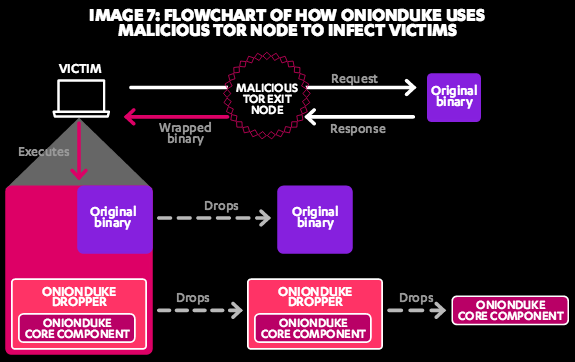
Finnish security and privacy company F-Secure recently published a white paper exploring the activities of 'The Dukes,' a group of hackers that has been targeting Western-based governments think tanks, and other organizations for at least the past seven years. According to F-Secure's research, the group is known primarily for its use of advanced, often noisy spear-phishing campaigns as means to infect their victims with malware. In most cases, the Dukes practice 'smash and grab' tactics before breaking in and exfiltrating data. However, for more valuable targets, the group has been known to engage in stealthier tactics. Most of the Dukes' attacks involve the use of either a specially crafted malicious email attachment designed to exploit a vulnerability in a software program running on the victim's machine, such as Microsoft Word or Adobe Reader, or a URL where any one of its malicious toolsets are hosted. These infection vectors are usually accompanied by a decoy image, video, or even fake voicemail, which is meant to distract the victim during the infection process. For close to a decade, the group has been leveraging at least nine different malware toolsets: MiniDuke, CosmicDuke, OnionDuke, CozyDuke, CloudDuke, SeaDuke, HammerDuke, PinchDuke, and GeminiDuke. At times, the Dukes have conducted several malware campaigns simultaneously. In 2012, for instance, operations involving CosmicDuke, MiniDuke, GeminiDuke, and CozyDuke were all concurrently active to different extents. (The group during that period favored CosmicDuke and MiniDuke over the others.) This ability to conduct multiple malware campaigns at once suggests that the Dukes have significant and stable financial backing, resources which F-Secure believes are possibly (but not conclusively) provided by the Russian Federation. The group's vast arsenal of malware has also evolved over its seven years of use. For example, though the Dukes began with PinchDuke in an effort to target the Georgian Ministry of Defense, a U.S. think tank, and NATO in 2008 and 2009, it replaced that malware toolset some two years later with the infostealer CosmicDuke, which eventually incorporated an embedded version of PinchDuke into its code and acquired the ability to load both malicious tools upon infection onto a victim's machine. Similarly, as MiniDuke slowed down in 2013, the group replaced it with OnionDuke, a bad Tor exit relay that creates torrent files containing trojanized applications and uploads them to websites that contain torrent files.
All of this activity has naturally alerted security firms to the ongoing work of this threat group. Both Kaspersky Lab and CrySys, for example, detected MiniDuke in the fall of 2013, whereas CosmicDuke was outed by F-Secure and Kaspersky a few months later. In both cases, however, the authors of the malware toolsets quickly made a series of improvements, sometimes in a matter of days. As F-Secure has explained, these fixes were likely meant to protect the malware against detection, especially after the group had invested significant resources into each one of their targeted attacks. F-Secure has spent a considerable amount of time compiling its research on this particular threat actor:
"While we had previously analyzed malware from both toolsets, what we hadn’t understood at the time was their context," the security firm explains. "With the discovery of new clues such as these two toolsets, we went rummaging through our troves of old malware searching for cases that we had previously not known to attribute to the Dukes. Through this process of proverbial connect-the-dots, we were able to slowly build a bigger, better picture of the Dukes and uncover new details of their over 7 years of activities."
Clearly, the Dukes are an extremely capable advanced persistent threat group, and the continued use of CozyDuke, CloudDuke, SeaDuke, and HammerDuke this year alone illustrates that this actor's malware campaigns are unlikely to subside anytime soon. To learn more about the Dukes, please read F-Secure's report here. Title image courtesy of ShutterStock

