
Together with the National Cybersecurity Center of Excellence (NCCoE), the National Institute of Standards and Technology (NIST) has released a series of practice guides that focuses on data integrity. Data integrity is the property that records have not been altered in an unauthorized manner. Tripwire is very proud to have contributed and collaborated with other technology vendors in the development of these practice guides.
Challenges to Data Integrity
Destructive malware, ransomware, malicious insider activity, and even honest mistakes all set the stage for why organizations need to quickly detect and respond to an event that impacts data integrity. Businesses must be confident that these events are detected quickly and responded to appropriately. Attacks against an organization’s data can impact business operations, revenue, and reputation. Examples of data integrity attacks include unauthorized insertion, deletion, or modification of data to corporate information such as emails, employee records, financial records, and customer data.
Some organizations have experienced systemic attacks that force operations to cease. While ransomware remains the most prominent attack method, other data integrity attacks may be more dynamic, targeting machines, spreading laterally across networks, and continuing to cause damage throughout an organization. These behaviors are usually targeted against multiple files at a time. After all, for most organizations there would be little impact if a single file is held hostage. Most attackers tend to choose high impact over subtle craftiness. This makes the events easily detectable if the correct monitoring tools are in place.
NIST Cybersecurity Framework
NIST published version 1.1 of the Cybersecurity Framework in April 2018 to provide guidance for protecting and developing resiliency for critical infrastructure and other sectors. The framework core contains five functions, outlined in a handy, easy-to-remember graphic:

- Identify – Develop an organizational understanding to manage cybersecurity risk to systems, people, assets, data, and capabilities.
- Protect – Develop and implement appropriate safeguards to ensure the delivery of critical services.
- Detect – Develop and implement appropriate activities to identify the occurrence of a cybersecurity event.
- Respond – Develop and implement appropriate activities to take action regarding a detected cybersecurity incident.
- Recover – Develop and implement appropriate activities to maintain plans for resilience and to restore any capabilities or services that were impaired due to a cybersecurity incident
NIST SP 1800-25, Identifying and Protecting Assets Against Ransomware and Other Destructive Events
Applying the Cybersecurity Framework to data integrity, this practice guide informs organizations of how to identify and protect against a data integrity attacks, and in turn, understand how to manage data integrity risks and implement the appropriate safeguards. The solution developed by NCCoE isolates the opportunities that would allow for cybersecurity events to occur and implements strategies to remediate those conditions. Also, the solution uses information from known cybersecurity events, and applies them to protecting IT infrastructure. To achieve this, the following core capabilities should be in place:

- Inventory
- Vulnerability management
- Policy enforcement
- Integrity monitoring
- Logging
- Backups
- Secure storage
- Network protection
Of course, it all starts with an accurate inventory of all the devices in an environment. Following that, a vulnerability management capability facilitates scanning and revealing weaknesses across the enterprise. A good vulnerability management system delineates priority for these exposures based on severity and exploitability, and it should also log resolved vulnerabilities. The information produced by vulnerability management is used either to fix the discovered vulnerabilities or quarantine the affected system until they are fixed.
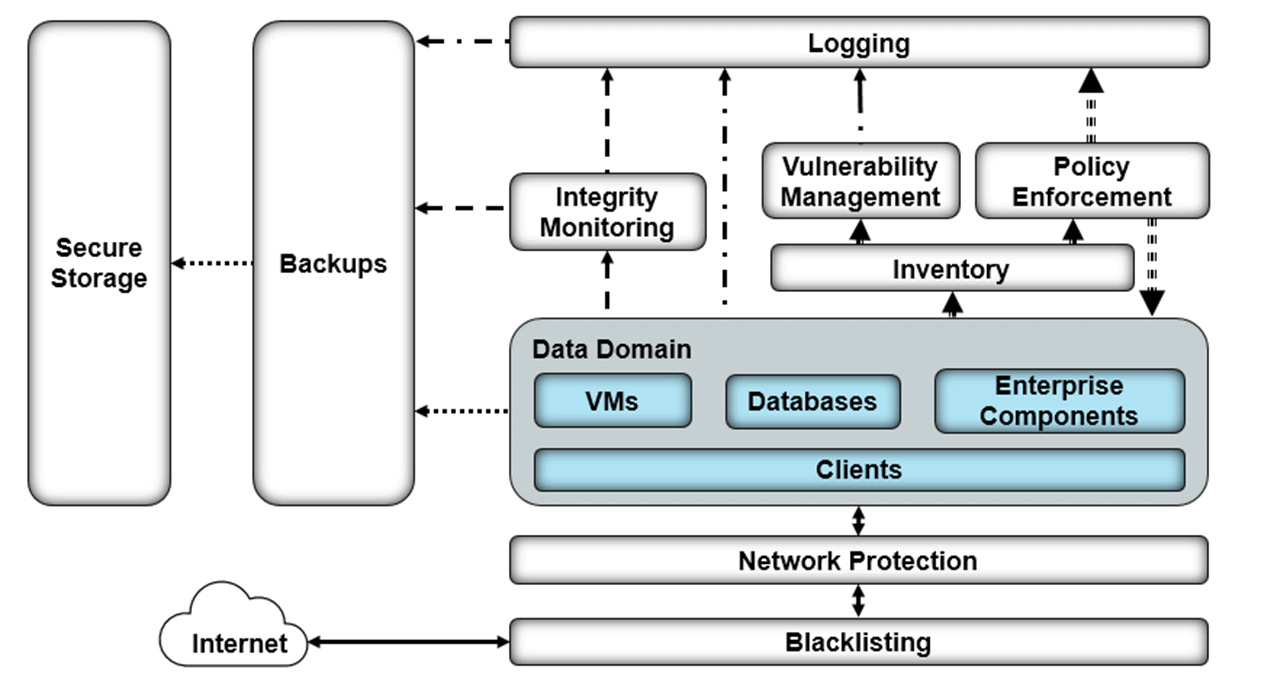
Figure 1: Identify and Protect High-Level Architecture. Source: NIST SP 1800-25 On the other hand, and in parallel with vulnerability management, integrity monitoring provides the ability to test, understand, and measure alterations that occur on files and components within the enterprise. It is important to first establish an integrity baseline for files and systems across the enterprise. A baseline of the system in its optimal state is what is used to establish any drifts from that condition. The value of integrity monitoring becomes clear both during, and after an event. Alerts can be set to notify the security team to act when abnormal changes are detected to a file or system, such as changes made at abnormal times or by users who typically do not make changes to these assets. Furthermore, the information produced by integrity monitoring systems can be used to inform a recovery process; they provide information about what changes happened, when changes began to take place, as well as what programs were involved in the changes. The outcomes of vulnerability management and integrity monitoring are fed into the logging capability. Logging from each enterprise component serves several functions in an architecture that aims to identify and protect assets.
NIST SP 1800-26, Detecting and Responding to Ransomware and Other Destructive Events
The NCCoE, also offers a practice guide to assist organizations about how to quickly detect and respond to data integrity attacks. This incorporates multiple systems working in concert to detect an ongoing data integrity cybersecurity event. Additionally, it provides guidance about how to respond to the detected event. Addressing these functions together enables organizations to have the necessary tools to act during a data integrity attack. Detecting and responding to attacks against data integrity could be done when the following capabilities work together:

