
Security researchers observed email attackers abusing the coronavirus outbreak to infect concerned users with the Emotet trojan. IBM X-Force found that the attack emails appeared to originate from a Japanese disability welfare service provider. Those emails informed recipients that officials had learned of a developing coronavirus outbreak in Japan's Gifu prefecture. They then urged recipients to open an attached document so that they could view recommended infection prevention measures.
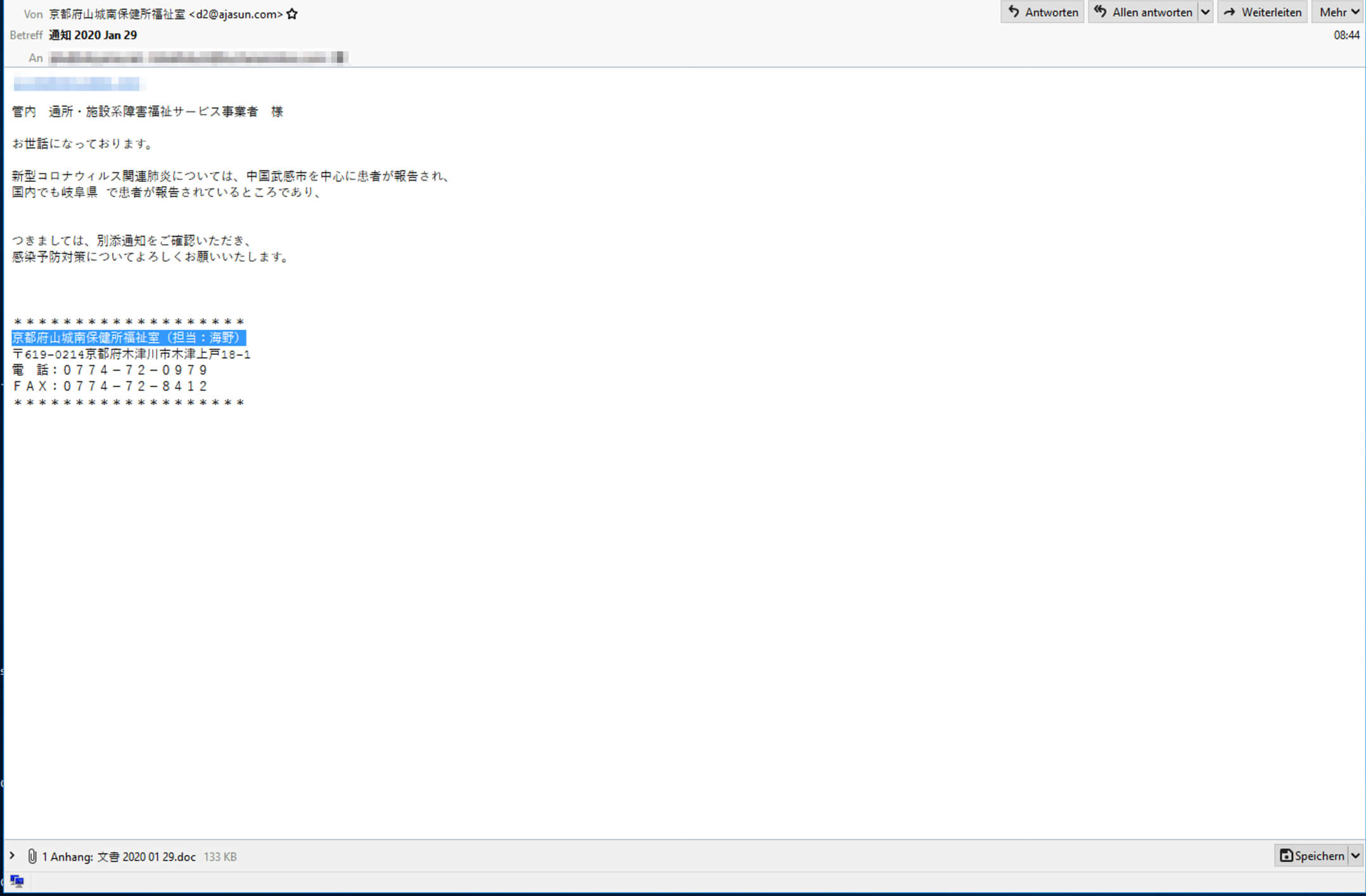
A sample text email warning Japanese users of a coronavirus outbreak. (Source: IBM X-Force)
Jurisdiction tsusho / facility related disability welfare service provider We become indebted to. Patients were reported about the new type of coronavirus-related pneumonia, mainly in Takeshi, China. Patients have been reported in Gifu Prefecture in Japan, Therefore, please check the attached notice, Thank you for your infection prevention measures.
