
Earlier this month, several media outlets ran a story claiming that a new type of malware could be used to destroy victims’ computers. These stories might have fared well in views, but their fear, uncertainty, and doubt (FUD) have proven useful to no one. Fortunately, a number of security experts including Graham Cluley were quick to correct the false impressions these articles created, allowing us to explore the threat, known as ‘Rombertik,’ in earnest. Tripwire recognizes Rombertik as an intriguing sample of malware because of its anti-analysis behavior. We will now scrutinize the threat by exploring how it implements each of the four most common evasive techniques used by malware: environmental awareness, confusing automated tools, timing-based evasion, and obfuscating internal data.
-
Environmental Awareness
The first type of evasive behavior, environmental awareness, refers to the capability of a malware sample, including Rombertik, to analyze the conditions of the system it is trying to infect. Earlier this month, Talos Security Group threat researchers Ben Baker and Alex Chiu published a report on Rombertik’s evasive behavior. Their findings reveal, among other things, that the malware implements a series of checks to determine whether it is running within a sandbox. Upon execution, Rombertik initiates one round of checks before installing itself on a victim’s computer. It then launches a second copy of itself, which is overwritten by the malware’s core functionality. Before the malware activates, however, it executes another round of checks to see yet again whether it is running in memory. If this last safeguard fails, the malware attempts to overwrite the Master Boot Record (MBR) and restart the computer, effectively rendering the computer unusable. Ultimately, it is Rombertik’s ability to overwrite the MBR that fueled the speculative articles to which we refer above. But even then, there is more to this defensive measure than meets the eye. Indeed, a few weeks after the publication of Cisco’s report, security firm Symantec published a post on its Security Response blog in which it explains how Rombertik is actually a newer version of an underground crimeware kit called Carbon FormGrabber. In this view, Rombertik’s ability to overwrite the MBR likely functions less as a countermeasure against security professionals and more as a deterrent to less experienced attackers who might be seeking to alter the malware’s code and make it do something for which it was not originally licensed. As an added safeguard, Rombertik injects itself into its victims’ browsers to help conceal itself. The malware then constantly scans for running browsers to hook, as explained by Joe Giron, a security researcher for Lastline Labs. In the event Rombertik does identify that the browser-memory already contains a hook, which may be due to the work of a sandbox, it will skip revealing its payload.
-
Confusing Automated Tools
Malware also make use of confusing automated tools in an effort to evade detection. With respect to Rombertik, the threat writes a byte of random data to memory approximately 960 million times. This technique confuses sandboxes. As they cannot determine whether it is stalling because the malware is not sleeping, most sandboxes eventually time out their analysis before Rombertik begins to exhibit any malicious behavior. Additionally, these stalling loops flood all tracing tools with log entries, which further complicates the analysis process even when malicious behavior is evident.
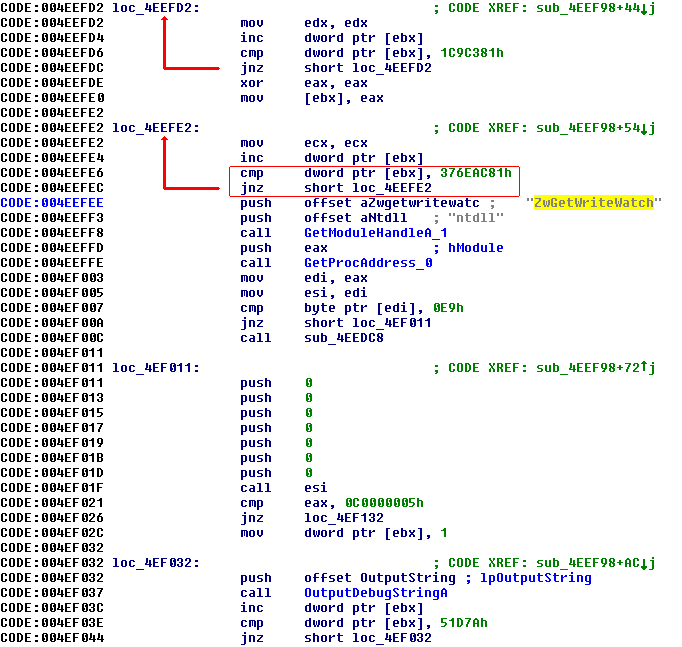
Source: Lastline Rombertik’s use of stalling code is a testament to how malicious tactics have evolved in tandem with the countermeasures employed by security personnel. As Lastline explains in a white paper, one of the first evasive techniques embraced by malware was code obfuscation and encryption. This tactic prompted AV companies to adopt dynamic analysis, which, in turn, gave rise to attackers designing malware with environmental awareness in mind. Once again, security researchers responded by analyzing the differences in how malicious code runs in virtual and real environments, an evolution which brings us to our current phase in which malware authors incorporate stalling code as a means to shut out this analysis. Clearly, Rombertik is at the forefront of malware-interested communities to the extent that it makes use of this latest innovation.
-
Timing-Based Evasion
Timing-based evasion is probably the least evident technique in Rombertik’s behavior. According to Symantec, the malware writes the file “%SystemDrive%\Documents and Settings\All Users\Start Menu\Programs\Startup\[RANDOM CHARACTERS].vbs,” which ensures that its code will run every time Windows starts up. But not much is known beyond that, as most analyses have focused on Rombertik’s other evasive attributes.
-
Obfuscating Internal Data
The fourth and final evasive technique commonly employed by malware is confusing automated tools. Here Rombertik makes use of garbage code to help conceal its most significant functions. In fact, Baker and Chiu found that about 97 percent of the packed file consisted of 75 images and approximately 8,000 functions that are never called. This tactic allows the malware authors to conceal much of the core Rombertik file, which is only 28KB in size, thereby making it difficult for analysts and automated tools to examine each and every function.
Conclusion
Given its ability to overwrite the MBR under certain circumstances, its use of both garbage and stalling code, and its initialization every time Windows starts up, we at Tripwire can only conclude that Rombertik is a master of evasion. But by no means does that mean that its evasion techniques are infallible. Researchers at Symantec discovered a location of an RSA public key that allows researchers to avoid triggering Rombertik into wiping the MBR. Additionally, while analyzing the malware, Lastline’s sandbox went undetected by Rombertik. These are both promising developments. Malware may be evolving with regards to its use of evasive behavior, but the security industry is keeping pace. Every day, security researchers devise new countermeasures to meet these emergent threats, and every day, online users reap the benefits by enjoying additional protection and security.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

