When you hear about a data breach in the news, it's usually related to a major company or social media network that has been targeted. The erroneous conclusion would be that the hackers only focus on exploiting security flaws in large organizations, but the opposite is true. The reality is that cybercrime is deadly to small businesses, with 60% closing operations within six months of an attack. The reason is these organizations often have limited budgets for IT security, which puts them at a disadvantage compared to larger entities with a million dollar budget (or more). A significant data breach can ruin a company's reputation and even drive it to bankruptcy. Stricter government regulations (GDPR we’re talking about you.) also dictate how electronic information must be stored and secured. Considering all this, the role of IT security has become more important than ever.
Juggling Priorities
Most small- and medium-size businesses do not have the luxury of maintaining a dedicated IT security team with dozens of experts and analysts. In fact, many organizations have chosen to outsource their technology support to external vendors because it’s cheaper. But no matter the humble size of the budget, cybersecurity can’t be ignored. If a hacker is able to infiltrate your local network or front-end websites, they may be able to steal data and either sell it on the dark web or expose the vulnerability in the media. Either outcome is bad for business. When a company is found to have security gaps in their software or hardware, the immediate effect is a loss in trust among users and customers. It should surprise no one if individuals decide to take their business elsewhere for fear you can't manage their data securely.
How Vulnerabilities Become Data Breaches
One of the most common and dangerous forms of cybercrime today is ransomware. During this type of attack, the hacker tricks a single employee into clicking a link in an email or opening an attachment on their local workstation. A ransomware virus propagates to the network and sets to work encrypting the data stored on the physical hard drive. Once complete, a message pops up on screen informing the user that their system is infected and is being held for a ransom payment. More times than not, paying the ransom, usually in untraceable Bitcoin or other cryptocurrency, is no guarantee the hacker will bother to decrypt the data. He’s got his money, and the company is left poorer and without access to critical data. Furthermore, don’t expect the incident to remain unknown, and once word gets out, you’re back to the problem of trust or lack thereof from the general public.
The GDPR Factor
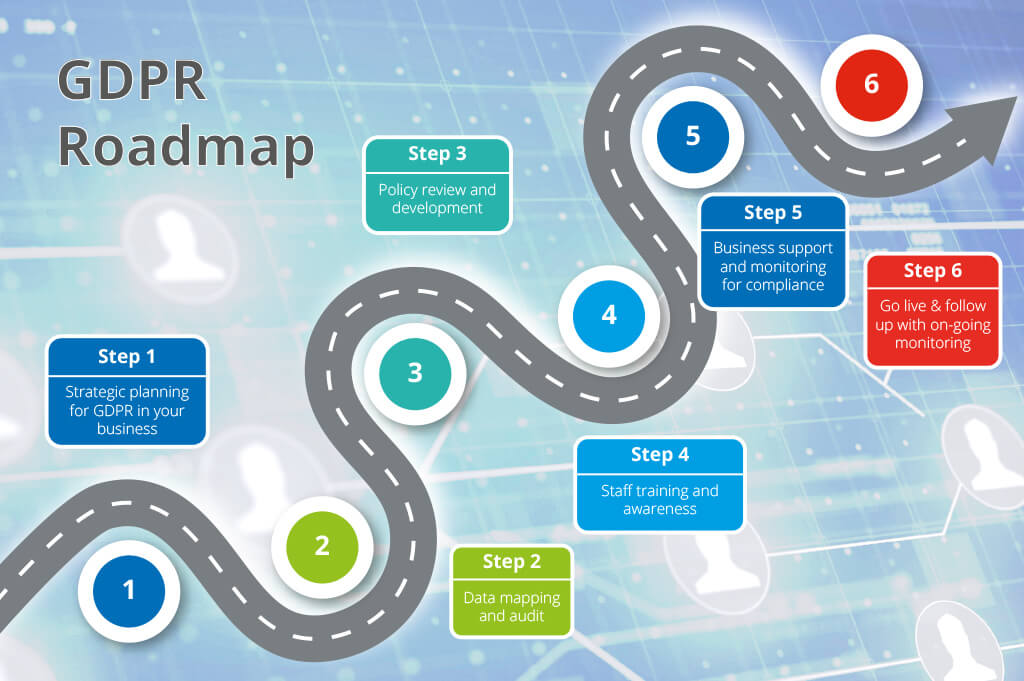
Source: cmsdistribution.com Internet privacy is a hot button topic. User data is the lifeblood of so many companies who use it to guide advertising decisions as well as assist with artificial intelligence and machine learning, while individuals are rightfully concerned with how their personal information is collected, stored, shared and distributed. As tends to happen in such situations, government swooped in to create new rules. The big splash in this arena lately belongs to Europe, which created a set of regulations called the General Data Protection Regulation (GDPR) that went live in 2018. The GDPR applies to any organization that operates a website which users can access in the EU. Yep, there are a lot of them. Website owners are responsible for protecting customer information and providing clear explanations for how that data is used. Failure to meet those regulations can result in significant fines. GDPR also requires companies to disclose the details of a breach within 72 hours of it