
Digital criminals have begun abusing a secure tunneling service to deliver samples of the Lokibot banking malware family. My Online Security came across an instance of this campaign when they received an email pretending to originate come from BBVA Banco Continental, a Spanish bank. The email leveraged the lure of a fake payment transfer to trick the recipient into clicking on an attachment named "Detalles de la transferencia de pago.xls." When opened, the email instructed the recipient to enable macros. Doing so caused the document to download a sample of Lokibot.
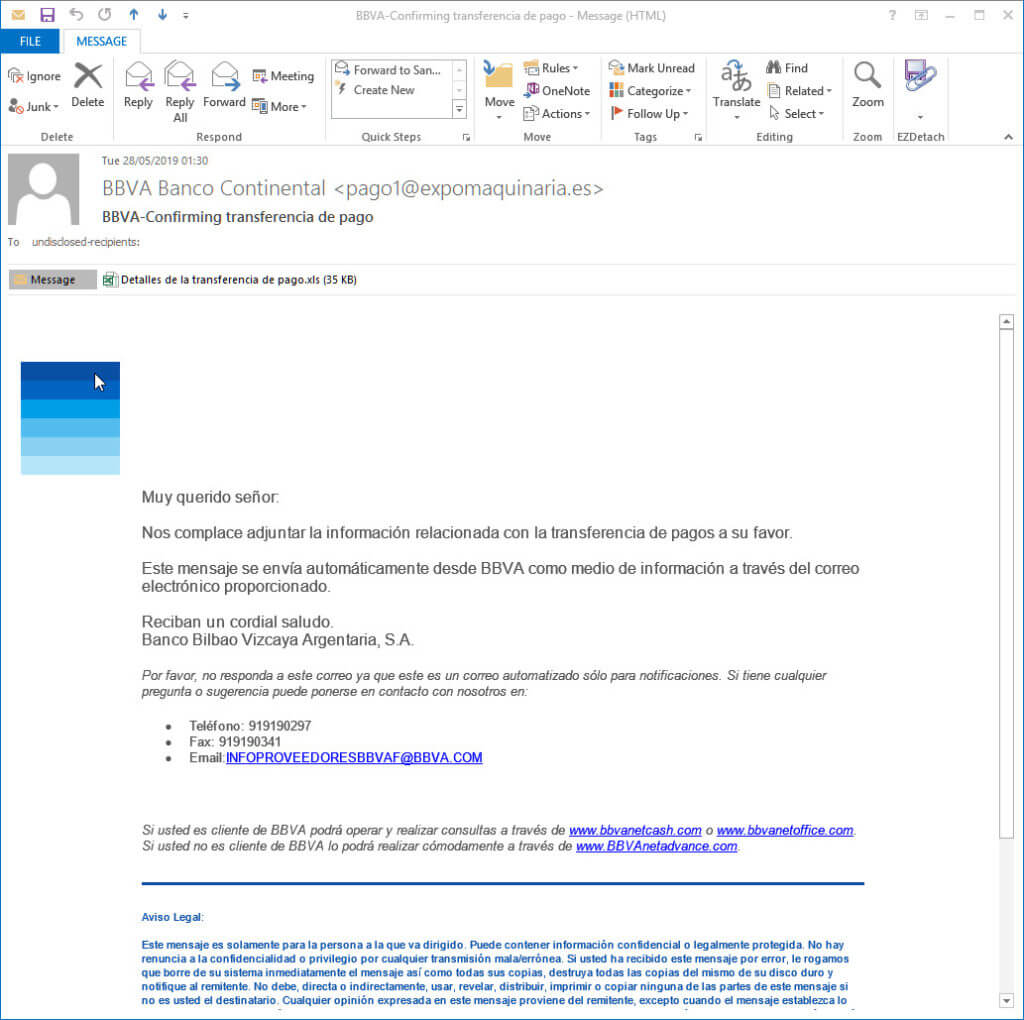
The fake BBVA email. (Source: My Online Security) This campaign stood out against other Lokibot attacks in that it abused NGROK, a secure tunneling service hosted on Amazon AWS. In the eyes of My Online Security, this particular choice worked in the favor of those behind this operation. As quoted in the security blog's research:
The Ngrok service is hosted on Amazon AWS so reporting to them is basically a waste of time because by the time they respond the malware has done its work & vanished and the malware isn’t actually stored anywhere on an Amazon server, just a link or redirect to the malware happens via Amazon AWS.
What's more, the way VirusTotal works makes it hard to gauge the efficacy of this campaign. That's because VirusTotal (at least the public version) doesn't show all subdomains. As a result, security researchers can only see malware delivered from the main ngrok.io.domain and not potentially thousands or even millions of subdomains. Given this lack of visibility, organizations should focus on protecting themselves against attack campaigns similar to the one described above. They should do so by educating their employees about some of the most common phishing attacks in circulation today. They should also leverage a sophisticated solution like Tripwire Malware Detection that can protect their critical assets against known threats and zero-day attacks.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

