
The Emotet trojan recently leveraged a phishing campaign to target email addresses associated with users at the United Nations. In an email provided by Cofense to Bleeping Computer, Emotet's handlers pretended to be representatives of Norway to the United Nations (UN). They used this disguise to conduct a phishing campaign with "highly specific targeting." In total, they sent emails to approximately 600 UN email addresses. The attack emails claimed that Norway's representatives to the United Nations in New York had discovered a problem with a signed agreement. They then instructed recipients to review the issue by opening an attached Microsoft Word document.
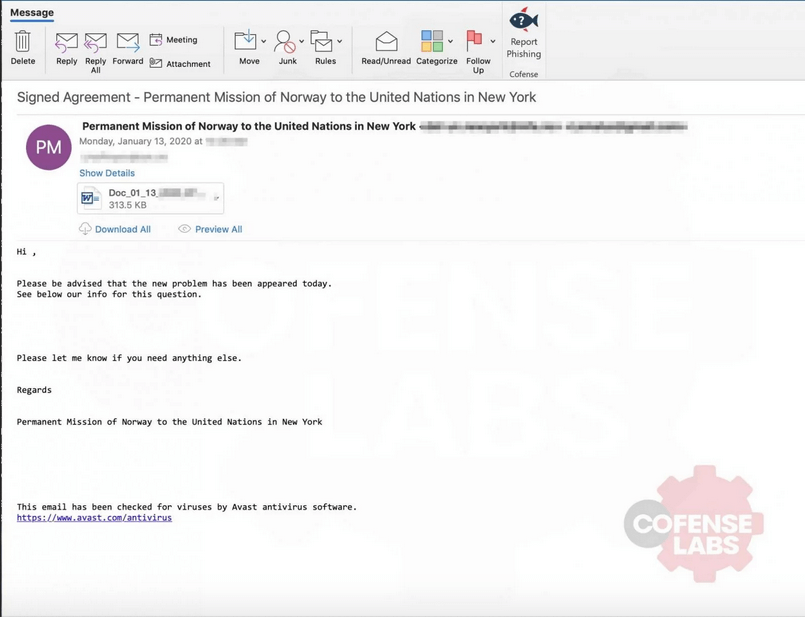
Hi, Please be advised that the new problem has been appeared today. See below our info for this question. Please let me know if you need anything else. Regards Permanent Mission of Norway to the United Nations in New York
If they didn't catch the email's awkward wording or grammar errors and opened its attachment, the recipient saw the same generic Word document template used by Emotet in all of its campaigns. This template instructed users to click on the "Enable editing" or "Enable Content" button. If they did so, the document's malicious macros then executed and loaded Emotet on the recipient's computer. Upon successful infection, Emotet is capable of loading other threats such as Trickbot. That's exactly what happened to Lake City, Florida back in the summer of 2019. In that attack, Emotet loaded Trickbot, malware which then deployed Ryuk on the municipality's network. Lake City ultimately agreed to meet the attackers' demands of $460,000. Even so, the municipality ultimately fired its IT director shortly after paying the ransom. The campaign targeting the United Nations highlights the need for organizations to defend themselves against phishing attacks. They can do so by educating their employees about some of the most common types of phishing campaigns in circulation today.