occurring and provide a comprehensive analysis of what took place. Smaller organizations may struggle to meet this timeline due to limited security resources, and the resulting fines can make the cost of the breach even worse. While fines can run up to the greater of $25 million or 4% of annual revenue, that’s not the whole story. In order to avoid these type of business-killing penalties, the cost of becoming compliant is no small expense, running (by some estimates) up to $50,000 for a micro-enterprise of 1-9 employees and substantially more for larger operations. It should be more clear now how companies stumble into a Catch-22 situation where a data breach might cause catastrophic damage to reputation but where the GDPR fine for non-compliance is worse.
Incident Prevention and Aftermath
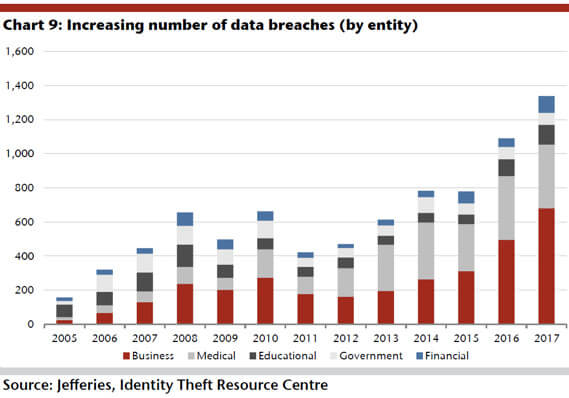
The goal of any small- or medium-size business should be to block as many outside threats as possible. But doing so on a tight budget can be a significant challenge. Tools like firewalls and intrusion detection systems are expensive to deploy and maintain. One low-cost option that organizations should adopt immediately is education. Both current employees and new hires should be exhaustively schooled in recognizing a cyber attack and reacting properly. Quick thinking in the early stages of an attack can prevent it from turning into the kind of breach that kills a business. As the incidence of cyber attack trends upward in both the private and public sectors, it’s imperative to encrypt your connection when connected to the internet. The most effective method for doing so is through the use of a virtual private network (VPN). This technology is a service deployed on the client-side that creates an FBI-grade encrypted connection to the internet.
Source: ibase.com Even if a hacker managed to observe the data flow, they would not be able to read it. Especially for a company that has employees working remotely to access a database or other internal resources, a VPN should be required.
Plan to Fail
But even companies with state-of-the-art defense systems will not be able to avoid every type of incident. In fact, plans for worst-case scenarios should be created before they happen lest the company not survive the juggernaut of confusion and panic that accompanies a data breach. The concept of disaster recovery (DR) is critical for every organization, no matter its size. Part of your DR plan should be focused on the physical technology, like ensuring that public systems remain online and that any lost data can be recovered or at least regenerated by a recent backup. You are backing up everything frequently, right? But just as important is the DR approach to public relations. Companies need to be transparent about the history and impact of any data breach they have suffered. Otherwise, the hit to their reputation will only be worse. Apologies are a start, but eventually users want to see a little less talk and a lot more action to fix vulnerabilities.
The Bottom Line
These days, your viability as an ongoing profit-seeking entity is liable to depend squarely on how much customers trust that the data on your websites and systems is protected properly. While no company wants to see a data breach, the danger is real. You may not be able to prevent every form of data breach, but planning ahead and then dealing with the problem head-on when it happens is your best bet to be able to live to tell the story.
About the Author: Sam Bocetta is a freelance journalist specializing in U.S. diplomacy and national security, with emphases on technology trends in cyberwarfare, cyberdefense, and cryptography. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

