
DoppelPaymer ransomware allegedly struck a U.S. coastal city in Los Angeles County by stealing its unencrypted data and then encrypting its devices. As reported by Bleeping Computer, the operators of DoppelPaymer updated their "Dopple Leaks" leak site with a post entitled "City of Torrance, CA." This post contained numerous links to files that DoppelPaymer's attackers had allegedly stolen in a successful infection. Based on their titles, those files included financial records and accounting documents, among other resources.
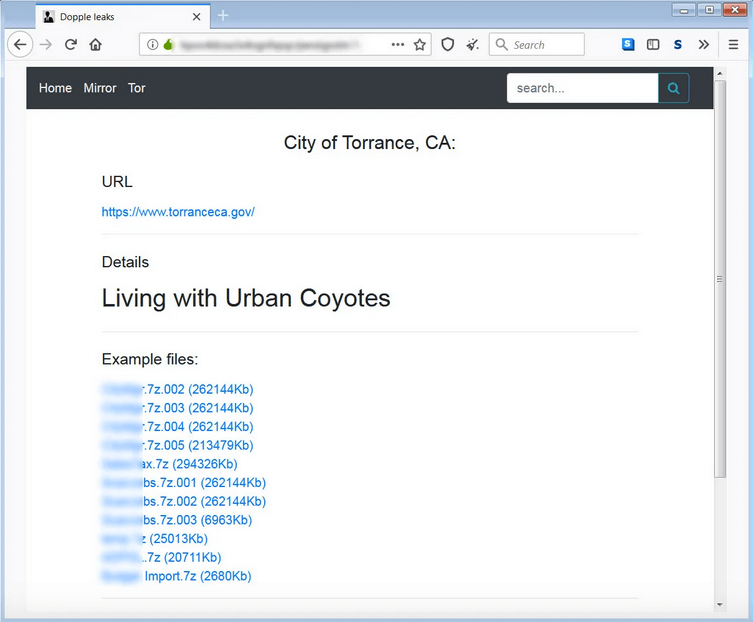
The "City of Torrance, CA" post published on Dopple Leaks. (Source: Bleeping Computer) News of a digital attack against Torrance first emerged at the beginning of March 2020. According to local media reports, the attack occurred early in the morning and affected email accounts and servers operated by the city of just over 145,000 residents. Torrance officials said that the attack had not affected "public personal data." It's unclear from the data dump whether DoppelPaymer's operators claimed to have stolen this type of information from the City of Torrance. Thy did assert to Bleeping Computer that they had succeeded in stealing a significant amount of data from the municipality, however. As quoted by the computer self-help website:
[T]he DoppelPaymer operators stated that in an attack on March 1st, they erased the City's local backups and then encrypted approximately 150 servers and 500 workstations. As part of the attack, they also claim to have stolen approximately 200+ GB of files. In a text file shared with Bleeping Computer listing all of the files they claim to have stolen, it comes out to 269,123 files throughout 8,067 directories.
DoppelPaymer's handlers also told Bleeping Computer that they had demanded 100 bitcoin (nearly $700,000) from City of Torrance in exchange for taking down the files they had already published, agreeing to delete all other stolen information from their servers and providing the municipality with a decryption key. News of this attack highlights the need for organizations to defend against ransomware attacks. One of the best ways they can do this is to prevent a ransomware infection in the first place. Here are some steps on how they can get started.