- Integrity monitoring
- Event detection
- Vulnerability management
- Reporting capabilities
- Mitigation and containment
Integrity monitoring, in combination with event detection not only function as tools to inform recovery, but also act as early indicators of compromise. Event detection uses these records and its own mechanisms to actively disclose anomalous actions as they happen, and to take appropriate action through other components of the reference architecture.

Figure 2: Detect and Respond High-Level Architecture. Source: NIST SP 1800-26 Logging collects information from event detection and integrity monitoring for use in response functions. Mitigation and containment provide capabilities to stop ongoing attacks, limiting their effect on the system. Forensics/Analytics enables analysis of logs and threat behavior to aid the organization in learning from the event. Reporting provides capabilities for memorializing information for the appropriate parties both during and after an incident. The information gained from these records can be used to inform products that fall in the Identify function of the Cybersecurity Framework to indicate vulnerabilities in the enterprise that need to be remediated.
Benefits of the Practice Guides
Prior to the practice guides, NIST had also released the NIST SP 1800-11 guide, “Recovering from Ransomware and Other Destructive Events.” These practice guides to data integrity can help your organization:
- develop a strategy for identifying, protecting, detecting, responding, and recovering from a data integrity cybersecurity event;
- facilitate comprehensive protection from adverse events, effective detection and response, and smoother recovery from an adverse event both to maintain operations and to ensure the integrity of data critical to supporting business operations and revenue-generating activities; and
- manage enterprise risk.
Benefits of Tripwire Solutions
Tripwire is very proud to be part of the NCCoE project. Companies have considered Tripwire functionality a key component to successfully implementing the NIST Cybersecurity Framework because the controls found in Tripwire solutions provide support for all five functions. The NCCoE used Tripwire IP360 to perform the vulnerability management functions. Tripwire IP360 is a vulnerability scanner and management tool, which can scan a variety of hosts for known vulnerabilities and report on the results. Furthermore, the tool can manage and assign risk levels to these vulnerabilities, allowing security teams to effectively manage vulnerabilities throughout the enterprise. For integrity monitoring, Tripwire Enterprise was used. Tripwire Enterprise is a file integrity monitoring tool that establishes a baseline for integrity activity within the enterprise. This baseline is used in the event of an attack to detect and alert on changes within the enterprise as well as aid recovery should it be necessary. Finally, Tripwire Log Center was used for logging purposes. Tripwire Log Center collected, transformed, and forwarded logs from Tripwire IP360 and Tripwire Enterprise. If you want to learn more about how Tripwire solutions can help your organization implement data integrity functions, contact the experts or ask for a demo.
* The NCCoE is a public-private partnership that brings together industry organizations, government agencies and academic institutions under cooperative research and development agreements to collaborate in the creation of practical cybersecurity solutions that address the needs of specific industries as well as broad, cross-sector technology challenges. NIST does not evaluate commercial products under this project and does not endorse any product or service used.
5 Things Your FIM Solution Should Be Doing for You
Discover the pivotal role of File Integrity Monitoring in maintaining system security and compliance with major standards. Tripwire Enterprise stands out as an advanced solution, offering real-time detection and detailed context for system changes, making it a superior choice for robust cybersecurity.

