
2016 will forever be remembered for all the "mega-breaches" that exposed users' personal information. Most of those larger-than-life security incidents dated back several years, with some breaches having made a larger splash in the security community than others. LinkedIn and Tumblr certainly stood out. But all other events paled in comparison to Yahoo. Why? By abusing exposed email addresses and unencrypted security questions/answers, bad actors could have circumvented Yahoo members' hashed passwords (Bcrypt protected the vast majority of them.) to gain access to their webmail accounts. And we all know the treasure trove that those types of accounts generally prove to be for attackers. Three University College London information security researchers Jeremiah Onaolapo, Enrico Mariconti, and Gianluca Stringhini explain:
"In the case of compromised webmail accounts, it is not uncommon to find password reset links, financial information, and authentication credentials of other online accounts inside such webmail accounts. This makes webmail accounts particularly attractive to cybercriminals, since they often contain a lot of sensitive information that could potentially be used to compromise other accounts."
Compromised webmail accounts certainly present attackers with a number of possibilities. But do those bad actors seize any of those opportunities? How do computer criminals leverage webmail accounts once they've been compromised? Do they prefer to abuse them for certain purposes over others? Those same questions intrigued Onaolapo, Mariconti, and Stringhini, so much so that they came up with an experiment of their own design in an attempt to answer them.
It Takes Some Honey to Observe a Computer Criminal
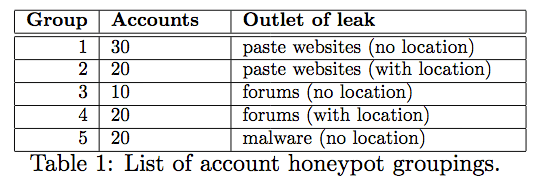
In an effort to understand what happens to compromised webmail accounts in the wild, the three researchers crafted an experimental infrastructure made up of two parts. The first part consisted of 100 dummy Gmail accounts. To make the accounts appear legitimate, the team populated them with emails they obtained from the Enron email dataset. They then modified all employee names and business information to make it seem like the accounts belonged to a fictitious company. Once they finished setting up those "honey accounts," as they called them, the researchers embedded scripts based on the Google Apps Script into them, tools which allowed the researchers to receive notifications of account activity such as when someone created a draft or opened a message. Onaolapo, Mariconti, and Stringhini also wanted to understand how attackers use webmail accounts stolen via malware. For that purpose, they designed the second part of the experiment: a malware sandbox infrastructure through which they supplied honey credentials to virtual machines (VMs). Those VMs triggered the malware, a process which automatically exfiltrated the webmail account credentials to command and control (C&C) servers under attackers' control. There's a lot that could have gone wrong with this experiment. The researchers foresaw some of those scenarios and subsequently accounted for them in their infrastructure's design:
"To prevent the honey accounts from sending spam messages while under the control of cybercriminals, we configured them to send all outgoing email messages to a mail server under our control. We also configured the mail server to simply dump the emails to disk, without forwarding them to the intended destination (as a normal email relay server would do). In addition, we imposed bandwidth and traffic restrictions on the malware sandbox infrastructure (described earlier) following best practices, to ensure that the infected VMs could not be used for harmful purposes, for instance, denial-of-service attacks. Finally, we obtained ethics approval for the experiments from our institution (UCL)."
With those safeguards in place, Onaolapo, Mariconti, and Stringhini leaked the webmail account credentials to paste sites and forums as well as leveraged the VMs to simulate an information-stealing malware infection.
Attackers flocked to the honey accounts like flies, and for seven months, the researchers observed what happened next. Here is what they found:
- Computer criminals that interacted with the honey accounts generally exhibited at least one of four behavioral types: Curious (accessed the accounts to see if they were real), Gold Digger (searched the accounts for sensitive information), Spammer (leveraged the accounts to send spam), and Hijacker (changed the accounts' login credentials).
- Criminals who obtained the accounts via malware outlets or paste sites went to more lengths to conceal information about themselves than those who found the accounts on forums. Some concealed data about their browsers, for example.
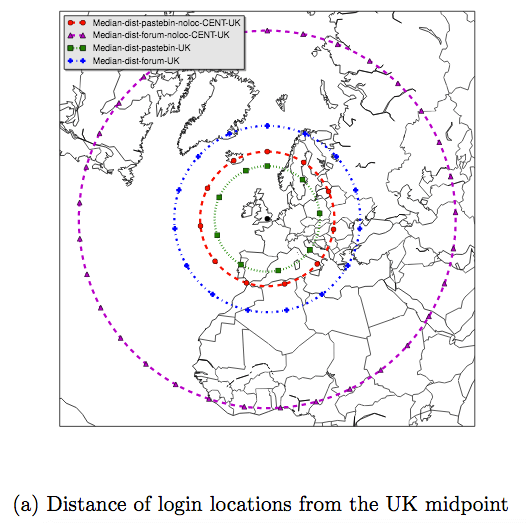
- Whenever they provided location information about the accounts, such as a claim that they originated from users located near London, the researchers noticed attackers accessing the accounts from locations that were close in proximity. Attackers pulled off that feat using proxies to evade raising a red flag with anomaly detection systems employed by webmail service providers.
Conclusion
Users have much to lose when someone compromises their webmail accounts. As the researchers point out:
"If they [the attackers] are able to obtain additional information about the victims, they can mount more effective attacks against such victims. For example, it is possible to obtain additional information about victims through online social networks. With the help of such information, they can then connect to the compromised accounts via proxies in a bid to appear close to the locations from which the victims usually connect to their accounts (to fool login anomaly detection systems)."
That's why users should protect their webmail accounts with a strong, unique password. They also implement two-step verification (2SV) whenever it's available, as doing so will protect their accounts even if a bad actor somehow obtains their login credentials. For more information about Onaolapo, Mariconti, and Stringhini's experiment, please read their full paper here (PDF).
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

