
A new threat group called "Fullz House" is using both phishing and web skimming in order to maximize the profits of its attacks. Fullz House isn't new to the threat landscape, but RiskIQ observed that the group had expanded its activities to include web skimming beginning in August-September 2019. These two operations are mostly split. However, there is a slight overlap in their domain-to-address resolution data on their attack infrastructure. The sales platforms used by Fullz House also intersect with those used by the group to steal customers payment card credentials.
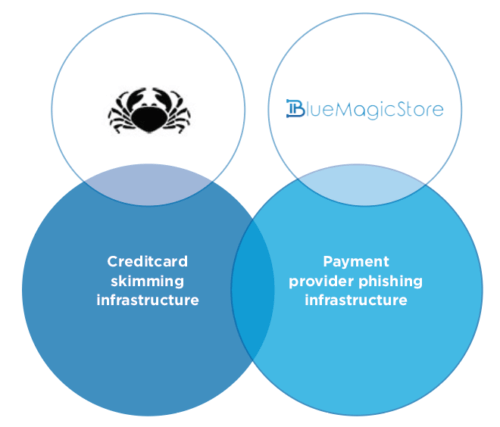
A look at Fullz House's infrastructure (Source: RiskIQ) RiskIQ found that the group is using active phishing campaigns to target PayPal users and other individuals online. These operations leverage reconstructed phishing pages that all belong to the same framework. Through its phishing attacks, Fullz House then sells "fullz," or complete packages of an individual's personally identifiable information, on its store "BlueMagicStore." At the same time, Fullz House is performing web skimming attacks using some very interesting tactics. RiskIQ says these attacks stand out first and foremost because of the skimmer that the group is using. As it explains in its threat research:
What makes these operators especially fascinating is that they wrote their own skimmer, which is something we don’t often see anymore. The majority of criminals rely on skimming kits, buying pre-made skimmers from others—there are only a handful of operators now that maintain their own code.
A closer look by the security firm revealed that the skimmer differentiated itself from those used by Magecart and others in another key respect: it does not wait for users to complete their purchases. Instead, Fullz House's skimmer hooks into every input field and essentially behaves as a keylogger by checking to see if there's any data that it can steal from those fields. Not only that, but the group is capitalizing on its experience with phishing to perform man-in-the-middle (MitM) attacks that redirect users from a compromised store to a fake payment page designed to steal their data. This stolen data ends up going to the same location where the skimmer sends its information. From there, the groups sells users' stolen payment card details on its "CardHouse" carding store.
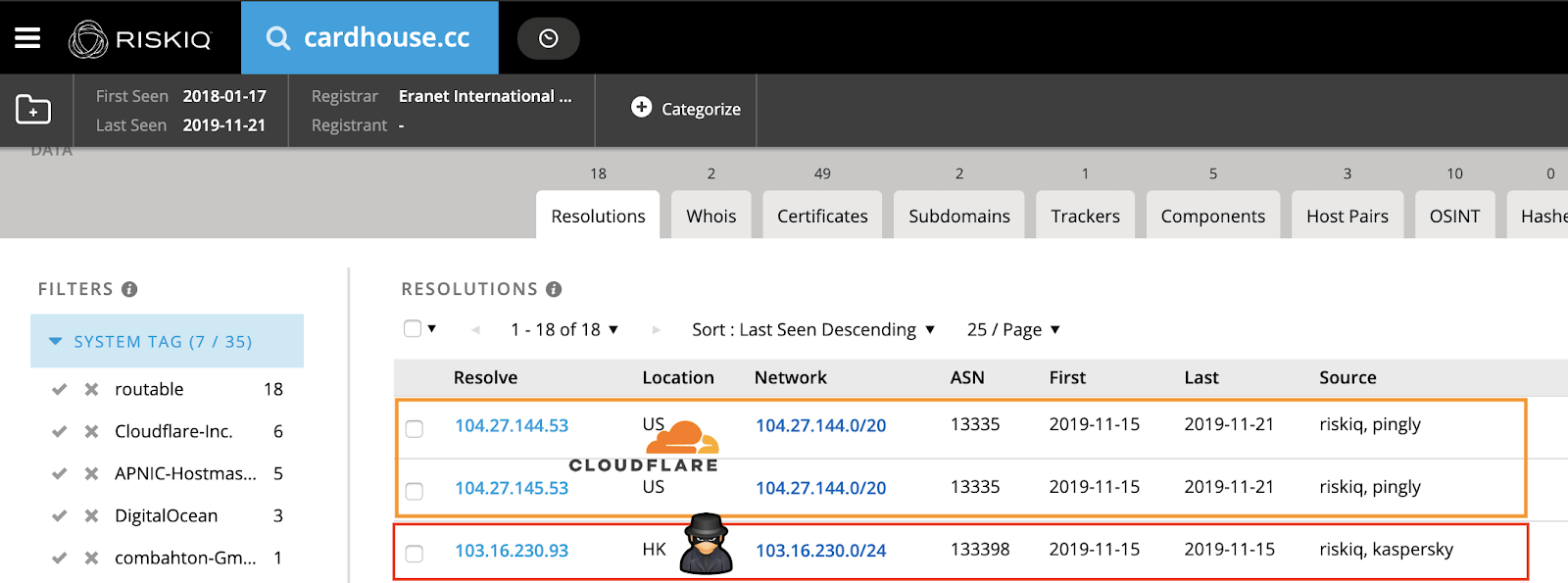
CardHouse The emergence of groups like Fullz House emphasizes the need for organizations to protect themselves against a range of digital threats. In this case, they should use security awareness training to educate their employees about the most common types of phishing attacks in circulation today. They should also use solutions like Tripwire File Analyzer to monitor for suspicious activity in their systems.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

