
Researchers observed digital attackers employing expired security certificates as a disguise to distribute the Buerak downloader and Mokes malware. Kaspersky Lab learned of a new attack method in which malicious actors leveraged infected websites to warn visitors of an expired security certificate. The Russian security firm traced the first instances of these website compromises to mid-January 2020. In the process, it found that they had taken place on a variety of websites including a zoo and a vendor of auto parts. Researchers at Kaspersky observed that the infected websites displayed something along the lines of the following notification:
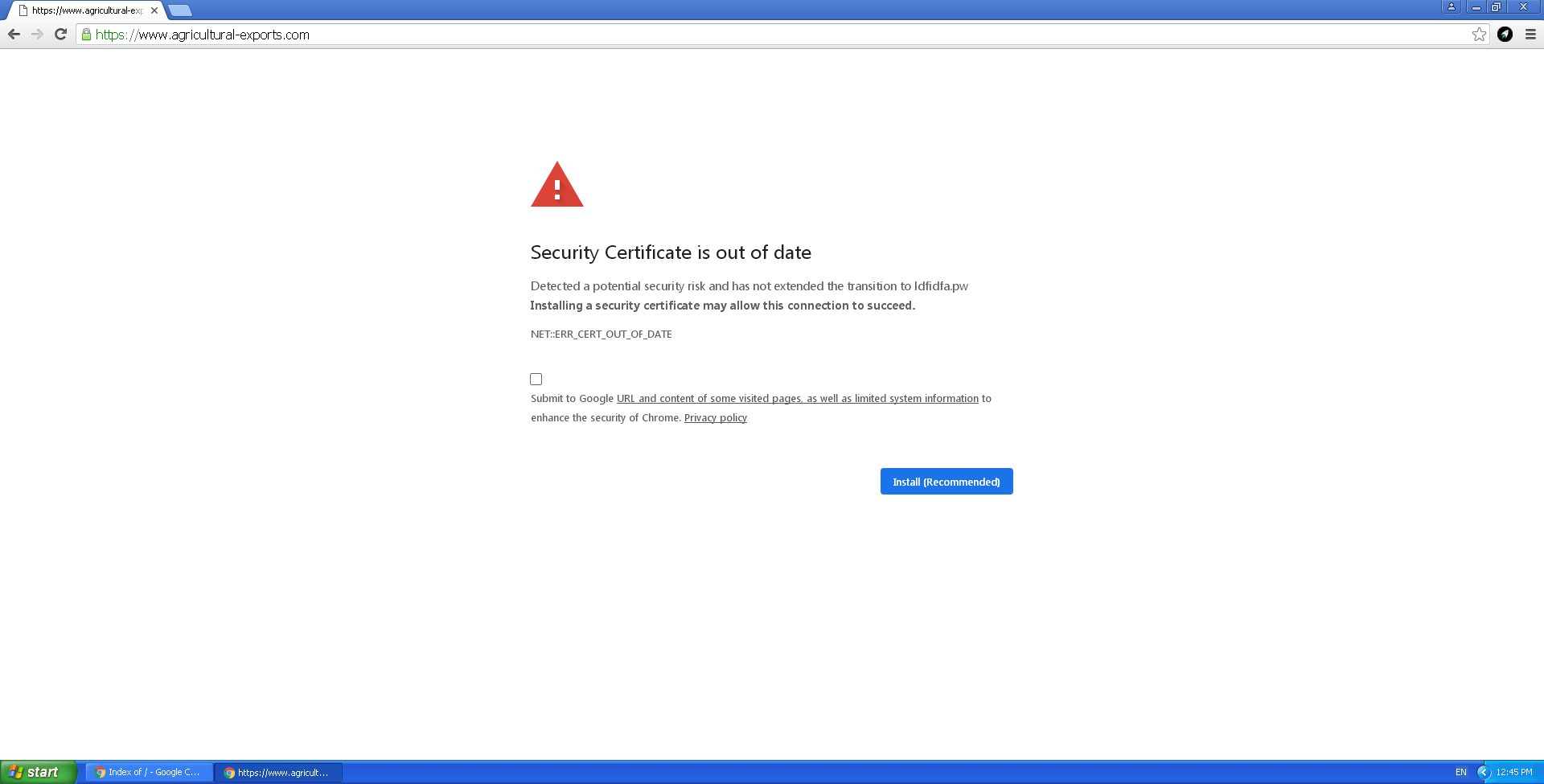
A screenshot of the expired security certificates notice. (Source: Kaspersky Lab) Not surprisingly, the notification was not legitimate. Instead, it was an iframe that digital attackers had overlaid on top of the infected website. (The URL bar still displayed the legitimate address, however.) This technique created the impression that visitors were seeing a real security warning on a legitimate website as the result of an expired certificate. Attackers leveraged this fake notification as a disguise to conduct their malicious activity. As Kaspersky Lab described in a post on Securelist:
Clicking the Install (Recommended) button on the banner initiates the download of the file Certificate_Update_v02.2020.exe, which we detect as Exploit.Win32.ShellCode.gen. Analysis of the file showed it to be Trojan-Downloader.Win32.Buerak, packed using Nullsoft Scriptable Install System. It is not the only malware distributed by the attackers. For example, Backdoor.Win32.Mokes was spread via the same campaign earlier in January.
A fake expired certificate notification constitutes the latest method employed by malware actors who wish to conceal their payloads. It certainly won't be the last. With that said, organizations should consider investing in a solution that examines suspicious file behavior in a quarantined environment and delivers detailed reports on relevant system changes. Click here to learn how Tripwire File Analyzer can help.

