
The Ryuk and Sodinokibi ransomware families both contributed to an increase in the ransom amounts demanded by attackers over the past quarter. Coveware found that the average ransom amount demanded by ransomware attacks in Q1 2020 was $111,605. This amount was a third higher than what it had been in the final quarter of the previous year. It was also nearly triple the amount of the quarter's median ransomware payment of $44,021, a value which had not changed drastically from the median payment of $41,179 in Q4 2019.
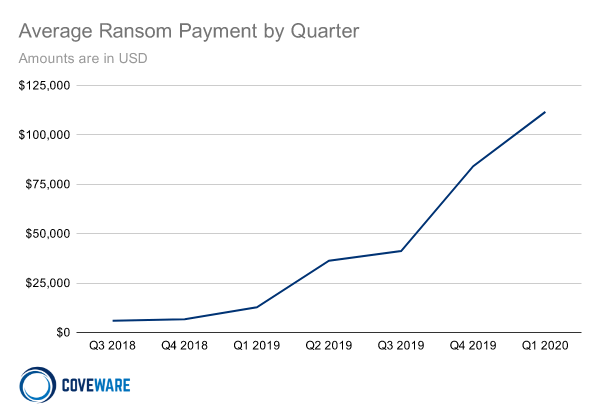
The average ransom payments made to ransomware attackers by quarter (Source: Coveware) In analyzing the reasons behind this increase, Coveware found that the three most popular ransomware families of Phobos, Ryuk and Sodinokibi all played a role. For instance, Phobos was the third most prevalent ransomware family in Q1 2020 with 7.8% of the market share. This threat didn't change its techniques much between Q4 2019 and Q1 2020, as it continued to target small enterprises for which Remote Desktop Protocol (RDP) was open. Even so, its average ransomware payment increased from $12,089 to $15,761. The second most prevalent ransomware with 19.6% of the market share, Ryuk was a different story in that its average ransom demands increased dramatically from $779,856 in Q4 2019 to $1,339,878 the following quarter. This increase occurred despite a decrease in the size of the organizations that the threat targeted in most of its attack campaigns. Sodinokibi had a more complicated story to tell. But that didn't stop the crypto-malware from seizing more than a quarter (26.7%) of the market share and earning its place as the most prevalent family in the quarter. As Coveware described in its research:
Sodinokibi ransom payments were more broadly distributed, representative of their broader victim demographic. A single large organization may have a million dollar ransom demand. Other times Sodinokibi targeted an MSP’s clients and tried to extort each individual end client for $5-$10k.
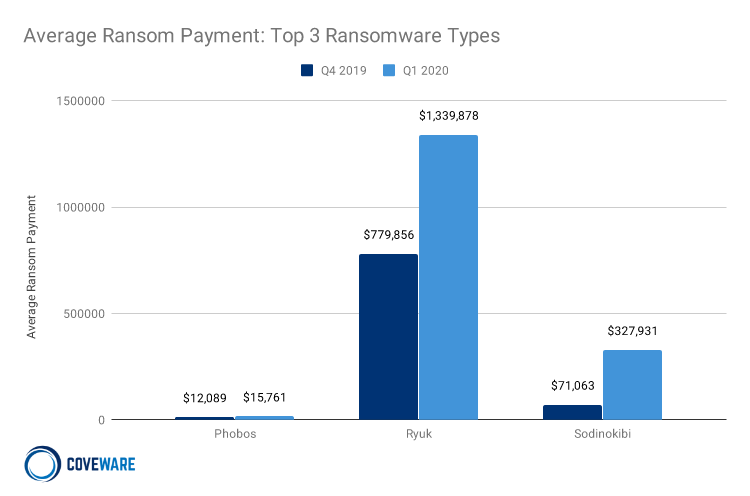
Average Q4 2019 and Q1 2020 ransom payments for Phobos, Ryuk and Sodinokibi (Source: Coveware) The increase in the average ransom amounts demanded by ransomware attackers highlights the need for organizations to defend themselves against a crypto-malware infection. One of the ways they can do this is by working to prevent such an attack from occurring in the first place. This resource is a good place to start.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

