If you're running a CCTV surveillance camera in your office, high street store, or at home make sure that you are not unwittingly helping hackers launch denial-of-service attacks. That's the warning that has been issued by the security team at Incapsula, who discovered a botnet of 900 CCTV cameras spread across the globe, flooding targeted websites with unwanted traffic in an attempt to blast them off the internet. According to the researchers, the CCTV cameras were vulnerable because they were set up with weak login credentials, and accepting connections from anyone else connected to the internet. All the hackers had to do was launch a brute-force dictionary attack against the CCTV devices to gain access, working through a list of likely passwords. In this particular DDoS campaign, all of the compromised CCTV cameras were running BusyBox. The BusyBox software provides a collection of Unix tools in a single executable file, and was specifically developed for embedded operating systems with limited resources such as routers. That's obviously very handy for Internet of Things (IoT) devices that may have limited resources and memory, but it has become clear over the last year or so that manufacturers creating such devices may not have properly considered how to best secure devices from being attacked by hackers. The Bashlite malware scans networks for devices running BusyBox, gains access by working through a list of easy-to-guess usernames and passwords, and then runs commands to hijack control of the system. In the past, versions of the malware have been seen exploiting the notorious Shellshock vulnerability. Once compromised, malware-infected devices can be easily commanded en masse to launch denial-of-service attacks.
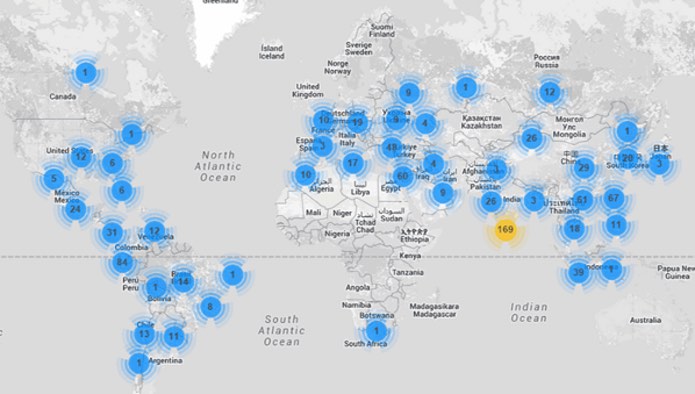
Examining the IP addresses of devices attacking one of its clients, Incapsula was bemused to find that not only did they all appear to belong to CCTV cameras using default login credentials, but also that one of them was located in a nearby shopping mall.
Looking through the camera lens we also spotted a familiar sight—a storefront in a mall located not five minutes away from our offices! The opportunity for some community service was too good to pass up, so we hopped in our cars and took a trip to the mall. We were able to meet with the store owners, show them how their CCTV cameras were abused to attack our clients and help them clean the malware from the infected camera's hard drive. As we did, we witnessed it coughing out attacking requests up to the very last moment.
The fundamental problem here is that the CCTV cameras aren't just cameras. They're computers, running software, and connected to the internet. And - critically - many of them are poorly secured, with default passwords. The researchers were able to demonstrate just how poorly the devices were protected by noting that in almost every case they were showing evidence of having been hacked by "several different individuals". As the research demonstrates, this illegal hacking goes beyond voyeurism and inquisitiveness to see what a CCTV camera is looking at, but actually exploiting the small computer system connected to the camera in order to commit criminal attacks. The key takeaway from the research is that whatever you have connected to the internet - whether it be a CCTV camera, a router, a WiFi access point or a network access server, you should never leave them configured with the default password they shipped with. In an ideal world, manufacturers would force you to change a device's password to something more secure before you could do anything more with them, but my suspicion is that there will be many more IoT devices hacked before that becomes commonplace. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

