
Digital fraudsters have launched a new phishing campaign that uses a salary increase scam to trick employees into handing over their credentials. Spotted by the Cofense Phishing Defense Center, the campaign used spoofing techniques to trick recipients into thinking that the attack emails came from their HR department. Those emails claimed that the recipient's wages would increase as part of a larger organization-wide effort to raise salaries in November 2019 and begin paying out these increases the following month. In support of this ruse, the emails came with an embedded link to what it claimed was a spreadsheet detailing employees' raises.
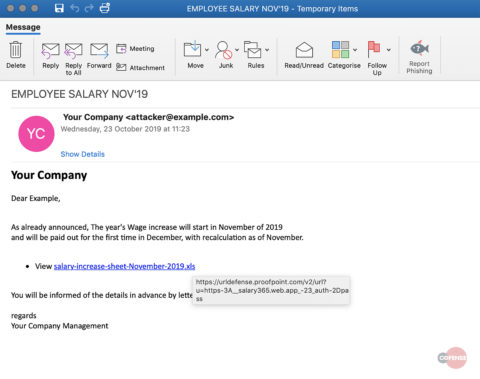
The body of an attack email detected by Cofense. Cofense explains how this link didn't send the user where they think they're going:
The idea is to make recipients believe they are being linked to a document hosted on SharePoint. However, they are being linked to an external website hosted on hxxps://salary365[.]web[.]app/#/auth-pass-form/. One can assume from the context of this malicious URL that it was specifically chosen and hosted for this phishing attempt.
Ultimately, the salary increase scam campaign transported the user to a phishing landing page hosting a fake Office 365 login portal. The URL for this page appended the user's email address and leveraged this information to auto-populate the form's "email" text field. The campaign then prompted the user to enter their password. The attack email analyzed by Cofense underscores how digital attackers often go to great lengths to capitalize on users' curiosity and trick them into doing something they normally wouldn't do. In response, organizations need to protect their employees against phishing emails that deliver a salary increase scam. They can do this by investing in a security awareness training program that educates everyone about some of the most common types of phishing attacks in circulation today. They can use this resource to boost the efficacy and focus of their internal training.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

