
Most security breaches are the result of one thing: sloppy password practices. Too many people make the mistake of choosing weak passwords, or reusing passwords that they have used elsewhere on the internet - making life too easy for malicious hackers trying to gain unauthorised access.
So I was pleased to see Google announce that over the coming weeks it will be rolling out a new feature to users of its Chrome browser which will make it easier to check for weak passwords and warn if stored passwords have been compromised in a past data breach.
Chrome users who store their passwords in the browser's built-in password manager will be able to check if their passwords are weak or have been compromised by going to Settings > Passwords > Check passwords > Check Now, or automatically after logging into websites.
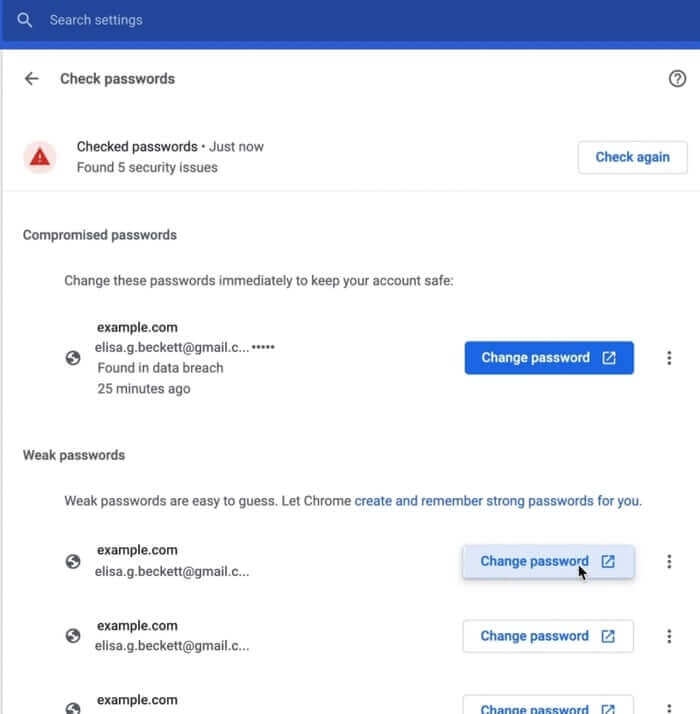
And, of course, once a weak or compromised password has been spotted it can be replaced to a stronger, safer password on the spot.
These password security audits come as part of the browser's "Safety Check" feature introduced last year.
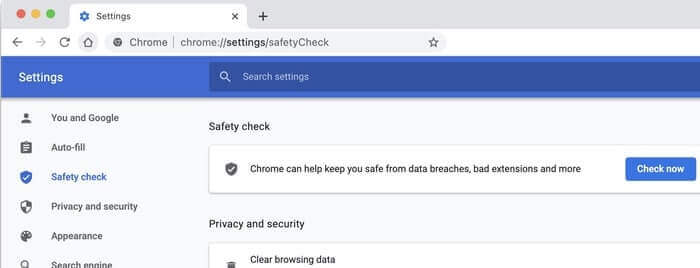
Google says that Chrome's Safety Check feature is used 14 million time every week, and since its introduction there has been a 38% reduction in the number of compromised login passwords stored in the browser.
With the latest enhancements, according to Google, users will be able to "update multiple usernames easily, in one convenient place." Initially the improved feature set will be available on the desktop and iOS versions of Chrome, but will be coming to the Android version "soon."
Personally, I'm more of a fan of using a third-party password manager than the one built into my web browser - but any kind of password manager is better than none at all, and anything that helps computer users raise their game when it comes to the passwords they use online has to be good news.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

