
According to Gartner, threat intelligence is evidence-based knowledge, including context, mechanisms, indicators, implications and actionable intelligence. When security research teams or government agencies release threat intelligence reports, some of the more tactical actionable intelligence is in the indicators. These indicators include (but are not limited to) IP addresses, domain names, file names or file hashes. The end goal of providing this level of detail is so defenders can either provide mitigating steps in place to block malicious behavior or to use this information to search for evil within their organization. I like to think of indicators as threat information rather than threat intelligence. Without additional context, such as time or intended targets, the indicators can be worthless. Time is an important one because indicators can be modified very quickly by an adversary. The pyramid of pain illustrates this quite well.
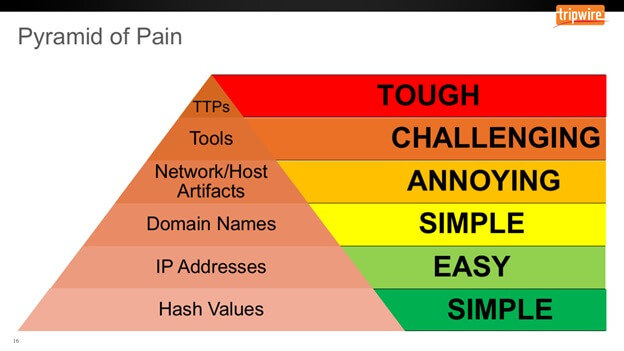
At the bottom of the pyramid you have file hashes, which are defined as trivial. This is because adversaries can change the hash of their malware programmatically with each iteration if needed. On the defender’s side, it’s also trivial to detect malicious hashes. Tripwire Enterprise has been detecting file hashes for the better part of two decades, and we’ve gotten quite good at it. When monitoring for change, knowing the file hash will quickly identify a changed file (although a files permissions and attributes can be changed without modifying the file hash). Starting in Tripwire Enterprise 8.4, a REST-based API was included with each server-side installation to allow for easier integrations with various technologies. One part of this API can query for various files, or elements, based on any number of attributes. While you can search for specific hash, the API Also allows you to supply any file hash and detect the type of hash supplied. For example, to search for a SHA1 hash, you can use the URL of https://te-server/api/v1/versions?sha1=3b1333f826e5fe36395042fe0f1b895f4a373f1b. Alternatively, you can also get the same results by using the URL of https://te-server/api/v1/versions?hash=3b1333f826e5fe36395042fe0f1b895f4a373f1b.
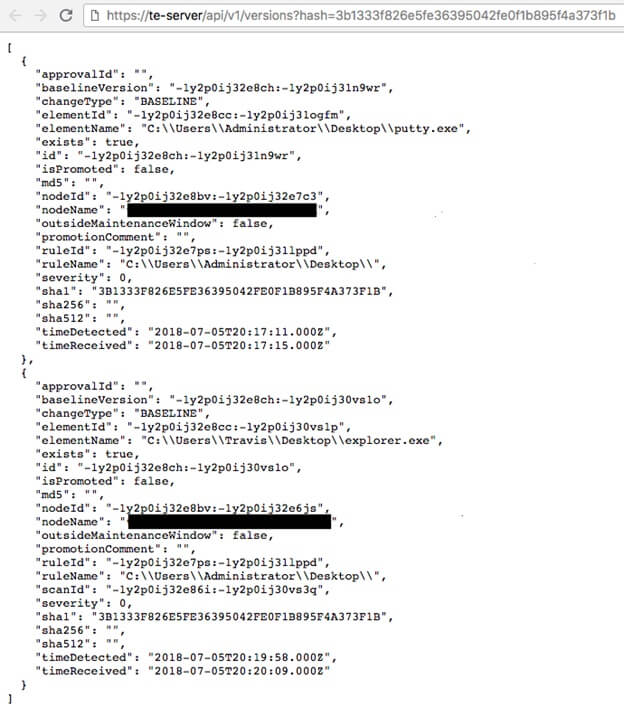
What’s great about searching for a specific API is that it does not care about file names. So, if a piece of malware is spreading across the environment and using unique names on each infection without mutating its hash, this will expose that very quickly. In the example above, we can see that the hash we looked for is named putty.exe on the first node but explorer.exe on the second node. When you read a blog post or receive intel with a file hash indicator, this is a quick way to search your environment for that data. Since the API is REST-based, creating quick scripts to pass the file hashes to are quick and simple. If no results are found, make sure you’re collecting the appropriate data from the endpoints. Create a rule to gather all EXE files or create a custom rule to search for areas of the endpoint, which are outlined by the threat intelligence report. Again, threat intelligence is all about context and actionable intelligence, so make sure you have the tools at your disposable to take advantage of that data.
5 Things Your FIM Solution Should Be Doing for You
Discover the pivotal role of File Integrity Monitoring in maintaining system security and compliance with major standards. Tripwire Enterprise stands out as an advanced solution, offering real-time detection and detailed context for system changes, making it a superior choice for robust cybersecurity.

