
A researcher has created a free decryption tool which victims of the PyLocky ransomware family can use to recover their affected files. Mike Bautista, a security researcher at the Cisco Talos Intelligence Group, is responsible for developing the tool. Cisco Talos has made this utility freely available for download on GitHub. First reported on by Trend Micro in September 2018, PyLocky is a family of crypto-malware known for imitating the infamous Locky ransomware. It's not related to Locky in any way, however. It just refers to itself as the "Locky Locker" in its ransom note and informs victims that they can obtain the "Locky Decryptor" by meeting their ransom demands.
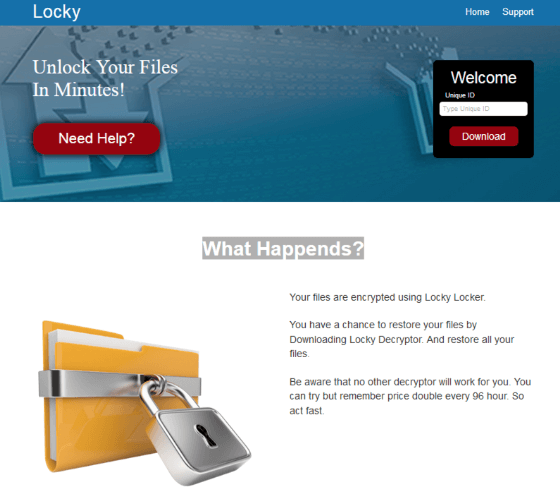
PyLocky’s ransom note pretending to be the Locky ransomware. (Source: Trend Micro) PyLocky stands out among other ransomware families by being written in Python, featuring anti-machine learning capabilities that make static analysis more difficult and relying on spam campaigns to target users primarily based in France and other European countries. It's important to note that Cisco Talos' decryptor comes with a few restrictions. The tool works on infected Windows machines only, for instance. Also, it tends to have the most success decrypting small files; it doesn't currently work as well with assets that are over 4 GB in size. Cisco Talos identifies another condition for its utility in a blog post:
Because our tool requires the capturing of the initial PyLocky command and control (C2) traffic of an infected machine, it will only work to recover the files on an infected machine where network traffic has been monitored. If the initial C2 traffic has not been captured, our decryption tool will not be able to recover files on an infected machine. This is because the initial callout is used by the malware to send the C2 servers information that it uses in the encryption process.
Given the continuing prevalence of PyLocky and other ransomware families in the digital threat landscape, users and organizations alike should focus on preventing an infection in the first place. They can do this by patching their software on a regular basis and training their employees to watch out for suspicious links and email attachments. Click here for additional ransomware prevention tips.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

