
In February of 2015, researchers at Kaspersky Lab disclosed the existence of a sophisticated cyber-attack group that's been in operation since early 2001, and targeted almost every industry and foreign countries with its zero-day malware. Kaspersky called this threat actor the Equation Group because of its love for encryption algorithms and the sophisticated methods used in its operations. The Equation Group employs advanced hacking tools that required significant effort to develop.
The Equation Group tight with Stuxnet, links to NSA
The Equation Group is a threat actor that has engaged in various CNE (Computer Network Exploitation) campaigns around the world. It uses multiple malware platforms, which surpasses the famous Regin malware (intelligence-gathering advanced malware for the NSA) in complexity and sophistication. The group uses RC5 encryption algorithm throughout its malware, many of which can infect hard drive firmware using an HDD firmware reprogramming plugin that provides API into hidden sectors. That technique makes the group's malware attacks extremely persistent to disk format and OS reinstalls.
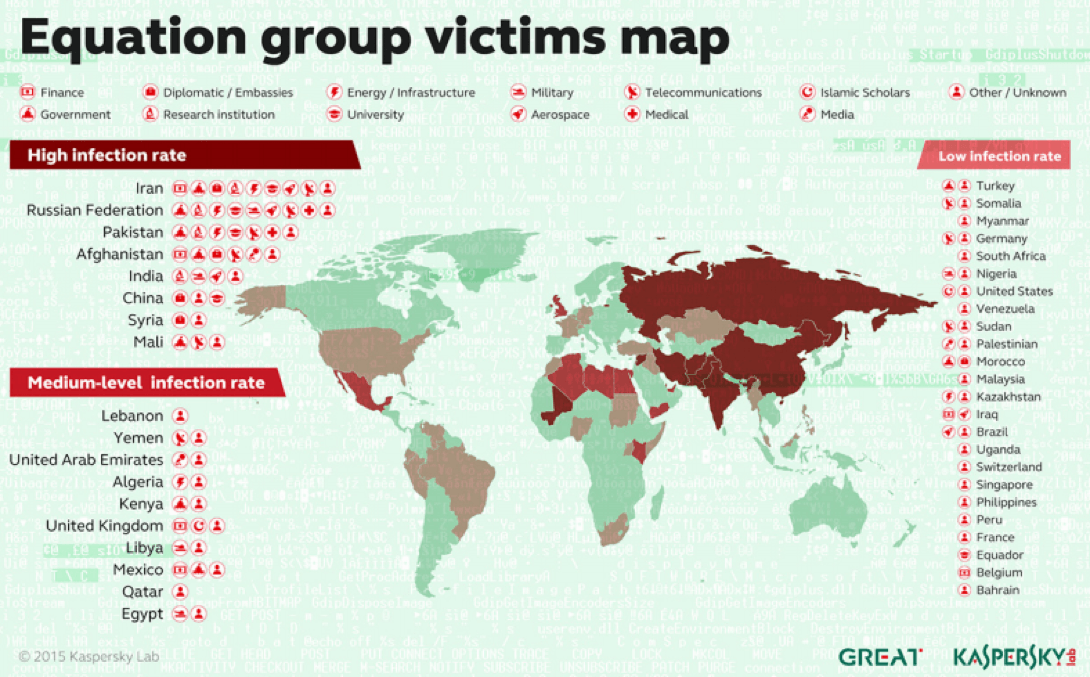
The Equation Group has targeted victims in more than 30 countries. (Source: Kaspersky Lab) Kaspersky's experts speculated that the group interacted with the operators behind Flame and Stuxnet and that it is linked to the National Security Agency (NSA).
Shadow Brokers Group leaked ATP group’s hacking tools: First auction
Earlier this year, another threat actor or a hacking group calling itself the Shadow Brokers claimed to have hacked one of the NSA's servers belonging to the Equation Group and stolen some hacking tools. According to The Intercept, there was a classified NSA internal agency manual that helps guide NSA operators in their efforts to track hacking tools with a 16-character string, “ace02468bdf13579.” The same string was used in one of the leaked hacking tools called SECONDDATE, thereby helping to prove the legitimacy of the data dump. SECONDDATE is considered one of the most notorious hacking tools available today. It is used in combination with TURBINE and BADDECISION exploits.
Analysis of first leaked archives
Kaspersky Lab's experts published a detailed analysis of the leaked data dump suggesting that the material does indeed belong to the Equation Group. For their leak, the Shadow Brokers provided links for two different PGP-encrypted archives. The first archive was available for free, but the second archive was auctioned for 1 million Bitcoins (approx. $578 Million). The free archive contained roughly 300 MBs of material including hacking tools, firewall exploits, and scripts with cryptonyms such as BLATSTING, BANANAUSURPER, and BUZZDIRECTION. Those exploits targeted firewall products by Cisco, Juniper, Fortigate, Watchguard, and TopSec. In response, the security researcher Mustafa Al-Bassam published a blog post that listed all the exploits, tools, and implants for hacking firewalls included in the archive. That post helped firewall vendors to discover the previously unknown vulnerabilities and patch them.
Shadow Brokers leaked yet another dump, revealing NSA targets: Start of crowd funding
After the Shadow Brokers group failed in its auction, it announced it would release the remaining dump once it raises 10,000 BTC in crowd funding. However, with the current situation of only 2 BTC, it seems unlikely that the group will succeed in its plan. With its announcement, the Shadow Brokers group leaked another batch of archives that contained the details of IP addresses and compromised servers used by the Equation Group to conduct their hacking operations. The researcher Mustafa Al-Bassam shared the list on his Twitter account. The detailed analysis of the new leaked files by Hacker House shows that the files in the archives date back between 2000 and 2010, and some of the compromised servers are still active and infected with undisclosed tools in the latest leaks. Some of the previously undisclosed tools include DEWDROP, JACKLADDER, INCISION, PATCHICCILIN, SIDETRACK, ORANGUTAN, STOICSURGEON, and RETICULUM. Other tools, which are referred to as "redirectors" by the Shadow Brokers, are named INTONATION and PITCHIMPAIR. However, it is noticeable that the names align with the conventions used in NSA's ANT catalog. The experts analyzed the files and confirmed 352 IP addresses and 306 compromised domain names including 32 .edu, and 9 .gov domains across 49 countries, with most targets in Asia Pacific. The affected countries include Germany, Spain, Japan, India, Taiwan, Mexico, Italy, Korea, China, and Russia. The motive of the Shadow Group is clear: they are looking to monetize from the Equation Group archives. However, the experts say the archives are not as valuable as the group thinks. It is not clear who's the curator of the Shadow Broker group. Popular theories are that either it is the Russian government, an NSA insider, or some opportunistic hacker who successfully breached the NSA's server. The linguistic experts from Taia Global strongly believe that the group's people are native English speakers who are trying to appear non-native. The latest messages by the groups seem to support the theory. Although the Equation Group allegedly used the disclosed malware to attack high-profile targets, intelligence surveillance efforts affect us all. Organizations should, therefore, consider security as a crucial factor in their infrastructure, and they should work to mitigate the risks of exposing their systems to attackers. Users should also take seriously the security measures of their devices, especially IoT products, and install security software to prevent future attacks.

About the Author: Shiraz Hashmi is a scholar of Information Security discipline. He is passionate about writing and learning latest trends in technology and other fields of interest. You can reach Shiraz Hashmi on Twitter. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

