
A new ransomware family called "[F]Unicorn" masqueraded as a COVID-19 contact tracing app in order to target Italian users. On May 25, the the Computer Emergency Response Team (CERT) from the Agency for Digital Italy (AgID) revealed in an advisory that it had received a sample of [F]Unicorn from security researcher JamesWT_MHT. The sample analyzed by CERT-AgID relied on emails informing users of a PC beta release of Immuni, Italy's COVID-19 contact tracing app, for distribution. Those attack emails leveraged typoquatting techniques to trick users into clicking on a download link for the advertised app. Once clicked, the malware showed a fake dashboard that claimed to offer COVID-19 information collected by the Center for Systems Science and Engineering at Johns Hopkins University. In the background, the email got to work encrypting a user's data. It then displayed its ransom note in Italian.
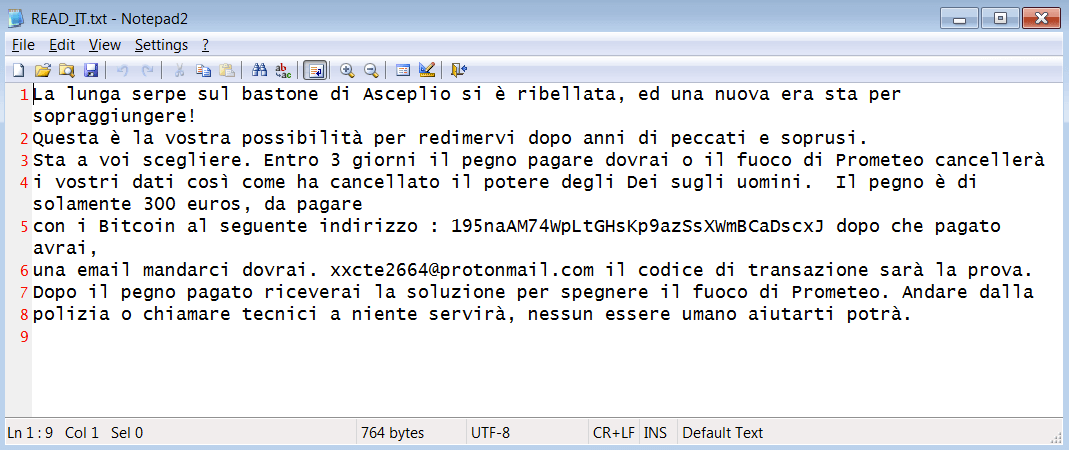
[F]Unicorn's ransom note (Source: Bleeping Computer) As translated into English by Bleeping Computer:
The long snake on Asceplio's staff has rebelled, and a new era is about to come! This is your chance to redeem yourself after years of sins and abuses. It's up to you to choose. Within 3 days the pledge to pay you will have to or the fire of Prometheus will cancel your data just as it has wiped out the power of Gods over men. The pledge is only 300 euros, to be paid with Bitcoins at the following address: 195naAM74WpLtGHsKp9azSsXWmBCaDscxJ after you have paid, an email to send us you will. [email protected] the transaction code will be the proof. After the paid pledge you will receive the solution to put out Prometheus' fire. Go from police or calling technicians will be of no use, no human being can help you.
There's good news and bad news. First, the bad news. The email address included in the ransom note above was invalid. This error left users without a viable means of sending proof of payment to the attackers for the purpose of recovering their data. Now onto the good news. CERT-AgID found that those behind [F]Unicorn received the password responsible for encrypting a user's data in cleartext. Victims could thus leverage network traffic logs to intercept this password and decrypt their information for free. While it's possible for victims of [F]Unicorn to recover their data for free, the same cannot be said about other ransomware threats. That's why organizations need to make an effort to protect themselves against ransomware attacks. One of the ways they can do this is by working to prevent a ransomware infection in the first place.

