
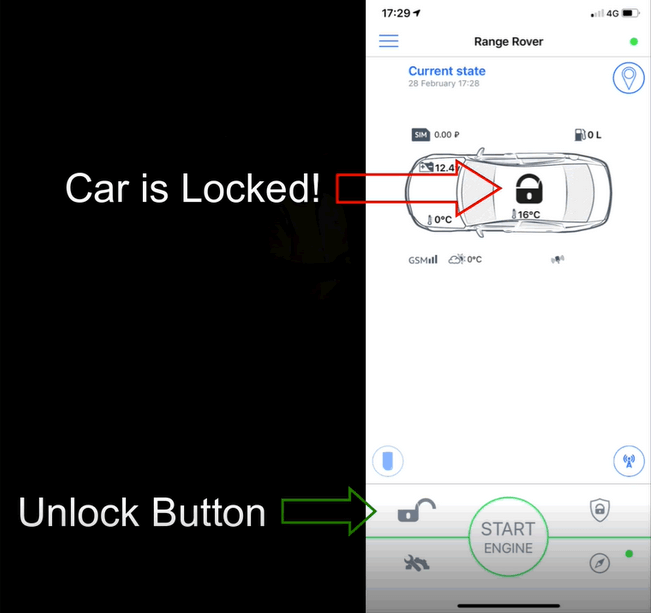
Two smart car alarm systems suffered from critical security vulnerabilities that affected upwards of three million vehicles globally. Researchers at Pen Test Partners independently assessed the security of products developed by Viper and Pandora, two of the world's largest and most well-known vendors of smart car alarms. With both systems, they found insecure direct object references (IDORs) in the API. These vulnerabilities essentially allowed the researchers to update the email address associated with each car alarm system's account, send a password reset to the altered address and thereby take over the account. Subsequently, the researchers found that they could abuse a user's account to cause all kinds of trouble. First, they leveraged their access to locate a car in real-time ad follow it using a chase vehicle. They then remotely set off the car alarm siren and flashers, which caused the driver to pull over and investigate. Once the driver exited the car, the researchers activated the immobiliser, effectively preventing them from driving off. They then cloned the key fob to be used with their mobile phone, unlocked the target vehicle's doors and drove away with it.
Source: Pen Test Partners That wasn't the end of their discoveries, however. The research team at Pen Test Partners found it could remotely access Pandora's microphone, a feature which enables drivers to make SOS calls, and thereby silently listen to individuals inside an affected vehicle. It even found a way to abuse a featured designed to halt a stolen vehicle. As it explains in a blog post:
We discovered we could kill the engine on the Viper equipped car whilst it was in motion. Promotional videos from Pandora indicate this is possible too, though it doesn’t appear to be working on our car.... [U]sing the account takeover vulnerability in the mobile app, one could kill the engine of any car fitted with these alarms.
https://youtu.be/aZUQmJMuf8c Following their discovery of these attacks, Pen Test Partners notified both Pandora and Viper about the vulnerabilities and gave the vendors a week to fix the security flaws. The former responded in 48 hours and fixed the issue overnight. The latter took a bit longer to respond but still patched the flaw in the disclosure window set by the researchers. These now-patched bugs highlight the ongoing digital security challenges associated with connected cars. Another researcher found a full account takeover vulnerability associated with connected cars in 2018, for instance. And there's no forgetting the two security researchers who remotely killed a Jeep on the highway back in 2015.

