
Security researchers released a decryption tool that enables victims of WannaRen ransomware to recover their files for free. On August 19, Bitdefender announced that it had made a WannaRen decryption utility publicly available for download. The security firm urged victims of this ransomware to save the decryptor somewhere on their computer after completing the download process. Once they click on the saved "BDWannaRenDecryptor.exe" file, they should click "Yes" and give the decryptor the permissions it needs to modify files on the infected device. They should then agree to the end user license agreement. With a "test folder" containing pairs of encrypted/not-encrypted files, victims can instruct the tool to scan their entire machine for encrypted files as part of the recovery process. Bitdefender also recommended that users select the "Backup files" option.
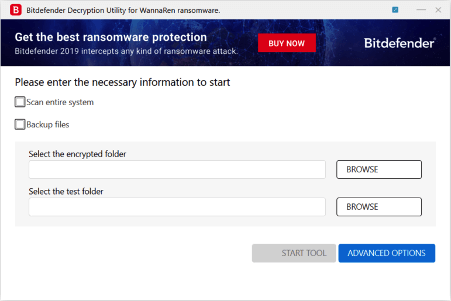
A screenshot of the WannaRen decryptor's dialog box. (Source: Bitdefender) News of this decryption utility arrived several months after WannaRen first attracted the attention of the security community. In April 2020, 360 Security Center was among the first to witness the ransomware circulating in the wild and demanding ransoms of 0.05BTC (worth approximately $600 at the time of writing). A close look by 360 Security Center at WannaRen revealed that the ransomware had originated from Hidden Shadow, a digital crime organization which has a history of exploiting EternalBlue for the purpose of moving laterally on infected networks and distributing banking trojans. The security firm found that WannaRen arrived with a PowerShelld downloader containing this same propagation method. It's not always possible for security researchers to develop a decryption tool for a ransomware family. Sometimes, the code reveals no apparent weaknesses that allow for the creation of such a utility. Acknowledging that reality, organizations and users alike should take steps to prevent a ransomware infection from occurring in the first place. This resource serves as an excellent starting point.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

