
Ashley Madison, a website for those who are interested in committing adultery, has made headline after headline in recent weeks after a hacking group penetrated its servers and published the information of all 37 million users online. As of this writing, it is believed that this incident dates back to mid-July of 2015. The timeline below recounts all of the major developments of this ongoing breach.
July 19, 2015
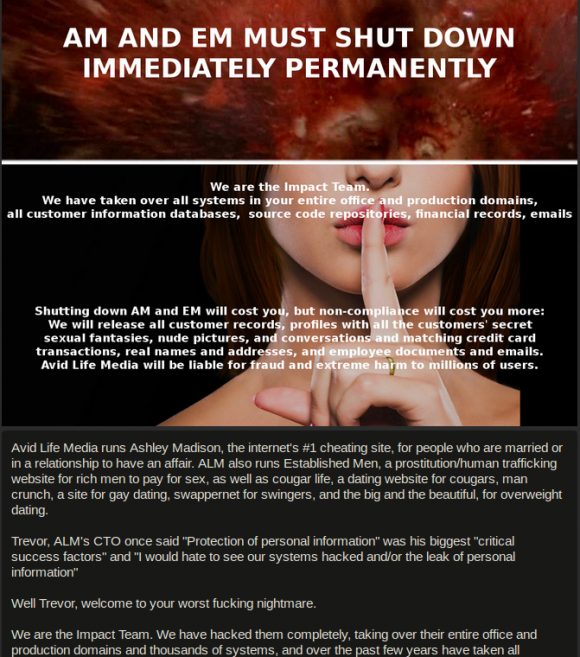
Brian Krebs breaks a story revealing that a group of hackers, known as The Impact Team, published approximately 40 MB of sensitive internal data stolen from Avid Life Media (ALM), the company that owns Ashley Madison and a number of other hookup services. The data dump includes customers' credit cards and ALM internal documents. Commenting on the breach, ALM CEO Noel Biderman says the company's security teams suspect that an individual who "touched" ALM's IT systems is responsible for the hack. At the same time, The Impact Team issues a statement threatening to release the sensitive details of all 37 million users of Ashley Madison unless ALM permanently shuts down the website.
August 18, 2015
The Impact Team releases a data dump containing the account details of all 37 million users of Ashley Madison. The files, 9.7 GB total in size, are posted to the dark web using an Onion address and are later revealed to include names, passwords, addresses, phone numbers and credit card transactions of the site's users.
August 19, 2015
The Ashley Madison data dump is posted to the open web, making its information readily searchable on several public websites. In an effort to lower the profile of the documents and information leaked online, Ashley Madison begins issuing copyright notices, including a DMCA to Motherboard journalist Joseph Cox, after the leaked material begins to surface on Twitter and other social media sites.
August 20, 2015
The hackers behind the Ashley Madison breach release a second data dump of sensitive materials stolen from the website. The leak is 19 GB in size and is said to include 13 GB of information stolen from Biderman's private email account. Researchers attempt to open that file, labeled "noel.biderman.mail.7z," but find that it cannot be unpacked because it has been corrupted.
August 21, 2015
Two Canadian law firms – Charney Lawyers and Sutts, Strosberg, LLP, both of Ontario – file a $578 million class-action lawsuit against Avid Dating Life, Inc. and Avid Life Media, Inc. on behalf of Canadian citizens who in the past subscribed to Ashley Madison's services. According to a statement issued by the firms, their lawsuit considers to what extent the website protected its users' privacy under Canadian law. At issue is a feature of Ashley Madison called "paid-delete," a process whereby users could have their data erased from the website's servers for a fee of $19USD. As of this writing, it remains to be seen whether Ashley Madison properly handled these paid-delete requests.
August 22, 2015
The Impact Team releases a third dump, which includes a fixed zip file containing messages leaked from Biderman's private email account. The emails reveal that Biderman cheated on his wife and attempted to engage in adultery with at least three separate women.
August 24, 2015
Toronto Police begin investigating two suicide reports with possible ties to the Ashley Madison hacking scandal. Meanwhile, the adultery website announces a $500,000 Canadian (US $378,000) reward for any information that could lead to the arrest of those responsible for hacking its servers.
August 25, 2015
It is announced that scammers and extortionists have begun to target Ashley Madison's users. In some cases, scammers falsely claim that they can remove a user's information from the data dumps for a price. In others, fraudsters threaten to publicly shame multiple users online for their use of the website unless they agree to send a payment in Bitcoins to the blackmailers. Reports also begin to circulate about malware being delivered through websites offering to scrub users' information from the data dump lists.
August 26, 2015
Brian Krebs publishes an article that explains how a hacker who goes by the name of Thadeus Zu on Twitter might be related to the Ashley Madison hack. Krebs explains that the adultery site was first alerted to the breach when its employees all saw a threatening message from The Impact Team posted to their computers. The AC/DC song "Thunderstruck" accompanied these messages. Krebs then looks back at Zu's Twitter history and notices that the hacker was listening to "Thunderstruck" shortly before The Impact Team first contacted Krebs back in July with regards to their successful hack of Ashley Madison. The infosec journalist goes on to explore what Zu might look like and where he might live, leading him to the conclusion that if Zu was not involved in the hack, he certainly knows who was responsible for it.
August 28, 2015
Ashley Madison releases a statement announcing the resignation of Avid Life Media CEO Noel Biderman effective immediately.
August 31, 2015
Ashley Madison publishes a statement (Update 9/2/15 09:39 EDT: Under our initial publication, this statement was listed to have been removed from Ashley Madison's site. It has since been re-posted.) stating that despite the fallout from the recent Impact Team breach, users continue to take advantage of the site's services. Among other claims, the website reports that 2.8 million women exchanged messages within the platform during the week of August 24, and nearly 90,000 new women signed up for Ashley Madison that same week alone. These statements run up against recent research, which found that of the 5.5 million female users on Ashley Madison, only 1,492 ever checked their inboxes, only 2,400 ever used the chat feature, and only 9,700 ever replied to messages that were sent to them. The research also found that 68,000 female users' profiles came from the IP address of 127.0.0.1 – a local non-routable computer – and that hundreds of female users shared the same unusual last name of a former Ashley Madison employee.
September 10, 2015
Password-cracking group CynoSure Prime announces on its blog that it has successfully cracked 11.2 million Ashley Madison users' passwords and that an additional 4 million could be broken using its techniques. The group exploited the fact that the infidelity website stored some passwords using an insecure implementation of the MD5 cryptographic hash function, which included the storing of passwords within the hashes themselves. At this time, CynoSure Prime has stated that the remaining 11 million passwords of the original 36 million leaked online are unaffected by its discovery. We will continue to update this post with further developments. If you think we've missed something, let us know in the comments below! Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

