
The post office email scam is a time-tested method of attack among malicious actors. Indeed, when users see that they have received an email from an actor purporting to be their local post office, most of them buy into the familiarity of this governmental institution and click on a link without taking the time to inspect the sender address. Attackers further exploit users' implicit trust by targeting victims based upon their nationality and using the correct language and visual elements to trigger action, as did scammers with Royal Mail in the UK this past summer. But as with most threats today, the post office email scam is evolving. Researchers at the financial and data protection firm Heimdal Security have spotted a group of scammers who are using a post office scam to deliver Cryptolocker2 (also known as "crypt0l0cker") ransomware onto Danish users' computers.
How a Post Office Scam Works, and What's Different Now
A post office scam generally proceeds as follows:
- An unsuspecting user receives what appears to be a legitimate email from a nearby post office informing them that a postman attempted to deliver a package to their place of residence but that no one was home. The email goes on to encourage the user to click on a link, which they can use to schedule a time where they can go to the post office to receive the undelivered package.
- Upon clicking the link, the user is redirected to a website that pushes an automatic download consisting of an executable file onto their computer. This file may then infect several of the victim's files or silently collect and transmit information, including passwords and financial information, back to the attacker(s).
The scam observed by Heimdal, as noted in a blog post, generally adheres to the procedure described above. Emails purporting to be from Post Denmark and PostNord lure Danish users to click on a link. In this case, however, the website to which they are redirected loads not a simple malware variant but Cryptolocker2, a form of ransomware that according to researchers employs the same infrastructure as Shylock malware and ZeuS GameOver, the latter of which was taken down last year as part of an international legal effort.
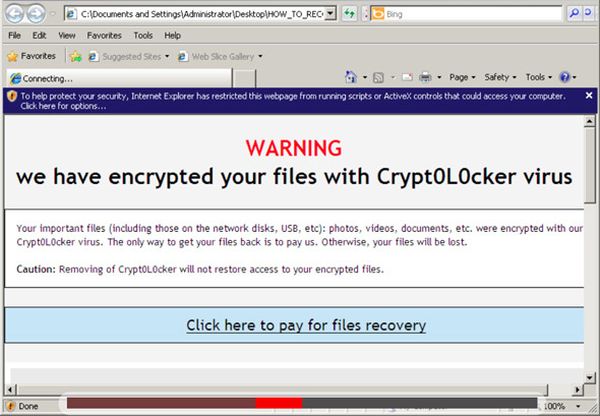
Source: Heimdal Security Also known as "crypt0l0cker", Cryptolocker2 copies itself to a Windows folder with a random filename, at which point it connects to a Russian server with the IP address 109 120 [.] 155,159 by injecting itself into the explorer.exe process. This server is translated via DNS from the domains ejkoesc [.] net, oroxwey [.] com, and mqweodhy [.] com. The ransomware then encrypts all of the locally stored data as well as the data available on network-connected devices. Finally, it creates a "HOW_TO_RECOVER_FILES.html" file that the victim can use to receive instructions regarding how to pay the attackers for the decryption keys. Once crypt0l0cker has successfully infected a machine, it employs a number of techniques to make sure it stays that way. For example, the advanced malware runs "HKEY_LOCAL_MACHINE \ SOFTWARE \ Microsoft \ Windows CurrentVersion \ \ Run agukelub" to make sure that a system reboot does not remove it from the hard drive, and it removes any anti-phishing tools that might be installed on the computer. Even in the event that an anti-malware scanner is still active, the ransomware uses a variety of evasion tactics, including anti-debugging and sandbox actions as well as a right-escalation method to force access to windows through injection. The attackers build onto this impressive anti-detection arsenal by using multiple hosting providers for the malware and their websites throughout Europe, equipping Cryptolocker2 with a domain-generating algorithm (DGA), and having the malware redirect to Google's homepage whenever any attempts are made to replicate the infection process, as is common for reverse engineers to do. As of this writing, this threat has a low detection rating at 2/56 on VirusTotal. A sister post office scam campaign also spotted by Heimdal that redirects user to Denmark-portal24 [.] com, where a file named “forsendelse.zip -> forsendelse.exe (in Swedish “Forsandelse.exe “) is downloaded, scored even lower on VirusTotal at 1/56.
Conclusion
Andra Zaharia, Marketing & Communication Specialist at Heimdal Security, rightly points out that users need to be informed if they hope to adequately protect themselves against crtypo-ransomware like Cryptolocker2.
"There are too many Internet users who are unaware of the dangers of Cryptoware and that’s exactly what makes it so dangerous," Zaharia said. "There’s no telling what country cyber criminals will set their eyes next, but it could be yours, so you need to be prepared to handle a cyber attack, not just in terms of tools, but also in terms of knowledge (that will help you choose the right tools and course of action)."
Internet users can protect themselves against these types of threats by installing anti-virus software on their systems, adding additional layers of security that are capable of detecting advanced malware onto their machines, and using two methods to backup their data (in the cloud and on an external hard drive). To learn more about ransomware, including how you can avoid becoming a victim, please click here. Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

