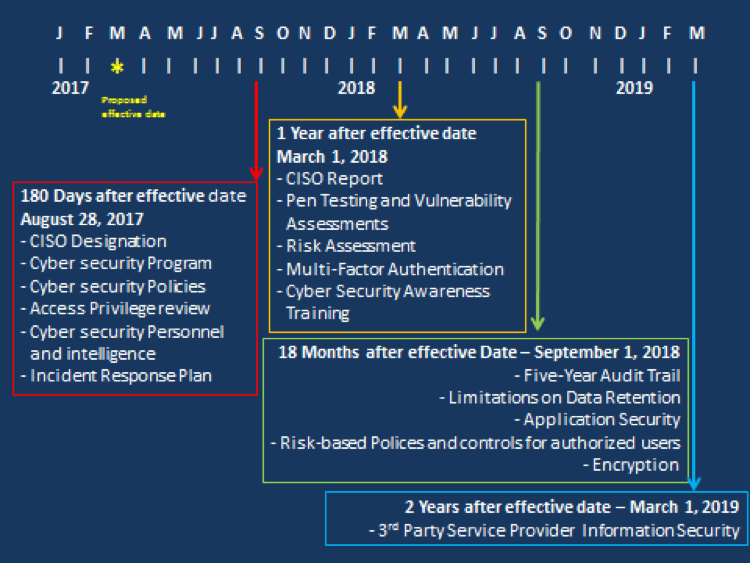
In part 1 and part 2 of this series, I reviewed some of the administrative and technical evolution of the cybersecurity legislation that has been proposed for all financial entities in New York State. As I started to write this, the final regulation was adopted. The good news is that most of the changes that were proposed in the first revision have remained in place, so this little exploration is still valid. It has been interesting to see how a regulation changes from its original form to its adopted resolution. One of the more noticeable developments in the regulation is the treatment in respect to Third Party Service Providers. In the original proposal, the regulation sought to protect a covered entity by requiring risk assessments for third parties who have access to sensitive data. It also required multi-factor authentication and the use of encryption for all third parties that handle sensitive data for the covered entity. (In case you missed it, the “Covered entity” is any business operating under the New York State Banking, Insurance, or Financial Services law.) The original proposal did not define what a “Third Party” was. This has been remedied in the revisions. In a breathtaking oversight, the requirement for multi-factor authentication for third party service providers has also been relaxed; it is no longer a requirement. It is as if nothing was learned when that big department store was breached via the access that their third party HVAC vendor had into their system. Infosec professionals have known the value of the “pivot attack” for many years. It is well-understood that multi-factor authentication would have prevented many of the breaches that have taken place in recent years. I have intentionally omitted an exploration of various sections of the new regulation. Items such as the requirements for an incident response plan, as well as application security and the prescriptive requirements for notices to the Superintendent are all clearly defined in the regulation. I hope that this evolutionary analysis has sparked your interest in reading the full regulation with an understanding of its original requirements and how it evolved over each of the 45-day comment periods that were offered to the public prior to the final regulation was adopted. Perhaps, as infosec professionals, this exploration will encourage participation as part of that process to express our concerns and shape future regulations. We can use our unique knowledge and our voice to shape policy. I am certain that there will be many webcasts and further articles covering all aspects of this new regulation, and it is widely believed that this regulation in New York State will be the template upon which other states will soon enact their own cyber security regulations. You can find the new regulation here (PDF). In order to assist you with the deadlines prescribed in the new regulation, I have also created the following graphic to let you mark your calendar for the milestones found within the regulation.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.