The digital world is riddled with threat actors of which we know very little. Some of these mysterious agents launch one or two modest attacks and peter out soon after crawling their way into existence. Others last a bit longer, raising hubbub and gaining notoriety in the process. Not a lot of actors make it into the latter category without the security community learning a lot about them. But it does happen from time to time. One such group has been around for several months, and it's still making headlines…though not for much longer.
Brokering in Disappointment
In August 2016, the world first learned of the Shadow Brokers when it announced an auction of hacking tools. The threat actor claims it procured those utilities from the Equation Group, a malicious entity which has engaged in computer network exploitation (CNE) around the world. Little is known about the Equation Group. But many in the security community speculate the hacking group conducts digital espionage at the behest of the National Security Agency (NSA). Not surprisingly, Shadow Brokers raised a lot of eyebrows when it said it had hacked the NSA. But the proof was in the details. As reported by The Intercept, one of the leaked hacking tools contained a random 16-character string that the NSA uses to keep track of its CNE implements. This discovery helped prove the legitimacy of the data dump. Notwithstanding their authenticity, the leaked hacking tools didn't generate as much interest as that for which the group had been hoping. Shadow Brokers originally set a desired bid amount of one million Bitcoin (approximately 560 million USD at the time) for the entire dump. When the auction raised only a fraction of a fraction of that amount, the threat actor said they would release the remaining files once they received 10,000 BTC in their Bitcoin wallet. In the meantime, the group decided to begin selling off the tools piecemeal for amounts ranging from one Bitcoin to 100 BTC. It also released another batch of leaked files that contained details of IP addresses and compromised servers used by the Equation Group. To learn more about the hacking tools included in the Shadow Brokers' inaugural data dump, please read Kaspersky Lab's analysis here.
A Leak of Windows Hacking Tools
It was a disappointing first run for the Shadow Brokers. But it's still confident it can make a profit from its hack of the Equation Group. That explains why the threat actor has ushered in 2017 with another sale. https://twitter.com/shadowbrokerss/status/817961045033709570?lang=en This time, the Shadow Brokers is trying to auction off a database of hacking tools developed by the Equation Group and designed solely for the Windows platform. The group is asking 750 Bitcoins (607,500 USD) for what it's calling "Window Warez." It's also willing to sell off the tools piecemeal for prices ranging in value from 10 Bitcoin to 250 Bitcoin. Screenshots of the sale (as included in the threat actor's tweet) provide some insight into the advertised hacking wares. For instance, it appears Shadow Brokers has in its possession a tool that's capable of editing and tampering with Windows event logs. Attackers could use this tool to prevent incident response teams from finding out what happened in the event of a breach or targeted attack. Jacob Williams, founder of Rendition InfoSec, is well-aware of the dangers posed by this type of tool. As he told Dark Reading:
"Knowing that some attackers apparently have the ability to edit event logs can be a game changer for an investigation. If Shadow Brokers release this code to the world (as they've done previously), it will undermine the reliability of event logs in forensic investigations."
Williams goes on to an explain in a blog post that one of the offerings called "PSP_Avoidance" is capable of evading detection from anti-virus solutions designed by Avast, Avira, Comodo, Dr. Web, Kaspersky, McAfee, Microsoft, Symantec, and others. In that sense, it jeopardizes the security of computer users everywhere.
The Sun Sets on Shadow Brokers
Shadow Brokers put up their Window Warez sale on 8 January 2017. But less than a week later, the threat actor announced it's time to say goodbye. In a message posted to its website on 12 January, the group says it was always about the money and that it will be "going dark" until its Bitcoin wallet receives 10,000 BTC for the original leak.
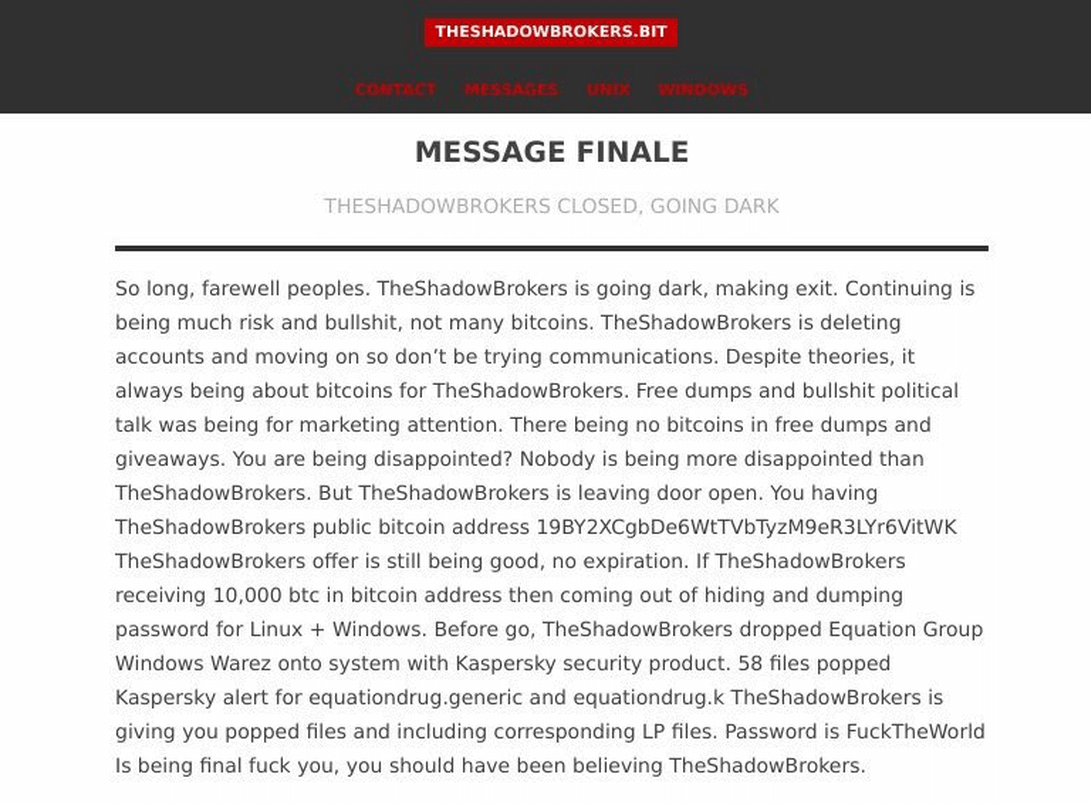
Source: Heimdal Security As quoted by Heimdal Security:
"So long, farewell peoples. TheShadowBrokers is going dark, making exit. Continuing is being much risk and bulls**t, not many bitcoins. TheShadowBrokers is deleting accounts and moving on so don't be trying communications. Despite theories, it always being about bitcoins for TheShadowBrokers. Free dumps and bullshit political talk was being for marketing attention. There being no bitcoins in free dumps and giveaways. You are being disappointed? Nobody is being more disappointed than TheShadowBrokers. But TheShadowBrokers is leaving door open. You having TheShadowBrokers public bitcoin address 19BY2XCgbDe6WtTVbTyzM9eR3LYr6VitWK. TheShadowBrokers offer is still being good, no expiration. If TheShadowBrokers receiving 10,000 btc in bitcoin address then coming out of hiding and dumping password for Linux + Windows. [censorship added]"
Before it turns out the lights, The Shadow Brokers released an archive of 58 Windows hacking tools to the public that are detected by Kaspersky Lab products. Maybe they're hoping that leak will help them sell the Window Warez haul for 750 BTC and the original Equation Group dump for 10,000 BTC. Let's hope the threat actor never comes close to raising that amount and instead fades into oblivion.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

