Electronic Health Record (EHR) systems have been around for over 40 years. The adoption surge came in the United States with an Executive Order for nationwide deployment in 2014. Today, they are the heart for most healthcare providers. The value of EHRs has been well-documented, offering improved patient care while improving organizational productivity and financial posture. But with great value comes great risk, as well.
The Onslaught on EHRs
EHRs are prime targets for cyber-attacks. In part, that reflects digital attackers' preference for medical providers more generally. Healthcare is the second-most common industry targeted by hackers; it's just behind financial services (Verizon 2017). Needless to say, the implications of a successful attack can be very serious. EHR has many devices connected on which the organization might not have originally considered security. With that said, the threat vectors are vast for EHR. This is bolstered by the fact that the average cost of a stolen patient record is $355, compared with just $5–$30 for financial data. In other words, Protected Health Information (PHI) is a more valuable cybercrime opportunity than the theft of banking credentials. By taking advantage of patients’ medical conditions or claim settlements, criminals can use PHI to target their victims with scams. Attackers can also create fake insurance claims, allowing for the purchase and resale of medical equipment. Or they can use PHI to illegally gain access to prescriptions for their own use or resale. If they have access to a real-time database, they can change the payment directions to redirect funds.
What About Patient Safety?
Cyber-attacks can also compromise EHR systems' uptime. A recent study by JAMIA revealed to what extent downtime impacts patient safety. The study examined patient safety incidents that resulted because of system downtime. The biggest impact from downtime was the lab. Labeling and tracking of specimens from the lab and a lack of continuity of patient identification throughout the lab processes were disclosed. Researchers found that downtime most often resulted in the need for specimens to be redrawn from patients, which produced delays. Additionally, medication incidents were due to administration issues that included the wrong dosage and medication. EHR systems provide critical patient data and treatment. Without it, human error is inevitable. The range of attacker motives and methods in healthcare is daunting. And it’s clear it has significant implications.
Next Steps with EHRs
The next wave in the EHR evolution includes interoperability and increased access. An example of this evolution effort is a $10 million gift granted to UCSF from the Silicon Valley philanthropists Priscilla Chan and Mark Zuckerberg to bring more value by integrating EHRs to improve quality of care and to better understand diseases. T his grant will also examine the notion of recycled data to improve drug development and new treatments, the concept being that there is a ton of data out there. In other words, you do not need to start from scratch all the time with new clinical trials. The Office of the National Coordinator (ONC) for Health IT is also looking at open application programming interfaces from folks like Facebook and Twitter to help address the interoperability steps. Health Level 7 (HL7) is a set of international standards for the transfer of clinical and administrative data between software applications used by various healthcare providers. Like Layer 7 in the OSI model, this focuses on the application layer, so there are lots of efforts to extend the current EHR. It sounds all good. But there are questions we still need to ask. Will these potential enhancements further increase the risk? If so, what do we need to do? Logically, it seems that more connections and integrations mean more attack vectors.
Minimize EHR Risk
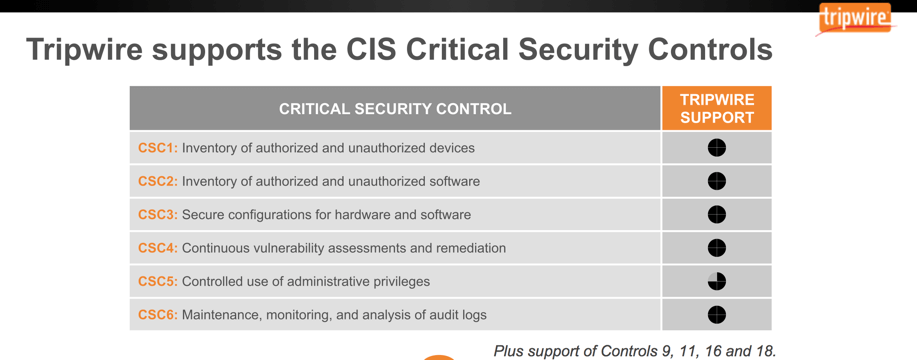
To minimize risk and establish integrity, one needs to deploy fundamental security. When it comes to basic security hygiene, the SANS Institute praises the 20 CIS Controls. It also specifically states the following:
"Implementations of the first six CIS Critical Security Controls have proven to deliver a highly effective and efficient level of defense against the majority of real-world attacks and provide the necessary foundation for dealing with more advanced attacks."
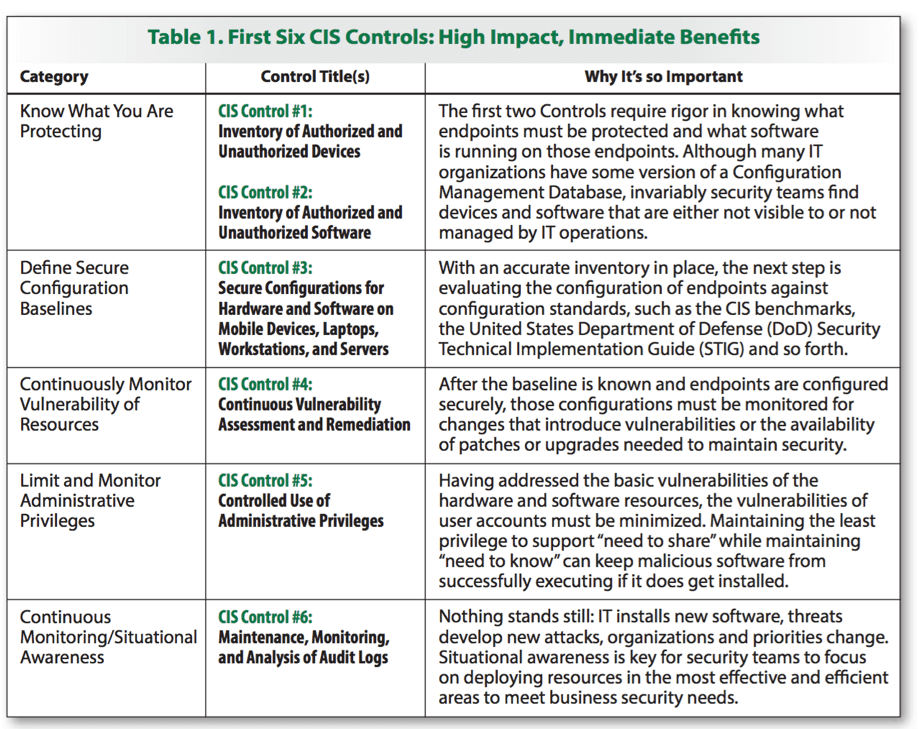
SANS 2016 The first six controls deliver the fundamentals of securing your EHR infrastructure and monitoring it regularly for changes that may indicate malicious intent. These should help prioritize your security efforts for your EHR. The good news? Tripwire has you covered for the first six controls.
I am excited about the future of EHRs and how they can improve healthcare. Healthcare is an important asset we need to invest in. For more information on how Tripwire's solutions can help hospitals, click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

