evolution of the web for over a decade. But then things changed. As the Internet continued to expand in size, TLDs started to diversify and increase in number. By 1998, websites with addresses ending in ".biz", ".info", ".telo", and ".jobs" began popping up. Fast-forward nearly 20 years later, and today we have over 1,000 TLDs, many of which have only been in existence for the past two years. The proliferation of TLDs is exciting for the future of the web. However, it also raises important questions about the extent to which those organizations charged with monitoring all of these top-level domains have sufficient resources and infrastructure to secure them against malware and other threats. With that concern in mind, security provider Blue Coat Systems Inc. has published Do Not Enter: Blue Coat Research Maps the Web's Shadiest Neighborhoods (pdf), a report which examines the most suspicious TLDs in existence today.
Shadiness on the Web
After analyzing web requests originating from 15,000 businesses and 75 million users, Blue Coat has put together the following list of the top 10 "shady" TLDs, which also includes the percentage of "shady" websites respective to each domain.
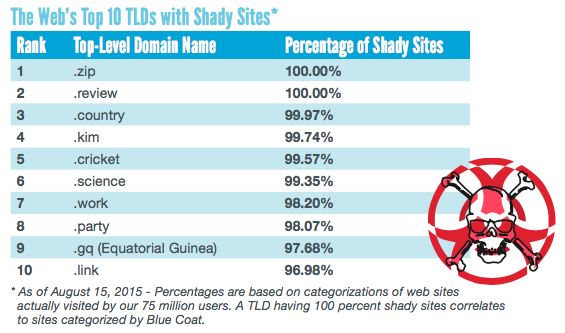
Source: Blue Coat To compile the above list, Blue Coat analyzed whether any web requests to a test site were flagged for spam, scams, suspicious activity (such as search engine optimization/poisoning), and/or potentially unwanted software. Malware, botnets, and other more serious threats were considered less common "shady" indicators for reasons that are at this time unclear. The extent to which these websites were found to exhibit "shady" behavior varied considerably. For instance, one website with a ".kim" address was built using obfuscated Javascript. Its pages mainly displayed image files and attempted to get users to install malware. Meanwhile, a website under the ".country" TLD hosted videos on a fake site that was meant to look like YouTube. Those videos could not be viewed unless a user liked or shared them or if they filled out a survey. The former resulted in spamming attacks directed against the user's Facebook friends list, whereas the latter could lead an unsuspecting user to potentially compromise their sensitive personal information. These are just two examples. The fact that over 95% of those 10 domains demonstrated "shady" behavior suggests that hundreds, thousands, or even tens of thousands of websites per domain may be engaging in suspicious activity. Some TLD managers have internalized Blue Coat's findings and are working to clean up the websites operating under their administration. This includes the organization behind the top-level domain ".xyz".
"We have agreed to start sharing some data back and forth with them, and I'm hopeful that will reduce the number of bad .xyz domains that show up," Chris Larsen, malware research team leader at Blue Coat, told CSO Online.
But not everyone appreciates Blue Coat's analysis. In a post published on Domain Incite, tech blogger Kevin Murphy condemns Blue Coat's study and its numbers as "bellocks."
"My main reason for this belief? Blue Coat has ranked .zip as '100% shady,'" Murphy explains. "This means that, according to the company, every single .zip domain its customers have visited is either spam, malware, a scam, a botnet, suspicious, phishing or potentially unwanted software. The problem is that the entire .zip zone file currently consists of precisely one (1) domain. That domain is nic.zip, and it belongs to Google Registry. This is a pre-launch TLD. As far as I can tell, Google Registry is not involved in distributing malware, spam, phishing, etc."
Blue Coat has since responded to Murphy's critique in a post of its own, in which it notes, among other things, how ".zip" URLs are showing up in its traffic logs mainly as filenames that are being treated as URLs in someone's browser.
"We have nothing against Google, we don't mean to imply that they're running a shady operation. This is just all about the unintended consequences of having .zip as a TLD," Hugh Thompson, Blue Coat's Chief Technology Officer, told Reuters.
Mapping the Safe Neighborhoods
"Shady" behavior is not the only element documented in Blue Coat's analysis. The security provider also compiled a list of the top 10 safest TLDs, which also comes with percentage values of "shady" websites found in each domain.
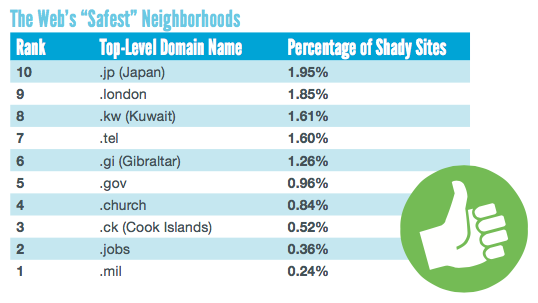
Source: Blue Coat These findings are instructive, but they can be misleading. As Blue Coat rightly notes, only 100 websites are currently found under the ".london" TLD, and plenty of small churches that may or may not operate under ".church" have been successfully hacked by ISIS and by other malicious actors. Ultimately, the "safe" TLDs distinguish themselves by instituting guidelines that regulate the purchase of individual websites.
"On some of the good ones, there is usually a set of qualifications to be able to buy a domain. It's not just being able to have a valid credit card that can you charge $18 bucks on and you buy one of these domains," Thompson told CBS News. "The average person off the street can't go and buy a .mil domain. You have to be associated with the government. The registrar that controls that has a bunch of criteria on who you have to be. As a result of that, it's an incredibly safe TLD."
Other TLDs, such as ".sucks", require a $2,000 annual registration fee, a cost which likely prices many scammers out of the market.
Conclusion
Businesses that are looking to protect themselves against "shady" TLDs should consider blocking traffic from any domains listed in Blue Coat's analysis. Meanwhile, users should exercise caution should they come into contact with one of the suspicious TLDs in an email or web search results page. Users should also make sure that unknown links do not lead to a website operating under a "shady" top-level domain either by hovering their cursor over the URL in question or by pressing and holding down on the URL on their mobile device. Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

