
On September 20, 2016, the Mirai botnet temporarily brought down Brian Krebs' information security blog KrebsonSecurity.com. It did so by launching a distributed denial-of-service (DDoS) campaign, the attack traffic of which peaked at approximately 620 Gbps in size – one of the largest DDoS offensives the Internet has ever seen. A week or two later, researchers confirmed what they had suspected all along: Mirai had amassed its power by enlisting hundreds of thousands of vulnerable Internet of Things (IoT) devices protected by default login credentials. Mirai might be the latest (not the first) botnet that's exploited IoT for malicious purposes, though it's certainly not the only infected network that's on researchers' minds. Take Andromeda, for instance. With its discovery dating back to late-2011, Andromeda is one of the longest running botnets in existence today. It's made a name for itself by preying upon unsuspecting users with malware like GamaPOS and the Odinaff trojan. But don't be fooled. Age doesn't imply antiquation. Like any sophisticated malware family, Andromeda is constantly incorporating new malicious executables to maximize its distribution. One such new arrival burst onto the scene in October 2016. Here's a little bit about it. The malware, which belongs to the Sarvdap family, attempts to connect to www.microsoft.com after checking for a debugger, allocating memory for itself, and completing a number of other initialization tasks. Assuming it successfully establishes that connection, Sarvdap does something most other malware samples don't. Brandon Levene and Brandon Young of Palo Alto Networks' Unit 42 research team explain:
"This malware is interesting because it contains a hardcoded list of commonly known blacklist servers. These servers are used as a means to check the infected host/zombie to determine if this infection is live and not on any of the provided blacklists. The blacklists checked are from all around the world and rather comprehensive, indicating the author was trying to get global coverage rather than that of a specific region."
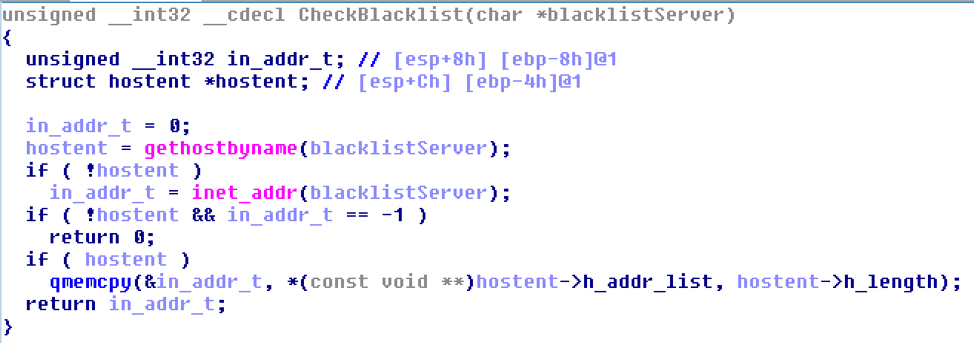
Sarvdap does something most other malware samples don't. (Source: Palo Alto Networks) In the event Sarvdap finds the IP on one of the blacklists, it returns the hostname (that is, IP+BlacklistAddress) instead of an IP address. Otherwise, it sends over S5R: %u: OK, with the %u argument representing the current blacklist server that's being checked, to its command and control (C&C) server. The malware doesn't want to waste its time sending spam mail from an IP address that's blacklisted, for security solutions will automatically block its efforts. That's why it terminates if it finds a match with a blacklisted host. Sarvdap expects to download and read a configuration file if the host passes the blacklist checks. At this time, it's not known what that file contains, as the server was offline when Levene and Young analyzed the malware. Even so, the duo knows the malware is capable of delivering pharmaceutical spam and the main Andromeda bot, which makes the Sarvdap spambot particularly menacing. As they note in their blog post:
"Phishing emails remain a highly prevalent threat for enterprise, government and home users. For-hire, large-scale spam focused botnets continue to churn out hundreds of thousands of messages a day from compromised hosts. Sarvdap is particularly interesting not due to its scale, but rather due to its attempts to increase overall spam delivery by abusing reputation blacklists."
It's important that users make an effort to protect themselves against Sarvdap and additional malware pushed out by the Andromeda botnet. They can do so by maintaining an up-to-date anti-virus solution on their computers and exercising caution around suspicious links and email attachments. At the same time, organizations can take it one step further by deploying an advanced malware protection solution that monitors their endpoints for unauthorized changes.