Other attack emails warned recipients about infections in other Japan's Osaka and Tottori prefectures. Regardless of the prefecture they cited, each email also included a postal code address and telephone number to add a sense of legitimacy to their claims. Once opened, the attachment revealed a Microsoft Word document containing an Office 365 message that instructed users to enable content. Victims who complied unknowingly caused the campaign to run an obfuscated VBA macro script. This script, in turn, opened PowerShell, which installed a downloader for the Emotet trojan in the background.
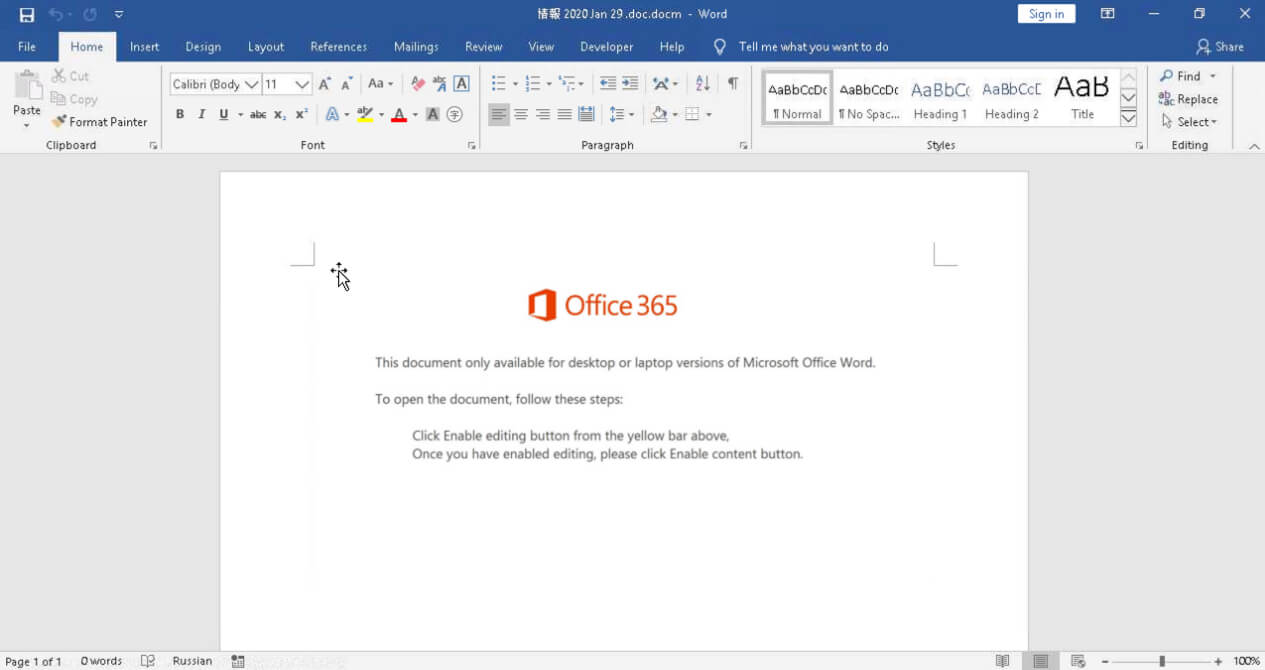
A screenshot of the malicious Word document. (Source: IBM X-Force) This isn't the only case of digital attackers abusing the coronavirus for malicious purposes. AppRiver recently spotted an email campaign that appeared to originate from the U.S. Center for Disease Control. Those emails warned users about several fictitious outbreaks of the virus around their city and instructed them to open a link in order to view prevention measures. Those links, in reality, directed users to a fake Outlook login page designed to harvest their email credentials. The email campaigns described above highlight the need for organizations to strengthen their security posture against email fraudsters. They can do so by educating their users about some of the most common types of phishing attacks distributed today.

