
A subsidiary of the Dussman Group suffered a ransomware infection in which malicious actors stole and publicly leaked its data. As reported by Bleeping Computer, the operators of Nefilim ransomware made good on a promise made back in March to begin publishing victims' stolen information by updating their data leaks website with a post entitled "The Dussman Group. Part 1." The post included about 14 GB worth of files including accounting documents and images. That said, Nefilim's actors indicated that they had encrypted four domains and stolen approximately 200 GB of archives.
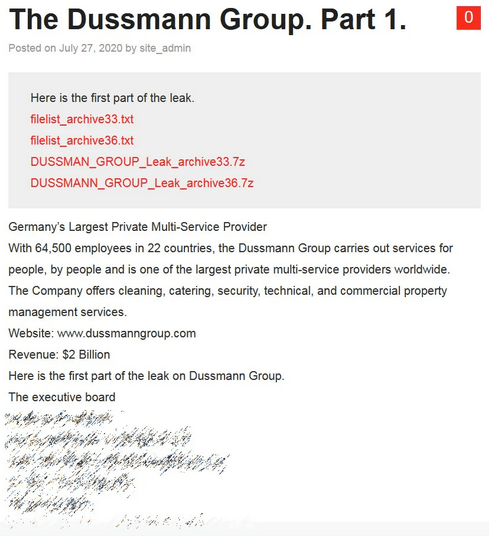
The post that appeared on the Nefilim actors' data leaks site (Source: Bleeping Computer) Upon learning of the data leak, Bleeping Computer reached out to the Dussman Group. It's then that Michaela Mehls, Dussmann Group's Head of Corporate Communications, told the computer self-help website that one of the company's subsidiaries had been the victim of a ransomware attack. As quoted by Bleeping Computer:
The refrigeration specialist, Dresdner Kühlanlagenbau GmbH (DKA) with 570 employees has been the target of a cyber attack during which data was encrypted and copied. DKA is a subsidiary of the Dussmann Group. The servers were shut down as a precaution. The data protection authorities and the State Office of Criminal Investigation in Saxony have been informed and charges have been filed. DKA is in close communication with the authorities and external cyber-security experts. Operational processes in the business unit for refrigeration air-conditioning plant engineering are secure. DKA has already informed clients and employees about the cyber-attack and the data outflow. Due to ongoing investigations, we cannot say more at present.
As of Bleeping Computer's reporting, it was unclear how the Nefilim actors had gained entry into DKA's network. This attack highlights the need for organizations to defend themselves against a ransomware infection, especially as crypto-malware actors continue to publicly leak non-compliant victims' data. They can do so by using these steps to prevent a ransomware infection from occurring in the first place.

